Anyone aspiring to work as a Linux administrator must master working with Linux permissions. Even if you’re not interested in administrative work, you might want to learn the basics which will allow you to share your computer with others while protecting your data and the system.
Why Learn to Work With Linux Permissions?
When learning how to work with Linux permissions, it’s imperative to keep in mind that almost everything under UNIX or a UNIX-like operating system such as the various distributions, also known as distros, is a file. Network interfaces, however, are not files. Each file on the system carries a set of permissions; this is the basis of the security of these systems that were designed to serve multiple users and allow multiple processes to take place while maintaining stability. The modification of Linux permissions is the principle way of controlling access to files, directories, and even programs on a system. You can give or restrict access to a single user or a group of users for a single file, directory, or program. The reasons why you might want to do this should be obvious. In the business world, the accounting department of a company will need access to accounts receivable/payable data and to certain programs for working with electronic spreadsheets. However, executives might not want the sales department to have access to such data or programs used by accounting. This concept could even be applied to the home if a family shares a computer. Mom and dad could be the root users and control access to certain files and programs for their children and also for friends who might want to use the computer while visiting.
Let’s Begin With Linux File Permissions
Even if you’re on a distro designed for a single user who works in a Graphical User Interface (GUI) as root all of the time such as Puppy, you can still exit to a prompt and practice these commands. Simply proceed as though you were going to shut down but choose the option to exit to a prompt which will take you automatically to a command line as root where you can create fictitious users and practice files. If you’re on a system like Fedora, Debian, or Mandriva, your experience will be a little different and closer to the work of a Linux or UNIX administrator in the real world. Every file has an owner, the user who created it is the initial owner (ownership can be changed). It also carries Linux permissions for being read, edited (written to), or executed by the owner, a group of users, and others. A user who is neither the owner nor a member of the group to which the owner belongs, falls into the “others” category. These three categories cover everyone, even guests on the system.
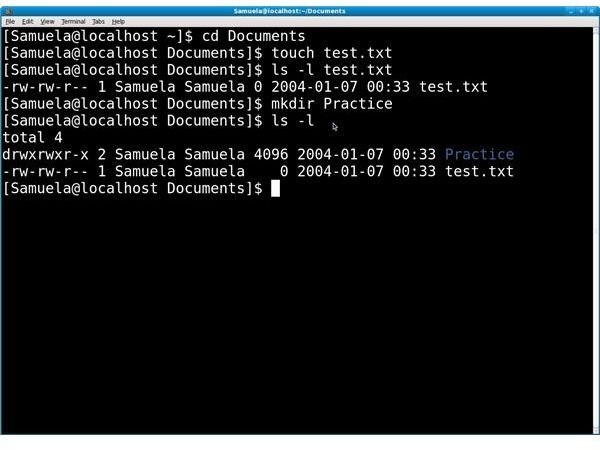
Remember that root, commonly referred to as the super user, has all permissions on all files, directories, and programs all of the time; root is the master user. Now is a good time to open a terminal; it could be called a console on your system, become root (or open a terminal as root) and create a practice file in whatever directory you want. You can use the simple “touch” command to create the file. If you want to create a directory, you can use “mkdir.” Omit the quote marks and type only the command between them. You can then immediately find out the default Linux permissions by typing “ls -l” plus the name of the file. To get the report on a directory, type “ls -l” and press enter. In the screen shot below you can see I’ve created a practice file called “test.txt,” you can also see the Linux permissions report I generated for it. Likewise, I created a directory called “Practice” on which I also generated a Linux permissions report.
The report for “test.txt” shows: -rw-rw-r– 1 Samuela Samuela 0 2004-01-07 00:33 test.txt. The letters r, w, and x stand for read, write, and execute respectively. There are three types of users on which the system is reporting: the owner, members of the group, and others. The report goes in that order. So, we see that the owner has read and write Linux file permissions. The group also has read and write privileges. Finally, others can only read the file. Why is there no information about who can execute the file? Because there’s nothing to execute. It’s not a program or even a script; it’s just an empty file. The number “1” indicates the number of links to the file, and we then see that Samuela is the owner and name of the group. The file size is “0.” The rest is self-explanatory; you’re looking at the date, time and, name of the file. Disregard the date, I hadn’t set it. The actual date of the file is March 16, 2010.
The output for the directory (Practice) is just a little different. We see a “d” in front of the permissions. The “d” lets you know that you’re looking at a directory, not a file. A directory holds files. The letter “x” also shows up because every user is allowed execute permissions. When speaking of a directory, this simply means that you can list the contents of it. To execute a file that is a program or script is to actually run it.
Changing Linux File Permissions
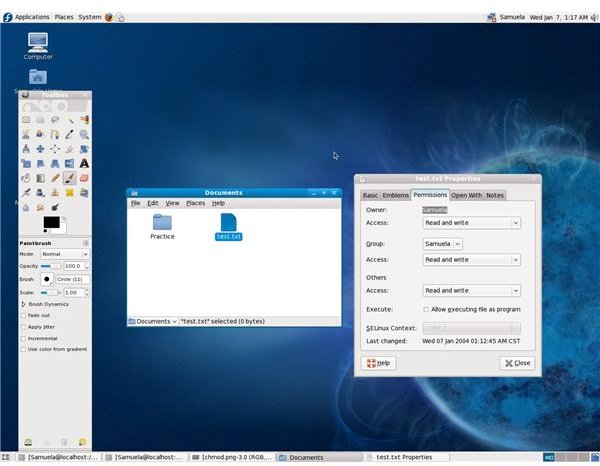
Now let’s say that the Linux permissions for the file “test.txt” need to be changed to allow users in the “others” “group” to write/edit it. This can be done by using the “chmod” command. In the screen shots below you can see that I’ve typed “chmod 666 test.txt” and then hit enter to report on the file by typing “ls -l test.txt” which now shows that users in “others” have Linux permissions to write. You can also see these settings in a GUI by right clicking on a file, selecting “Properties,” and then choosing the permissions tab.
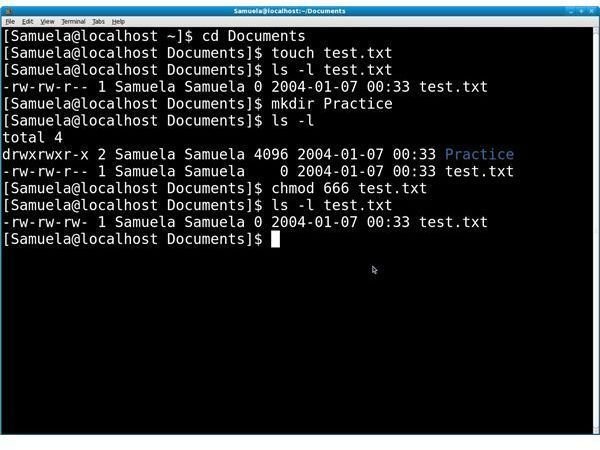
Changing Linux file permissions requires some knowledge of how to work with the mnemonic forms of the chmod command or how to represent authorizations using base-8 values. I’ll cover the basics of octal values since they are what most people prefer. The number “4” gives read permissions or “r”. The number “2” indicates the privilege to write a file or “w,” and “1” is used to give execute permission or “x.” These are used with the “chmod” command to change authorizations. For example, if a file has the permissions “-rw-rw-rw-,” the equivalent numeric code is “666.” Four, or “r” for read plus two or “w” for write equals six for the owner. We repeat this for the group and “others” for a total of 666. If you understand these codes, you can view the numbers and know what Linux permissions a file has. If you wanted to take all permissions away from “others” for “test.txt,” you would enter, “chmod 660 test.txt.”
Other Commands Used For Security and Authorizations
Security under UNIX or a UNIX-based system requires knowledge of how to work with other commands as well such as the “chfn” (change finger), “suid” (set user ID), and “sgid” (set group ID). These can compromise security so they should only be used by someone who really understands what he’s doing. Acquiring a solid grasp on Linux file permissions, however, is a giant step on the road to good UNIX and Linux administration.