We all know and agree that the User Account Control (UAC) is annoying in Windows Vista. Some users choose to disable the UAC completely, but we believe this is not a good idea in a security perspective. How can we balance the annoyance and the security?
Introduction
Yes, we know. The shaded screen asks your permission to further execute the program. The delay you experience, even half a second. But have you ever thought that disabling the UAC is saying the bad guys “look, I have disabled the notification so you can drop by in my system and do a shatter attack, and I will not be informed” in most cases? Yes, disabling the UAC makes your system vulnerable to especially shatter attacks, which are essentially bypassing security restrictions by exploiting the currently running processes.
Shaded Screen: Good-bye
There is a reason that Vista shades your screen. What your operating system tries to tell you is: “look, I have paused the execution of the program. I am not sure if this program can run with escalated privileges. I have stopped your system and took you to the secure desktop mode. Do you want me to continue?” Clicking unconsciously on the allow button enables the program to run which may allow an attacker to take control of your system. Vista informs you about this by shading the screen and thus trying to get your attention. There is a way to stop the shading screen but to continue receiving the alerts. This way you will get rid of the annoyance but will not bypass the important notification.
Vista Business, Ultimate and Enterprise: Open up the Local Group Security Editor from the start menu or simply by typing gpedit.msc in the start menu and hitting the Enter key. In the window that is opened, on the left pane, select Windows Settings, Security Settings, Local Policies, Security Options. Then, on the right pane, scroll down to see “User Account Control: Switch to the secure desktop when prompting for elevation”. Double click on this entry and change the setting from “Default” to the “Disabled”. Hit OK and then close the window.
Vista Home Basic and Home Premium: Local Group Security Editor is not present in Home Basic and Home Premium releases. To disable the shaded screen, you have to play with the registry. Open up your registry editor by running regedit (as always, do not forget to make up a copy of your registry before making any change.) Now, on the left pane, select HKEY_LOCAL_MACHINE, SOFTWARE, Microsoft, Windows, CurrentVersion, Policies, System. On the right pane you will see the entry “Prompt on SecureDesktop” with a DWORD value of 0x00000000 (0). Double click on the entry and in the “Edit DWORD (32-bit) Value” window, change the Value Data to 1. Do not change anything else and click OK.
After making the change, you will still receive notifications but your screen will not be shaded.
Run Programs with Elevated Privileges without UAC
If you are using some program all the time and each and every time the program asks for running it with elevated privileges, there’s a workaround. The solution is not a “for all” solution, instead you have to go through each step for each program that you want to run without UAC.
To go on with this solution, you must be a member of the Administrators group. The solution will not work with standard user accounts. The security risk is implicit here: you must not use your computer with an administrator account if you are not making changes to your system, to say, if you are not performing administrative tasks. If you work with an Administrator account all the time, it means that “hey attackers, if you can take control of my system, you take control of the administrator. Do whatever you want as you please.” This is true for both Windows XP and Vista. UNIX-like operating systems (UNIX, Linux, BSD etc.) do not allow you to use the computer with Administrator privileges. In fact, they do not allow you to log in to your computer as root. This approach is –in my opinion- poorly implemented in XP and Vista, because the user that is created with the installation is automatically placed in “Administrator” group. To overcome this situation, always create a regular user and an administrator, and preferably rename the administrator log-in name.
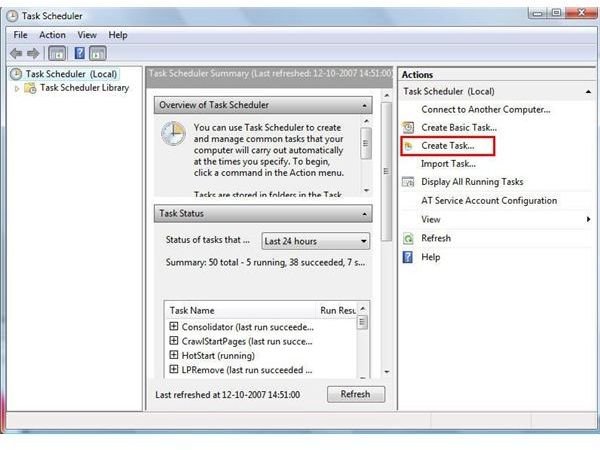
Back to our subject. First open the Task Scheduler program from the Start Menu. Say OK to the UAC. In the right pane in the Task Scheduler, click on “Create Task”. Enter the name of the task (take a note of this name; let’s say high_privilege_task.exe), and do not forget to tick the “Run with the highest privileges” box. This is the trick to bypass the UAC, but we have a little bit more to do. Switch to the Actions tab and enter the name of the program that you want to run with escalated privileges (if necessary, enter the whole patch such as c:\windows\notepad.exe.) The switch to the Settings tab and click the “Allow task to be run on demand” box. By this, we are making the program to run any time we click on its shortcut, rather than running it on scheduled times. Save OK and save everything and close the window.
Now, go to the desktop and right click on an empty place, select New -> Shortcut. In the window, type the shortcut name as
schtasks /run /tn high_privilege_task.exe
Give your shortcut a name and finish.
Now, every time you click and run the program from this shortcut will bypass the User Account Control. However, when the program initializes, you will see a blink of the UAC, just open and close, without your intervention.



