Along with the challenges of managing the operations of the business, small business owners must concern themselves with network security issues. In this guide, we explain how small businesses can deal with those network security issues.
Small businesses are constantly at risk from attacks to their network security. Not only can spam email, viruses, worms, trojan, spyware, and zero-day attacks cause a business to lose revenue, but also productivity and embarrassment as well. In order to ensure that all the resources on the business’ network are secure, network administrators must take steps to ensure that the business doesn’t lose money, suffer embarrassment or is liable to litigation as a result of network security issues.
Security for Your Small Business Network
Not only does strong network security prevents malicious entities from infiltrating your network but it also gives small businesses the following advantages:
- Promote collaboration - As employees, vendors, partners, suppliers, and other parties work to ensure that all communications are secure and un-compromised, the effort improves communication and therefore a spirit of collaborations among the parties involved.
- Improve productivity - By not having to deal with security issues, the IT staff, and employees in general, can apply their time to more productive activities. A more secure infrastructure also allows the business to give employees greater access to the tools and resources they need to do their jobs well, even while they are on the road or on vacation.
- Easily scale up your Network – By having a robust network infrastructure; the network can easily be expanded without much trouble. This means that new branches and offices can be easily added to the network, without there being a need to redesign the network.
- Enhance the customer’s experience - By allowing customers to securely access confidential information, in a hassle free manner, the level of satisfaction among customers will improve.
- Reduced the risk of litigation – Strong network security also reduces the risk of litigation by better protecting sensitive customer, client and partner data from loss or security breaches.
Basic Network Security - A Firewall
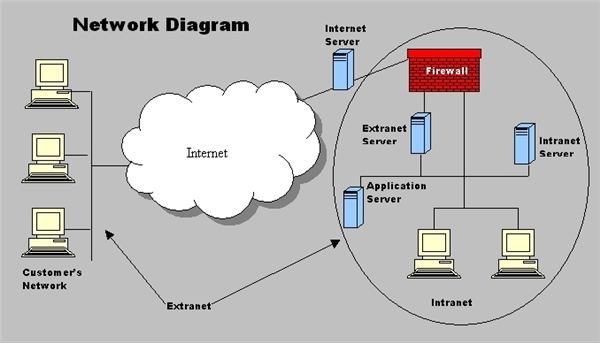
As a bare minimum requirement, every small business should have a firewall as part of their network security measures. Firewalls provide a first line of defense against potential threats to network security. A firewall serves as a shield between the small business’ network and external networks such as the Internet.
A firewall continuously examines network traffic and ensures that all the transmitted data packets pass the network’s security rules before they are allowed to enter the network. If the data packet is questionable, the firewall should block it and any threat that it contains. Threats that a firewall and other security measures can block include: spam email, viruses, worms, Trojan horses, spyware, and zero-day attacks.
Network Security Solutions to Consider
The network security solution you’ll need depends on the nature of your small business, your current IT requirements and how much you expect to grow in the future. If for example you have several branches or remote partner sites, you may want to use a VPN (virtual private network) to connect the remote offices securely over public networks or cheaper data telecommunications options such as DSL.
You may also want to consider employing a remote network monitoring service to ensure that you have the required experts who can respond, at any time, to a network security issue.
Be Prepared for Future Network Security Challenges
Most small business owners have hopes of making it big. However, along with growth comes the challenge of finding the resources to finance the acquisition of new office space, equipment and staff. With growth also comes the scalability challenge of getting legacy equipment such as network appliances to work together.
Managing a larger operation will also bring new security threats, and small businesses must be prepared to deal with them. Regardless of the challenges that a business may face network security for small businesses has to be a top priority for management, especially if they have any hope of keeping the network, and all the resources that reside there secure.
Reference:
Image: “Network Diagram” contributed by the author. Some rights reserved.