A robust, powerful firewall with lots of extras, including a panic button and instant lockdown switch. ZoneAlarm Pro is a great security package.
Introduction
ZoneAlarm Pro by Check Point Software Technologies is a competitive security package that has carved a niche as a robust firewall that can be customized to your specifications. ZoneAlarm is distinct in that it leverages a security approach common in some military and civilian scenarios. Terms like “security zones,” “lockdown,” “perimeter security,” and “alarm” are very apropos when attempting to understand the ZoneAlarm model. The product makes good use of this model and implements it effectively.
The product installs easily enough, although it requires more user interaction than I care to give. I encountered none of the uninstall problems that people have complained about in the past. Registration is not required but a post-install reboot is. Once installed the product ran with a very small memory footprint and performed admirably in my test.
The user interface is busy but reasonably clear. While it’s easy to get lost in the many layers of options and dialogs, most users can proceed by modifying a few top-level properties and ignoring the customization buttons that almost every screen provides. Power users will love the extensive flexibility of the firewall. The general user will find the product simple enough to install it and forget it.
Price to Value (5 out of 5)
What’s Hot:
It will be hard to beat the feature richness and robust implementation of the well-rounded firewall. Power users will love the advanced ‘firewall rules’ that can be written and general users will find the level of protection worth the money.
Installation & Setup (3 out of 5)
What’s Hot:
The installer writes roughly 33Mb to the hard disk and creates almost 200 registry keys. The uninstaller cannot be run by rerunning the installer therefore uninstalling requires a trip to the Windows Control Panel or Start Menu (ZoneAlarm puts a link to the uninstaller in their menu listing). The uninstaller verified permission to uninstall (so a virus or malware doesn’t uninstall it without you knowing about it) and cleaned up the disk quite well. However, it did leave behind a significant amount of registry entries.
What’s Not:
Installation went smoothly but it requires a fair amount of interaction from the user. The second screen in the install wizard asked for registration information. Registration is always irritating and I was annoyed about entering personal information before the product was even installed.
-
At the end of the installation, you’re prompted again for registration information.
-
The installer does require a system reboot but before the reboot, you’re told about more services ZoneAlarm offers.
Advertisement -
I understand why software companies want users to register and use online services. When a user registers, not only does a company get information that will allow it to sell direct, but it also is able to better track how many people are using their software. A company can also track the conversion rate from purchase to install. Still, registration should be a background process and not something the user is hit with more than once. At the end of the installation, you’re asked to join DefenseNet.
User Interface (4 out of 5)
What’s Hot:
The main UI is busy and initially struck me as a bit dated. It worked more like a web interface than a desktop application. It uses a page and tab metaphor (as do many other security applications) but the implementation isn’t slick or clear like other packages I’ve tested. Still, it works well once you learn how to navigate it.
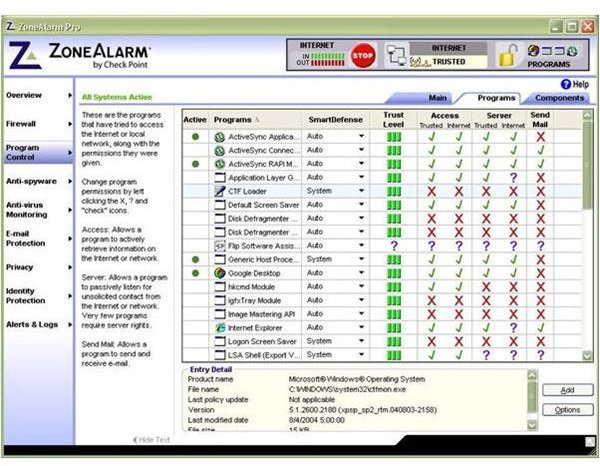
Other pages of the interface are clearer and the ZoneAlarm UI designers provide plenty of information. The program control section of the UI is busy but informative. In this tab you can view the programs with which ZoneAlarm has interacted. Here it displays the level of trust each program has and the access granted by ZoneAlarm. You also can easily see which programs are currently active.
Each major feature uses a slider control to set the security level for that feature.
The sliders work well and are clear and simple to use. Each feature subsection contains a customization option that provides another level of feature detail. The spyware scanner worked well and the report was clear and usable. I did notice a significant performance hit while the scanner was running (I’m referring here to the system-wide scan not the runtime scanner).
What’s Not:
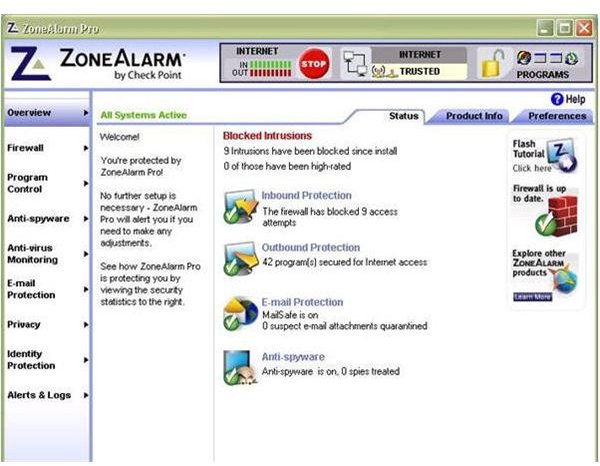
Interface oddities abound. On the Overview page of the UI, there is an admixture of information, tutorials, functionality, help text, and advertisements. I can learn that all scanners are active but ZoneAlarm indicates this to me with small green text at the top of the tab group. It looks more like a title than an indicator. In red text below the tabs in the tab group, I’m told how many intrusions were blocked. Underneath that I’m given a rundown of the activity of the various scanners. To the right of these icons are more icons that appear to be buttons. These buttons do not have any rollover effects nor does the icon change when you hover over them. But they are active and take the user to various functionalities. Finally, at the bottom, beneath the tab group are two small grey text hyperlinks. One hides the text (what text? ; perhaps “Hide Message” would be clearer) and the other I can use to “reset to default” (reset what to default?).
The top message bar (which is not a banner ad) includes a stop button to stop internet access, a lock icon which locks down internet access, and a small bar that contains icons of running programs that are using the network. The icons are not rendered well and look out of focus and malformed.
Product Features (5 out of 5)
What’s Hot:
ZoneAlarm Pro includes a Spyware scanner, email protection, privacy and identity protection, and a firewall. It doesn’t include virus software but will monitor third-party virus software installed on your system. This enables you to manage all your security products through a single interface. ZoneAlarm Pro also integrates cleanly with Windows’ Security Center.
When ZoneAlarm loads for the first time, you’re asked if you want to watch a video tutorial to become acquainted with the software. This is a nice touch for those who want to get oriented to the software quickly.
The “ZoneAlarm” name really is descriptive in the case of this software. First, the “zone” part. The ZoneAlarm firewall rightly divides your network into two zones; trusted and internet. Each IP address that is being used by your network can be added to either of these zones. At first launch, ZoneAlarm asks about the IP addresses on your system and into which zone each should be placed. This is a unique approach to securing a home network and I liked it. With other software the user has to see multiple popups while the software learns which applications to trust and which ones not to trust. With ZoneAlarm you can add traffic along a specific IP into the trusted zone and don’t have to be constantly asked if activity on that IP should be trusted or not. Some users may want that granular oversight but I like security software that is smart enough to manage those decisions and let me do other things.
One of the more powerful features of the firewall is the ability to set up rules. This is for the power user (in fact ZoneAlarm puts this feature under the “Expert” tab) who has a complex environment and needs the power of flexibility. This feature allows users to set up security on specific network paths using specific network protocols. Say you want files to travel from a computer with an IP address of 11.1.11.2 to a computer with an IP address of 11.1.11.16 using the TCP/IP protocol and the communication can only happen from 1am to 3am on Tuesdays. ZoneAlarm’s rule feature allows you to set that up and it’s fairly easy to do.
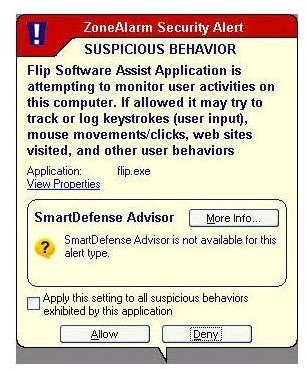
ZoneAlarm’s scanners also look for applications that engage it. What it determines to be “suspicious behavior” will trigger a pop up warning message. The alert is quite busy and didn’t clearly indicate to me what application was causing the issue. The application title is too small to see quickly and make a decision about . However, once I knew where to look future alerts were dismissed more easily.
Now the “alarm” part. One of ZoneAlarm’s distinctions is in the way it provides for the ability to quickly shut down internet access in the event of an attack. It uses a kind of “panic button” approach where it allows the user to tell ZoneAlarm to stop all traffic to and from the internet by hitting a big red button. Internet access can also quickly be locked down by clicking the lock icon in the top tool bar.
Additionally, ZoneAlarm supports the ability to turn off internet access when the screen saver kicks in or when the computer has been idle for a specified amount of time. For users who only want to be connected to the internet when they’re in front of their computer, this is a novel way to provide for that. Instead of having to turn your computer or cable modem off when you leave, ZoneAlarm will automatically handle access for you. It’s certainly a novel approach and one that I have not seen in other packages. For many, this type of modulated access doesn’t support usage patterns. However, for the occasional browser or emailer who doesn’t want to be concerned with activity on their computer while they’re away, these features could be effective.
Performance (5 out of 5)
What’s Hot:
My goal in testing performance was to see if the runtime scanners would cause any noticeable slowdown while doing daily tasks like copying files or browsing the internet. To create a more controlled environment for these procedures, I wrote a small software program that does the following. The first test copies five 21MB files over my home network from the local machine (on which Internet Security is installed) to a network share and precisely times the process. I run this test five times and take the average number in milliseconds. This test is run twice, once with the scanners running and once with them turned off. The second test involves copying 300 8K files over the network. I wanted to see if the smaller files would negatively affect the scanning engines. This test is also run five times with both the scanners running and not running. The average time in both runs is calculated in milliseconds. Finally, my program downloads the full content of five major web sites with complex layouts. I ran each test five times on a 2.2Ghz Celeron, 1Gb RAM, Windows XP SP2 with all the latest service packs. The destination machine is running Windows Vista Ultimate. Here are the results of the tests for ZoneAlarm Pro:
No Scanners
1. Large Files: 15734 ms.
2. Small Files: 4792 ms.
3. Web sites: 6017 ms.
Scanners
1. Large Files: 16130 ms.
2. Small Files: 4271 ms.
3. Web sites: 5434 ms.
ZoneAlarm did very well in my time tests. In fact, it performed the best out of the batch of security software that I tested. Part of the reason may be due to the fact that it separates the network into zones and trusts the zone rather than having to touch each file that passes through it. Another factor clearly at play here is that ZoneAlarm is not doing virus scanning which greatly affects the performance of the types of tests I’m running.
I did have one issue with the scanning engines. While they did shut down easily enough, I had a problem when I tried to restart ZoneAlarm. The application appeared to be starting but would fail and retry over and over. I got a dialog box telling me that it was attempting to initialize. I could not stop the process in Windows TaskManager and the only way I found out of the loop was to restart my computer.
The ZoneAlarm runtime nibbled a very modest 3 Mb of RAM.
Images













Suggested Features
Check Point should include the ability to manage the firewalls of other computers on a network. This would make the package more attractive to small businesses. With the power and extensibility of this software, that definitely could be a strong market.
Conclusion
ZoneAlarm Pro turns out to be a very solid firewall package. As I say in all my reviews, the real proof is when you use it. I recommend users download a trial and test the product in their environments before making a final purchase decision. Still, on the face of it, ZoneAlarm excels at what it does. It offers plenty of extensibility to keep computers on larger home networks or small business networks secure.


