Have you ever wished you understood more about computer security? That you had a better understanding of what each term meant? Do you want to have a clearer idea about how these things are related? If that’s the case, this article is for you. Read on to find out more about this topic.
Introduction
Computer security has been around since the advent of PCs, computers that were built for the average Joe, so that everyone could make use of this miraculous technology. Naturally, back then everything was simpler and the threats much more limited. However, as more and more people joined the club of computer users, and as interaction among computers became easier and faster, everything changed. Malicious programs became commonplace and those corrupt individuals who abused technology became more adept in finding ways to exploit computers and create problems for everyone. Their motivation is either monetary benefit or, more often, simply showing off. Nowadays things are so complex in this field that there is serious research (conducted by serious universities), so as to find ways to provide security to computers, whether they are independent or part of a large network. As you probably don’t have the time to attend a whole course on this topic, we offer this distillation of it to you, so that you become more familiar with the various terms, their relationships and the software you need to keep your digital assets safe.
Definitions - PC-Related
First, let’s start with something simple that you probably have used already: Backup. According to John Daintith in A Dictionary of Computing (2004 edition), backup is “a resource that is, or can be used as, a substitute when a primary resource fails or when a file has been corrupted. The word is also used as a verb, to back up, i.e. to make a copy in anticipation of future failure or corruption.” So, basically it is when you keep a copy of your files somewhere outside your computer, usually a DVD or an external hard drive. You can do that either manually or, preferably, using a backup or synchronization program, such as AlwaySync .
Another important term, which is used very frequently in computer security software is Encryption. According to the Gale Encyclopedia of E-Commerce (2002 edition), “encryption is the scrambling of sensitive information, such as credit card numbers, personal information, legal documents, confidential records and even personal communications, in such a way that only authorized persons or organizations are able to decipher it… Encryption is the fruit of cryptography, the study of codes and ciphers for the guarding of secret information.” In other words, this is when you turn the contents of a file (or a whole hard disk for that matter) into gibberish, which can only be turned back to the original information using a certain password/passphrase, which is called the “key”.
Steganography is a bit more esoteric, but it’s something that’s used a lot today (if you haven’t heard about it, that’s a sign that it’s working well). Deriving from the Greek στεγανός & γραφή (“covered writing”), it “is the secret transmission of a message. It is distinct from encryption, because the goal of encryption is to make a message difficult to read while the goal of steganography is to make a message altogether invisible. A steganographic message may also be encrypted as an extra barrier to interception, but need not be. Steganography has the advantage that even a talented code-cracker cannot decipher a message without knowing it is there.” (Encyclopedia of Espionage, Intelligence, and Security, 2004, article by Larry Gilman). Usually steganography involves images or videos, although it can be applied to any file type, given that it’s large enough for your sensitive data to fit in it.
All of these terms relate to independent PCs mainly and have to do with basic computer security. In the following section we’ll look into network-related security, something which is more essential nowadays.
Definition - Network-Related
When a computer is connected to a network, it’s a whole different game, as the security threats increase exponentially. Usually network connectivity means having access to the Internet, as it is quite rare today to find a computer that is connected with other computers, without also being part of a larger group.
Although you’ve probably heard and used the term Internet, it’s good to define it here properly and provide some background information on it. The Internet is a network of computers linking the United States with the rest of the world. Originally developed as a way for U.S. research scientists to communicate with each other, by the mid 1990s the Internet had become a popular form of telecommunication for personal computer users. West’s Encyclopedia of American Law (2005 edition) provides a quite good definition on this term: “The Internet, popularly called the Net, was created in 1969 for the U.S. defense department. Funding from the Advanced Research Projects Agency (ARPA) allowed researchers to experiment with methods for computers to communicate with each other. Their creation, the Advanced Research Projects Agency Network (ARPANET), originally linked only four separate computer sites at U.S. universities and research institutes, where it was used primarily by scientists.” So, it is the means through which all your emails and webpages travel and are stored, every time you use your browser or your email program. Also, as it is something global, the Internet provides a user with access to computers all over the world.
Another important term is that of Phishing (which is different to fishing). Encyclopedia.com defines it as “a term used to describe e-mail scams that attempt to trick consumers into disclosing personal and/or financial information. The e-mail messages appear to be from legitimate sources, such as banks, credit card issuers, or well-known Internet sites (such as America Online, Paypal, and eBay). The content of the messages varies, but often they tell the consumer that he needs to update personal information or that there is a problem with the consumer’s account. The messages usually contain links to fake Web sites. When the user clicks the link, they are taken to Web sites that look official, and may even include images from the legitimate Web sites. These fake Web sites often instruct the unsuspecting user to enter credit card numbers, social security numbers, bank personal identification numbers (PINs), and other valuable information. Once the user enters that information, the violators use it or sell it.” In other words, whenever someone tries to get personal info from you, without having any authority to do so, they are performing phishing. Remember that banks, online accounts (such as Alertpay) and any self-respecting organization will not contact you to ask you what your password is, for “verification purposes” or any other seemingly legit reason. A scammer masquarading as an organization might do so though, and they may go into great lengths to accomplish their task.
When dealing with sensitive information online, a website often employs a security sockets layer, to make sure that it remains safe. “Security Sockets Layer (SSL)”, according to the Gale Encyclopedia of E-Commerce (2002 edition), is “a public-key encryption scheme widely used in client-to-server applications, was developed by Netscape and was supported by both Netscape and Microsoft browsers.” You can spot when SSL is used as it reflects on the URL of the web page viewed, which instead of starting with https:// it starts with https://, plus it is usually a bit slower than a non-secure web page (because of the encryption/decryption that takes place).
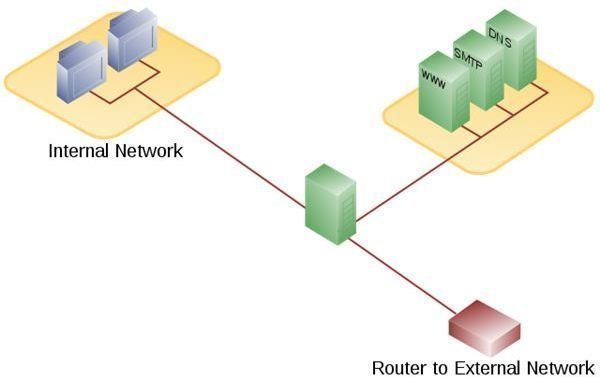
F****irewall is another netword-related term. According to the Encyclopedia of Small Business (2007 edition), the term refers to “a computer security device that is situated between a small business’s internal network and the Internet. It can work at either the software or the hardware level to prevent unwanted outside access to the company’s computer system.” Firewalls can pinpoint potential intruders and block them, though they can also stop outbound Internet traffic as well (e.g. access to adult websites or anonymizers).
Malicious Software and Software Solutions to Them

Malicious software, programs developed with malicious intent (such as viruses), are usually referred to with the generic term Malware (encyclopedia.com). Malware is usually in one of the following main categories: a virus, a trojan or spyware.
According to encyclopedia.com “the term ‘virus’ is often used generically to identify any harmful migrating computer program. However, more strictly defined, a ‘worm’ is a program that travels from one computer to another, usually over a network, but does not attach itself to the operating system of the computer it ‘infects.’ It replicates itself until the host computer runs out of memory or disk space. A ‘virus’ insidiously attaches itself to the operating system of any computer it enters and can infect any other computer that uses files from the infected computer.” These are very common malware and can often cause significant problems, such as data loss, resources shortage and even a complete system breakdown. Moreover, there are new viruses spawning every day.
A ‘Trojan horse’ (or just Trojan), according to the same source, “is a piece of computer software that acts like it has a benign purpose, but is actually performing an ulterior malicious command, such as erasing files.” John Daintith in the Dictionary of Computing (2004 edition) defines this as an “apparently innocent program designed to circumvent the security features of a system. The usual method of introducing a Trojan horse is by donating a program, or part of a program, to a user of the system whose security is to be breached. The donated code will ostensibly perform a useful function; the recipient will be unaware that the code has other effects, such as writing a copy of his or her username and password into a file whose existence is known only to the donor, and from which the donor will subsequently collect whatever data has been written.” Trojans are somewhat sneakier and often pass unnoticed for a while, since their effects don’t cause any vital changes to the system.
According to the Encyclopedia.com, “Spyware is a term used to describe a program that is put on a computer without the user’s permission, and usually without the user’s knowledge. A spyware program runs in the background and keeps track of the programs the user runs and the Web sites the user visits. Some spyware tracks the user’s keystrokes and extracts passwords and other information as they type. It then uses the information gathered to display certain advertisements or forces the user’s browser to display certain Web sites or search results. Most spyware is written for the Windows operating system.” These are less harmful than the other types of malware, but can be a great nuisance as they cause your computer to be targeted by many advertisements, compromising your productivity.
To tackle all these security threats, you need to have an anti-malware program or a Security Suite. The latter, according to the PC Magazine Encyclopedia, is “a collection of software utilities that protect a user’s computer from viruses and other malware. Managed by a single control panel interface that displays all the functions, antivirus and firewall are typically the primary elements. Other functions include antispam, parental controls, Web site authentication, password storage and protection against identity theft. Backup and computer tune-up may also be part of the collection.” In other words, a security suite is a bunch of security programs put together in a complete package, such as the Outpost Internet Security Suite software .
Other Computer Security Topics

Most likely you’ve heard of the term Hacking and hacker. Carey Nachenberd in the Computer Sciences encyclopedia (2002 edition) clarifies this topic quite well. “For years, ‘hacker’ was a positive term that described computer enthusiasts who had a zeal for computer programming. Those who hacked took pride in their ability to write computer programs that stretched the capabilities of computer systems and find clever solutions to seemingly impossible problems. Although many computer enthusiasts still ascribe to this definition, the everyday usage of the word has changed significantly. Today, ‘hacking’ generally refers to individuals who break into computer systems or use their programming skills or expert knowledge to act maliciously.” So if someone breaks into your computer (probably over the Internet) or sends you a malicious email that will create a mess in your system, you are probably a victim of hacking.
Another commonly used term is Spam, referring to “unsolicited e-mail messages that usually contain an advertisement for some product or service, such as mortgage loans, pornography, or prescription drugs… Spam messages, according to a May 2008 statistic, account for more than 80 percent of e-mail.” (encyclopedia.com, Computer Sciences - 2002) This is not something dangerous, but it is definitely undesirable and can cause significant waste of resources. Any serious computer security solution aims to keep spam at bay, although this is still quite a challenging task.
Final Words
These definitions are a good start to getting to know the computer security field. It may be overwhelming at first, but once you gain some experience in the topic, everything will become more manageable. Check out one of the security programs mentioned and read its literature, or join a computer security forum, to gain a wider pespective of the subject. Gradually you will discover that it’s not all that difficult and that with some proactive steps, you can keep your digital assets safe and sound.
References
1. Sheila Robinson, June 2010. “Cryptography or Encryption – Is there a Difference? ”
2. A Dictionary of Computing, 2004: https://www.encyclopedia.com/topic/backup.aspx#2
3. Gale Encyclopedia of E-Commerce, 2002: www.encyclopedia.com/topic/Encryption.aspx
4. Home page of AlwaySync software: www.alwaysync.com
5. West’s Encyclopedia of American Law, 2005: www.encyclopedia.com/topic/the _Internet.aspx
6. Computer Sciences, 2002: www.encyclopedia.com/topic/Hacking.aspx
7. https://www.encyclopedia.com/topic/Computer _Security.aspx
8. Encyclopedia of Small Business, 2007: https://www.encyclopedia.com/topic/firewall.aspx
9. https://www.encyclopedia.com/topic/computer _virus.aspx#5-1O11:virus-full
10. https://www.pcmag.com/encyclopedia _term/0,2542,t=security+suite&i=61437,00.asp
Images’ sources:www.computersecuritytopics.com, https://commons.wikimedia.org and https://cce.cpcc.edu
All websites were last accessed in May 2011.