Will Microsoft’s new operating system Windows 7 be more secure than other operating systems? Basic tests were run against the operating system to test the default settings of the OS. Windows 7’s firewall and setup is much like Windows Vista. The performance is totally different.
Protection
No matter what you throw at an operating system, especially Microsoft, other people will find weaknesses. It doesn’t scare me to test new operating systems and give an opinion. It is my opinion that basic tests are often as good as thorough tests. For home users, unless a hacker has ’latched’ on to your ip address and you have virtually no protection in place, you are going to be vulnerable. Now with businesses or corporations, every security measure had better be put into place to protect assets. Businesses are a virtual gold mine to true hackers. So why are basic tests almost as good? It goes without saying that if you are a home user, regardless of your operating system; you better have your firewall on, updates downloaded, anti-malware, anti-virus software, folders only shared to specific usernames only and good surfing habits.
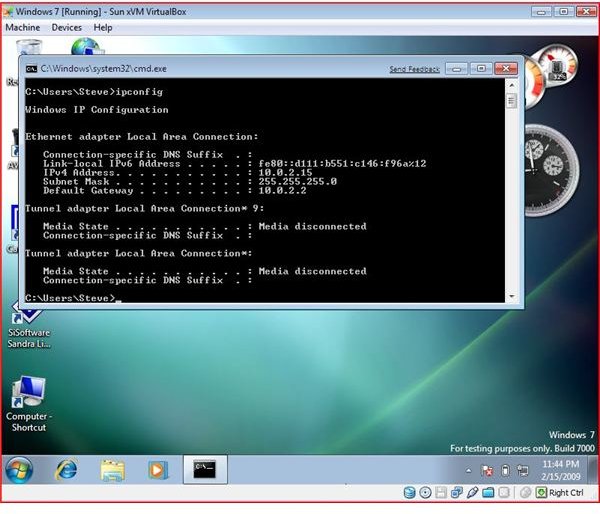
These tests were performed both inside and outside of virtualbox in order to look at a physical computer and a virtual computer. The test results were the same.
Windows 7 and the UAC
The world is jumping on Microsoft about having the UAC in Vista. Now the world is jumping on Microsoft about the control on the UAC in Windows 7. The UAC is a prompt that roughly 90+ percent of users will click “Allow” regardless of the danger behind what is being done. End users of any operating system need to think about what they are allowing when this prompt comes up. So is the UAC a security risk? No and Yes. User education is the key behind any prompt on any program.
Windows 7 Basic Tests
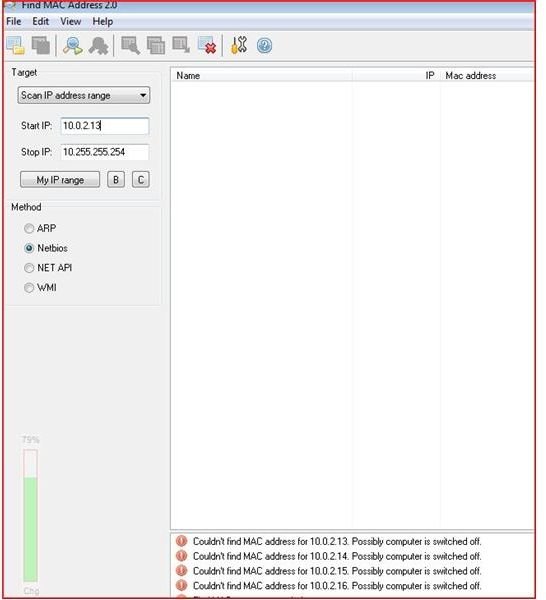
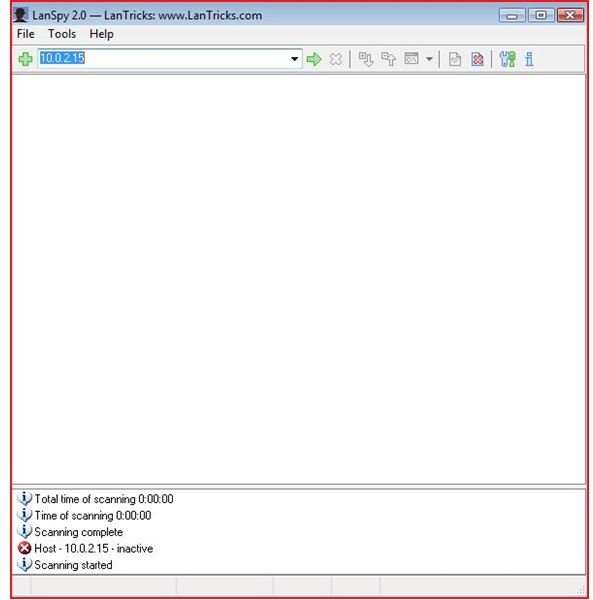
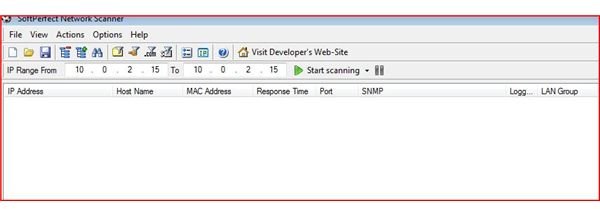
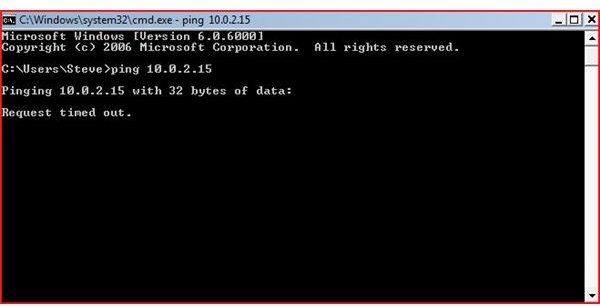
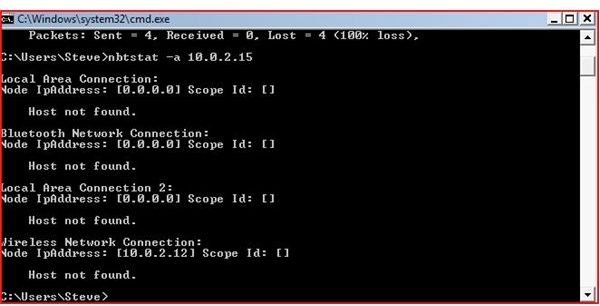
I decided to perform basic testing on the default settings of a Windows 7 installation.
Using a basic ping, netbios path, Find MAC, NETSCAN, and several other basic programs, the operating system was not footprinted and no open ports showed up and no ports appeared to be open.
Remember these are basic tests and these first tests are a positive start for Windows 7. Now of course there will be weaknesses. Someone will also find an obsure file that can take control your computer if certain circumstances allow it. Under most circumstances, if good practices are followed, all operating systems are secure enough for home users as long as good practices are followed.
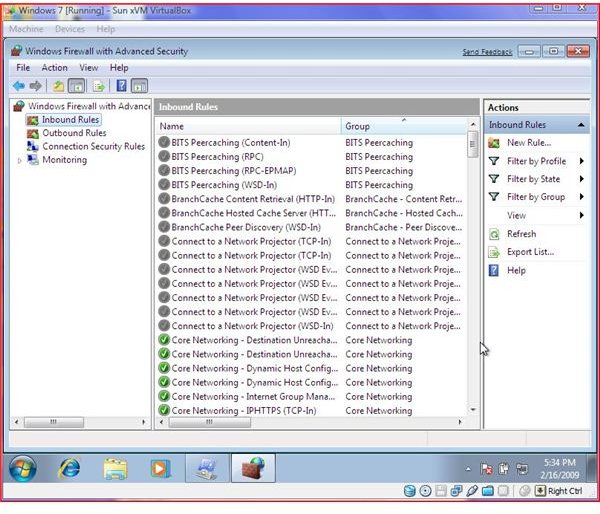
With Windows 7 the Microsoft Windows Vista style firewall is in place.
Basic Tests
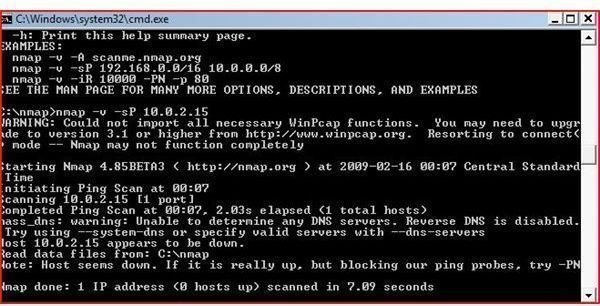
Windows 7 More Complex Test
Initial tests with NMap and several other more complex security programs indicate that Windows 7 is generally secure. Using NMap, the computer did not respond to several “probes”. During these initial tests, NMAP was ran against a Windows XP Professional computer and it was configured with several different switches. The results from the XP vs. 7 were totally different.
While this is only very basic tests, it is again important to remember that no matter what tests are performed at this stage, vulnerabilities will be found. Ultimately, it is up to the end user to configure proper sharing, permissions and to make sure antivirus and anti-malware protection is loaded along with any updates or patches.
Nmap and Windows 7 Firewall
Conclusion
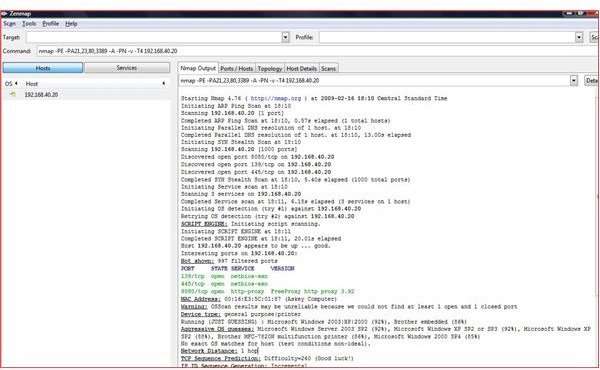
The image above represents Zenmaps run against a Windows XP computer configured to its default settings. When this picture is compared to Windows 7’s test, Windows 7 by default appears to be more secure than Windows XP’s default settings.
Although this is not a hardcore penetration test, these tests conclude that Windows 7 is fairly well protected. As Microsoft learns from its mistakes, they continue to improve on their operating systems. When Microsoft announced their security initiative several years ago, they have gotten better at releasing fixes and educating end users. Windows 7’s performance with its first test on security appears to be a robust operating system.