If you are looking to keep your information free from prying eyes, or hacking eyes, then one simple and easy way to add an extra layer of protection to your system is by encrypting your database. This user guide will show you how to do just that.
Why Encrypt?
There are a lot of very good reasons why you would want to keep the information in your database secure. Maybe you want to:
- Keep your customer information safe from the prying eyes of your competition. After all, they would steal your customers in a second if they could.
- Keep your employee payroll database safe from the prying eyes of the other employees in order to keep your company from degrading into a hot bed of salary arguments and potential lawsuits.
- To keep the information that you have worked so hard to compile from being changed because you have a file sharing system that plays it fast and loose with access permissions.
- Just want to quell your inherent fear of hackers and one of the million other problems that can happen when your computer and all of its files are open and exposed to the Internet.
The How To’s
The actual steps involved with encrypting your Access database are surprisingly easy. This means that even if you have only basic Access skills and no coding experience, then you can still have your database be safe and sound.
- Open the Access database that you want to secure. You can do this by navigating to the file and double clicking the files icon.
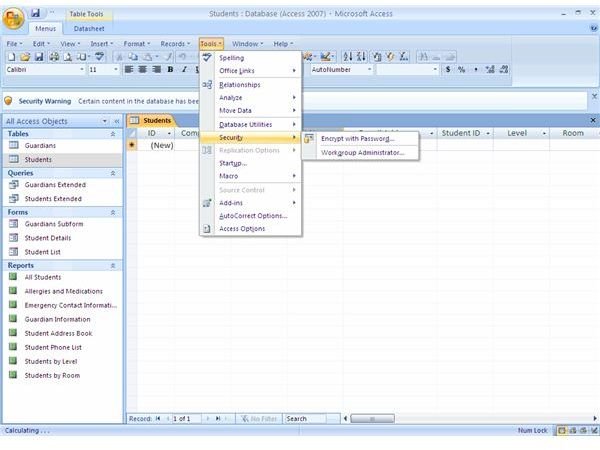
- Click on the word “Tools” to make the tool menu appear on the screen.
- Click on “Security” in the “Tools” menu. This will make your Security Options window open.
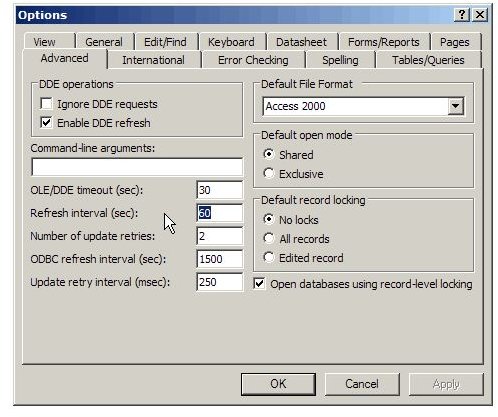
- Depending on your version of Access, you will either see a set of tabs or simply sections of the window. If you have a tab, click on it. If you have a section then just locate it in the window and you should see a button. It will be labeled “Encrypt/Decrypt”.
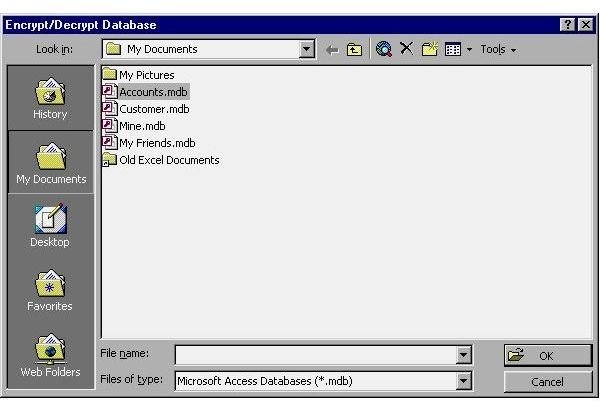
- Under the “Encrypt/Decrypt” section or tab you will see the dialog box for Encryption appear. Now you will have access to a list that you can choose files from that you want to encrypt. Choose those files that you want to modify and then click on “OK”.
- Depending on your version of Access, you may have to name the file. If you choose the same name, the old file will simply be overwritten. The encryption process will now begin.
These directions are designed for Access 2003, but they can be used for 2007 as well – just be aware that there may be some minor location changes.
Images