This is the 2nd article in a series on the Conficker.A and Conficker.B worms. We examine the detection and removal of Conficker using Microsoft’s Malicious Software Removal Tool (MSRT). This how-to details step-by-step obtaining the latest release of the MSRT and using it to remove Conficker.
How To Remove Conficker
In the first article in this series, we discussed protecting a Windows network from the Conficker worm . That was a high-level view. This article details how to remove the worm from your Windows computer if it is infected.
Conficker - also known as Downadup or Kido - can infect any recent version of Windows if the operating system is not patched. Reasons for infection may include, but aren’t limited to: anti-virus software that was out of date or not installed, manually patched systems that did not have Microsoft patch MS08-067, or perhaps Automatic Updates were turned off. (Conficker can turn off Automatic Updates and other services such as Error Reporting Services or the Background Intelligent Transfer Service (BITS) so the patch wouldn’t have been obtained after infection).
Before we remove the Conficker worm, we need to patch any infected systems so that they won’t be reinfected. We may need to manually download and apply the MS08-067 patch. After applying the patch we can proceed to the removal.
Conficker comes in variants including the A, B, and C variant.
Get Microsoft’s Malicious Software Removal Tool
If you have Windows 2000, Windows XP, Windows Server 2003 or Windows Vista, you can use the latest version (January 11, 2005 or later) of Microsoft’s Malicious Software Removal Tool (MSRT). The tool scans for infections by numerous worms and malware (such as Sasser, Blaster, and Conficker) and then removes them. MSRT finishes with a report of infections, with a detailed list of what was scanned for, found infected, not infected, or removed.
First we need to download the latest version of the MSRT. It can be found here: https://www.microsoft.com/security/malwareremove/default.mspx . We can click the “Skip the details and download the tool” link. We want to do this from a patched, uninfected computer. We then copy the downloaded file: windows-kb890830-v2.7.exe to any infected computers, and run the MSRT from those computers (logged in locally to the desktop or via Terminal Services or Remote Desktop).
Running the MSRT
Running the Malicious Software Removal Tool is easy.
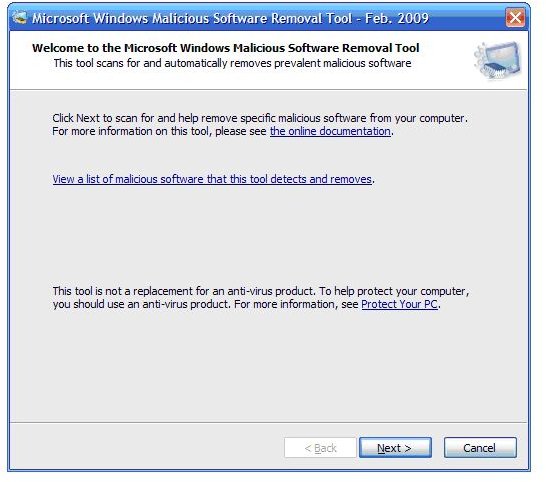
The executable is self extracting. We double-click on it, and follow the prompts.
The welcome page has a list of malware the tool detects and removes, so it’s easy to double-check that the version we’re running will remove Conficker.
Next we’re prompted to choose a type of scan. For Conficker we want to pick the 2nd option: Full scan.
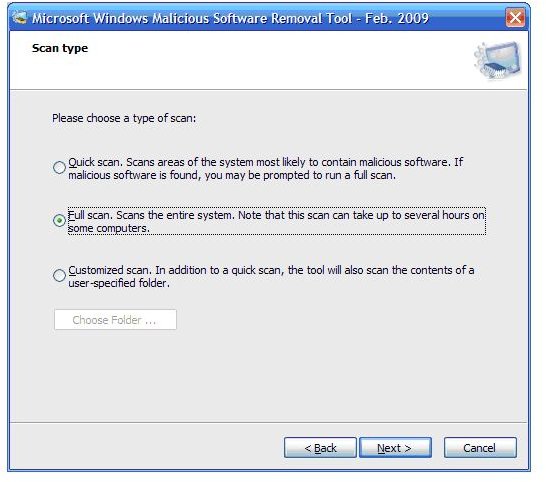
Granted, on a file server with lots of storage, this could take a long time, but we’ve got to do it!
Next we see a typical progress screen, with a progress bar, and a list of what’s currently being scanned, the number of files scanned, files infected, the start time and elapsed time.
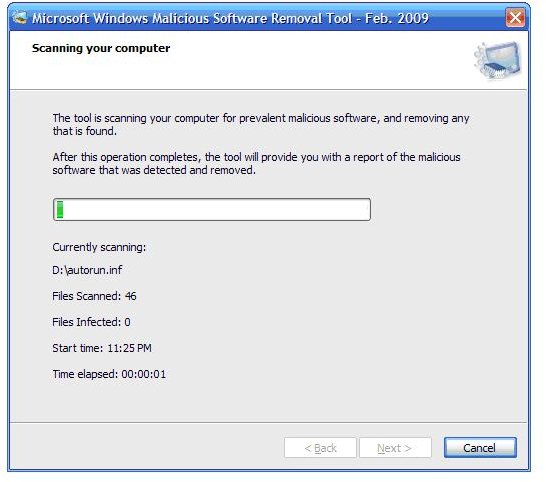
So, it’s easy to know how much work has been done! If the MSRT finds an infection it will attempt to remove it.
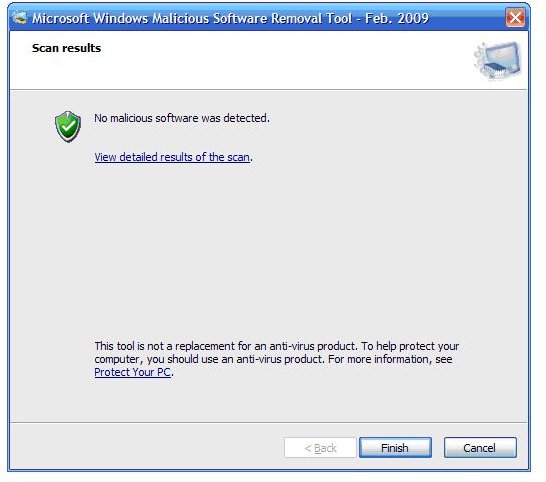
Once complete with the full scan, the scan results are shown, we can view detailed results of the scan,
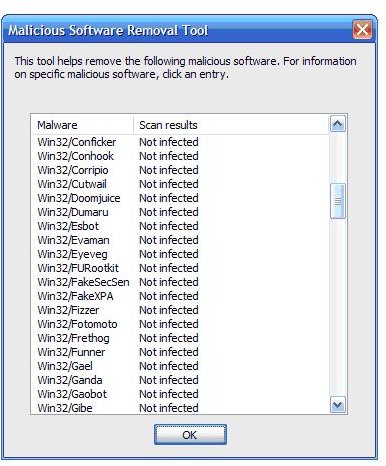
and then click Finish.
Next Steps
Microsoft notes (and I agree) that: “This tool is not a replacement for an anti-virus product. To help protect your computer, you should use an anti-virus product.” If you’re not already running an anti-virus product, you should start doing so ASAP. Bright Hub’s reviews of leading solutions including ESET Smart Security , Norton Internet Security , BitDefender Total Security and McAfee Total Protection Service may help you decide which product is right for you.
You should always have some type of protection on your system. The good news is that at least for the Conficker C variant, infections overall seem to be going down. On the other hand it is notable that Conficker A and B variant infections detected seem to be increasing significantly. Total infections of these two variants detected increased from just under five million in August to almost 6.5 million in December of 2009 according to the Conficker Work Group.
The next article in this series will examine potential changes to firewall settings which will help protect against future worms and malware attacks.
This post is part of the series: Protecting Windows Networks From Worms And Malware
Worms and malware such as the recent Conficker.A and Conficker.B worms are a growing and recurring threat to modern business networks. Constant Internet connectivity means constant vulnerability and exposure, but a few fundamental security strategies can minimize current and future risks.