The Autorun.inf worm started off innocently enough, but has evolved to become a recurring pest on a number of USB storage devices. By itself, the worm is harmless, however it is used to load a harmful file onto the system. This article looks at the various methods to get rid of the Autorun.inf worm.
What is Autorun.inf?
Autorun.inf is one of the few worms that ordinarily have a legitimate use; it is the same file that is detected by a computer when new hardware is plugged into the port. The file is usually stored on the peripheral and loaded onto the computer each time.
However, this innocuous file has another insidious side to it as well. In case of malware on the peripheral, most often removable USB drives, these are transferred onto the computer when the file executes. The worm causes files to behave strangely; the most common symptom is when drives cannot be accessed from Computer.
There are a number of ways to get rid of the Autorun.inf worm; the most effective ones are described in detail.
How to Get Rid of the Autorun.inf Worm using the Command-line
In the event that the infection is a particularly tricky one to permanently remove, it is best to use the command line interface to remove it.
First, it is important to disable the autorun feature altogether. After plugging in the device, a notification window appears asking the user for the next action to perform. Click on ‘Cancel’ to dispose of the window.
Then navigate to the command prompt of the computer, either by typing ‘cmd’ in the Run command box, or using the Search function for newer versions of Windows.
Once the black window is open, navigate to the root directory of the USB storage device. For example, if the USB drive is denoted by the letter G, and the main drive is C, then the instruction would look like this:
C:\cd F:
Usually, malware files are hidden or archived which makes them more difficult to spot and remove. Therefore the next step is to change all the file attributes to visible, non-archived, non-system and read-write access:
F:\ attrib –r –a –s –h *.*
(Note: The notation “*.*” means that the command applies to all files with all extensions – essentially all the files on the drive.)
To view all the files on the drive, use the directory command:
F:\dir
The displayed list may have a number of visible infections, like svchost.exe or Ravmon.exe. These files can now be deleted. As mentioned before, to get rid of the Autorun.inf worm permanently, it is important to delete all the malware files on the drive, as the file could be recreated.
Duping the Worm
If a computer is subject to use by numerous users, it can be difficult to protect it from infections from each USB storage device. In that case, rather than rely on an antivirus program, it is simpler to create a folder named “autorun.inf” at the root of the drive. This dupes the worm into thinking the computer has already been infected, and it is does not load on to the system at all. If there are multiple drives, one folder per drive will keep infections at bay.
Some antivirus programs use the same strategy to prevent subsequent infections from occurring, as well. While it is an inelegant solution to the problem, it is effective in getting rid of the Autorun.inf worm.
Using Antivirus Programs
Most antivirus programs are able to detect the Autorun.inf worm when it is scanned, and remove the threat immediately. However, the catch is that the worm is not removed permanently therefore the infection keeps appearing whenever the device is unplugged and re-plugged into the computer. It then becomes a tedious process to manually scan the device each time.
There are a few programs those are able to get rid of them, without recurrence:
- Sophos : The antivirus company has recently discovered that the Autorun.inf file is being dynamically created by another malware known as Conficker. They maintain a blog with their recent findings and developments, making it easier to see that the contents of the security database have been updated accordingly.
- Kaspersky : Kaspersky has a module that runs whenever a USB storage device is plugged into the computer. Only once the program gives the all clear is the computer allowed to explore the device contents.
- AutoRun Eater : Specially designed for removable media, the AutoRun eater program automatically scans every USB storage device for malware. The cure effected is permanent.
- AVG: One of the more popular editions of free antivirus programs, AVG can be used to scan the device and remove the file altogether. It is important to remove all the malware infections that are detected since the other files may recreate Autorun.inf.
There are a number of other software applications, especially designed to target the Autorun.inf file. Most of them are free for home use, and are quite effective also.
Disabling Autorun.inf in Windows
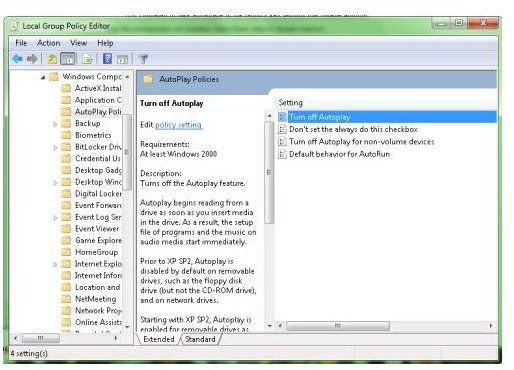
To disable Autorun and Autoplay permanently in Windows, the user needs to edit their Group Policy. This is done using the gpedit.msc system tool, and the steps are as follows:
(NOTE: Modifying the contents of the Windows registry is best left to professionals. Results can sometimes be unpredictable.)
- Click the Start button, and type “gpedit.msc” in the search box. Press Enter.
- A screen to called Local Group Policy Editor opens up. Expand the Computer Configuration folder, then the Administrative Templates and lastly Windows Components, in the left pane.
- Click on Autoplay Policies.
- In the right pane, an option appears, Turn off Autoplay. Double-click to view the settings.
- Click on Enable and exit.
- Restart the computer for the new settings to take effect.
In case of older operating systems, Windows may not have gpedit.msc. The user can turn off autorun functionality using regedit.
- Click the Start button, and type “regedit” in the Run box. Press Enter.
- Locate the following registry entry: HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer\NoDriveTypeAutorun
- Right-click on the entry, and select Modify.
- To disable autorun on all the drives, type 0xFF in the Value Data box.
- Exit the registry editor.
- Restart the computer for the new settings to take effect.
Conclusion
There are a number of methods to get rid of the Autorun.inf worm; some more efficacious than the others. Although Autorun.inf started out as a relatively harmless malware infection, it is now teamed up with other more sinister malware programs. These programs can recreate a deleted Autorun file, and therefore it is imperative to remove the whole infection from the drive.
There is a common misconception that the autorun worm is restricted to just USB storage media; it can also be found on removable optical media like CDs or DVDs. If the optical disc is write-protected, the user either has to throw away the disc, or create a folder on the root directories, as mentioned before.
Although disabling autorun is the always the first step, once the infection has been removed, the user can reactivate the autorun feature.



