Free software and free communication go hand in hand in the minds of many cypherpunks. Find out what free software exists to encrypt and secure your e-mails, instant messages, and storage devices from prying eyes.
UNIX-like Systems and Encryption
UNIX-like systems, particularly GNU/Linux and the BSDs, have a long standing history with free and open source software. Since many of the mathematicians and programmers behind today’s encryption methods support the open source software movement, a lot of the business and government level encryption relied on today has been released in some form or another for free on UNIX-like systems. Some of the software, such as Phil Zimmermann’s Pretty Good Privacy (PGP), the most trusted implementation of public key cryptography, was actually released as free software before becoming a commercially supported product. Additionally, open source advocates are quick to rewrite any revolutionary or extraordinarily useful software and release the code as a free and open source product. The best part is that the community made, open source implementation, typically ends up exceeding the feature set or outperforming the original product. Let’s take a look at a few free and open source encryption options for UNIX-like systems.
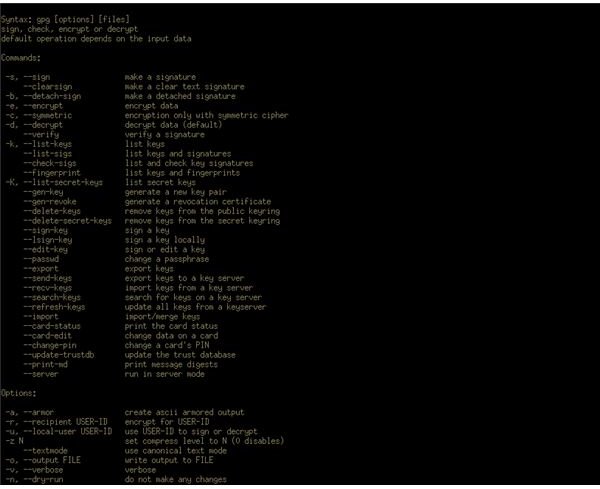
GNU Privacy Guard (GnuPG)
The history of GnuPG is highly intertwined with that of PGP, one of the most popular implementations of encryption software trusted by business, governments, and individuals around the world. PGP, originally released as free software, was later picked up and turned into a commercial product. Today, PGP is owned by computer security giant Symantec who provides enterprise application and server support for a number of products that PGP is implemented in. As PGP developed and was converted into commercial software, the cypherpunks, what the libertarian mathematicians fighting for encryption rights called themselves at the time, saw the need to create an open standard that could freely implement Phil Zimmermann’s PGP methods, in fact the movement for the standard was largely led by Zimmermann. Eventually, the OpenPGP standard was finalized and implemented by the GNU free software project.
GnuPG is freely available for any POSIX-compliant operating system, meaning almost any UNIX-like system out there. The methods use public key cryptography so users need to create a private and public key as well as manage a keyring of individuals they want to send messages to. Messages are encrypted using the individual’s public key, then decrypted using their protected private key. Although used primarily for communication, this public key cryptography method can be used to encrypt any form of data.
TrueCrypt
TrueCrypt is an application that supports On The Fly Encryption (OTFE), meaning that the encryption works transparently
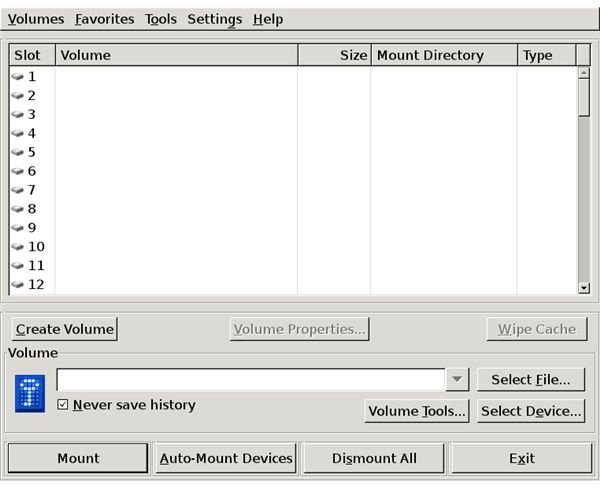
once the access key is enter. With TrueCrypt, users can create encrypted volumes from actual, physical volumes or create a virtual volume using a file on their hard disk. This is useful for hiding volumes from prying eyes. Additionally, TrueCrypt is capable of nesting one volume within another, allowing a compromised user to provide an encryption key for the outer volume, leaving the nested, hidden volume safe. This method of protection is called plausible deniability and is used by journalists, law enforcement, and dissidents in tumultuous regions. TrueCrypt is a cross-platform application, but not all UNIX-like systems have a port of the software yet.
Full Disk Encryption
Full disk encryption can be used to secure entire disks instead of single communication instances, files, or virtual drives. Depending on the UNIX-like system, full disk encryption is implemented in different ways. Under GNU/Linux, Linux Universal Key Setup (LUKS) and dm-crypt are typically used in conjunction with the Logical Volume Manager (LVM) to provide a seamless and expandable full disk setup. Linux also supports loop-AES, a full disk encryption method using the system’s loopback device to provide transparent encryption. OpenBSD on the other hand uses Cryptographic Device Driver (CGD) for full disk encryption and FreeBSD has either GBDE or GELI as an option, both implementing the method in different ways. Other implementations include DiskCryptor and TrueCrypt.
Instant Messaging

There are a number of free instant messaging applications freely available on UNIX-like systems that support varied types of encryption. The libraries used by Bitlbee, Finch, Pidgin, and other free and open source IM clients provide Off-the-Record (OTR) encryption support. OTR is an encryption method designed to not only seamlessly encrypt instant messaging conversations, but to also provide participation deniability. The idea is to create a series of encrypted hand-offs and handshakes that change often enough that the participants and the event cannot be properly identified, all while maintaining the confidentiality of the conversation.
Encryption Libraries
Many of the free encryption implementations available for UNIX-like operating systems use a number of free and open source libraries that make development easier and more efficient. Libgcrypt, maintained by the makers of GnuPG, provides access to the GnuPG implementation of PGP for outside applications. Additional programming libraries provide code for support of certificates and certificate management as well as the up and coming libotr library which provides implementations of Off-the-Record (OTR) encryption invaluable code. These libraries are made available under different programming languages by varied sources and provide an easy way for anyone to begin implementing strong encryption into their applications.
Resources
ForensicsWiki - Full Disk Encryption
Screenshots by the author, except contact window taken from Pidgin.im .