This penetration testing distribution is meant for anyone in the information security field. It comes with a mass of tools that can be used for data gathering, forensics, penetration testing, and remote exploitation.
Overview
The BackTrack Project is funded by Offensive Security , a professional training service for information security specialists in a wide range of industries. The distribution itself is on its fourth release and is aimed to be a one-stop shop for every security tool on the market. As the distribution has gained notoriety, it has seen over four million downloads of its latest version. While BackTrack is aimed at being used as a live distribution either from a USB or DVD medium, it can be installed as a computer’s primary operating system. Although Ubuntu -derived, it uses KDE by default, unlike Ubuntu’s adoption of the GNOME desktop environment.
Usability
Since BackTrack uses the KDE environment by default, the interface is intuitive, graphical, and extraordinarily easy to set up and use. There are a number of applications already installed that make it easily configurable on just about any type of network, allowing you to add Windows file or printer shares using Samba or even connect easily to some of the more advanced wireless networks since the system comes with Wicd as the network manager. Wine also comes pre-bundled with BackTrack 4, allowing you to run Windows applications right out of the box. Along with the basic KDE tool set and application suite, BackTrack has a variety of applications for both penetration testing purposes and user accommodation.
Applications
For Web browsing, BackTrack includes Konqueror and Firefox along with Lynx, the popular text-only Web browser. Other
Internet applications include the XChat graphical IRC client and Liferea for RSS news feed reading. Kopete is the default instant messenger, but since Backtrack uses the Synaptic Package Manager, you can easily replace it with the more popular Gaim or Pidgin clients if need be. Most uses of BackTrack do not include chatting however, so this function will most likely not be an issue for you. BackTrack also comes with a number of Internet services including HTTP, MySQL, SSH, and VNC servers for the quick and easy implementation of network services when needed. Where BackTrack really begins to make an impression though is when you begin to look at the wide and varied tool set that the developers have decided to include.
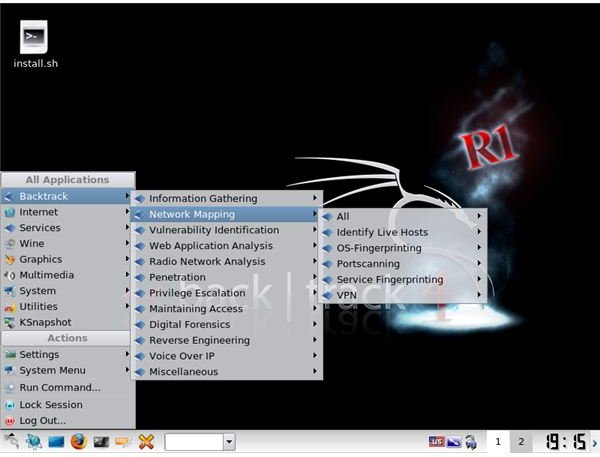
Tools
Backtrack comes with hundreds of tools, including both command line and graphical versions from a variety of assessment and analysis projects. The main tool category is composed of twelve sub-categories with many of the options overlapping. However, despite the amount of overlap, BackTrack comes with a few hundred security tools, enough to keep anyone chock full of information regarding the networks or systems they are currently using.
Wireless
By far the most popular use of BackTrack is for cracking wireless network’s WEP keys on the fly. The current release comes with many
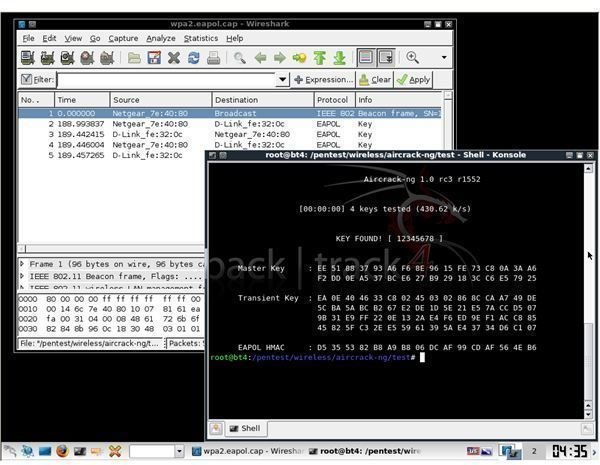
of the patched drivers that support packet injection, enabling users to inject ARP packets and speed up the cracking process. Popular programs such as aircrack-ng and Kismet are included, but BackTrack comes with close to one hundred wireless auditing tools, including Bluetooth and RFID tools. The list of radio tools is above and beyond what most people would ever need to use, but provides a lot of tinkering room for the curious. This tends to be the theme for much of BackTrack’s tools however, above and beyond to encompass any tool set a user might wish to play with.
Exploitation
Another popular use for BackTrack is for the delivering of exploitation payloads through penetration frameworks such as Metasploit or FastTrack. This is where BackTrack becomes truly useful for security researchers and hackers all along the slide of the ethical spectrum. With a massive exploitation database and a number of online resources for expanding that database, BackTrack comes with all of the necessary tools to practically point-and-click your way into a system. Once inside, BackTrack goes further and has over one-hundred tools for privilege escalation, access tunneling, and digital forensics. If most of the tools were not console-based, it would certainly run down the system to use too many of them at once. In any case though, BackTrack is packed to the gills when it comes to exploitation.
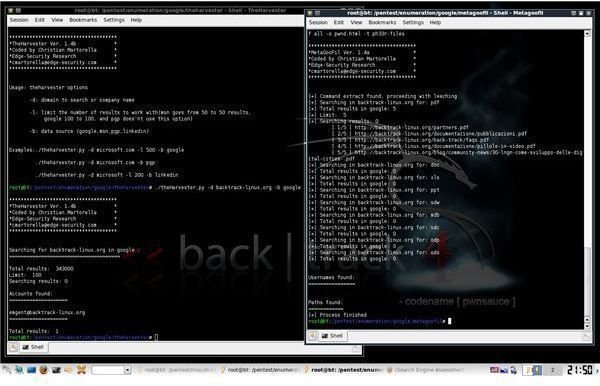
Information Gathering
BackTrack also shines when it comes to the number of tools available for information gathering and network mapping. While sporting some of the most valuable mapping and organizational tools, such as Maltego or Dradis, BackTrack also comes with a number of search engine and data harvesting tools for developing a large database on any target. While including the basic network mapping utilities such as Hping3, Nmap, and Unicornscan, it goes above and beyond in providing another dozen options for a range of uses from service and OS fingerprinting to VPN scanning. Furthermore, Backtrack includes a number of Cisco auditing tools along with OpenVas, the free GPL fork of the popular Nessus vulnerability scanner.
Community
A Linux distribution is defined by its community and user base. These are the people that maintain the forums and wikis that help new users figure out what is different about the way this distribution does things. These are the people that populate the IRC channel twenty-four hours a day to help new users get settled with a system. Many members of the BackTrack community use BackTrack as a secondary operating system and tool in their day-to-day work. Others are simply kids looking to become hackers because of the romantic way the hacker has been displayed in popular culture. This dichotomy has caused the community to be a little pompous, but rightfully so. The leaders of the BackTrack community have spent a lot of time to become security veterans and are not there to give instructional seminars on how to use the most basic of tools. In the past, BackTrack developers shut down the forums for the very reason that they were overgrown and below the standard that they were looking for. The community does not tolerate someone who is not willing to take the time to read up on and discover how to properly use the operating system themselves.
Usage
As a recovery or penetration environment, BackTrack is an excellent operating system. BackTrack overshadows any other distribution of its type since it simply eliminates the competition with its wide tool base and huge user community. With that being said, BackTrack seems like it would be too much for someone to have installed as their main operating system. Since even a veteran security researcher would only use a fraction of these tools, it seems like quite a bit of overkill, unless you are simply experimenting and learning, to have BackTrack as your system’s primary OS. A slimmed down version of Kubuntu or even another system like Arch would be best for someone looking to run a fast and responsive, day-to-day Linux environment. BackTrack should be used as a tool, a swiss-army knife to pull out when needed.
Conclusion
The BackTrack project provides a user with all of the tools they need to gather information on a network, exploit a system vulnerability, and then escalate and maintain their access to the network. It provides an easy to use, well organized graphical interface that just about anyone could figure out. Along with that, BackTrack provides all of the necessities for running a system, including services, even if it is only from a USB pen drive or DVD. The project itself comes in a variety of languages, making it extraordinarily accessible. This all adds up to make BackTrack, by far, the finest security-focused Linux distribution out there today.



