Network segmentation has become an important part of a layered defense. In this article, we look at how segmentation works, how to use the reasonable-and-appropriate metric to ensure business processes don’t suffer, and network segmentation security risk.
What is Network Segmentation?
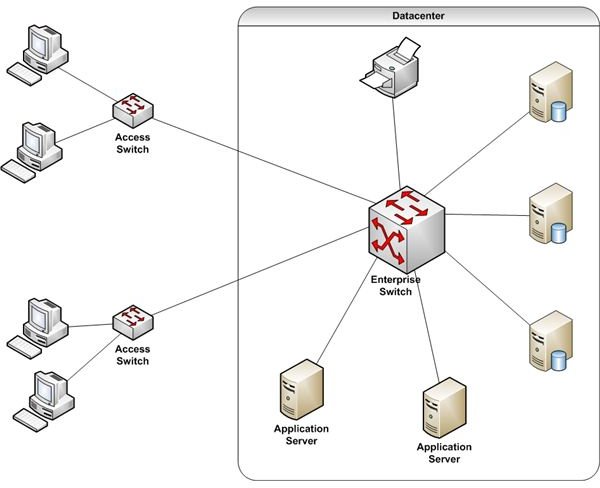
Traditional network design placed all servers and other network-connected information resources, into a common network segment. Figure 1 is a simple example.
All systems are connected via a switch, which means each system can “see” all other systems. While authentication and authorization layers should help keep unauthorized users from accessing sensitive information, a much better approach is to prevent unauthorized packets from getting to restricted systems in the first place. Network segmentation is the foundation for this approach.
Segmenting a network allows placement of critical infrastructure and sensitive data behind virtual locked doors. User devices must meet certain criteria to unlock a door, even before user access is authorized.
How Network Segmentation Works
The most common approach to network segmentation is use of Virtual Local Area Networks (VLANs). A VLAN is created by the appropriate configuration of a network switch. Most switches today, even small office and home office models, support VLANs.
Once a VLAN is created, access to it is controlled with an access control list, also configured in the switch. One caveat… if you plan to share data across VLANs, the switch must also support Layer 3 operations (i.e. routing). For detailed information about how this works, see Strengthen Data Protection with Network Access controls and Consider secondary VLANs to isolate critical or high risk systems .
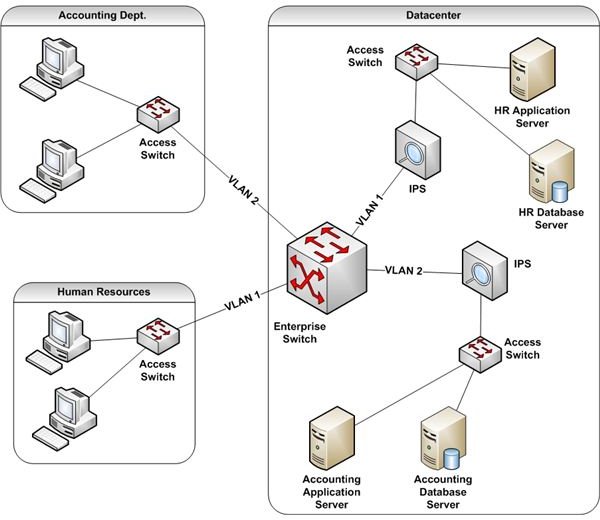
Figure 2 depicts a simple VLAN-segmented network. The enterprise switch configuration creates two VLANs, numbered 1 and 2. Traffic on VLAN 1 cannot see anything on VLAN 2 and vice versa. For example, packets between accounting systems will pass through the switch. However, the switch drops packets from Human Resources with a destination address for an accounting device.
If selected packets must pass from one VLAN to another, the switch must be able to route them.
Network Segmentation Security Risks
Again, network segmentation is a useful security layer in a defense-in-depth strategy. For example, it controls malicious attacks by:
- Restricting worm activity to the initially infected segment;
- Allowing isolation of compromised segments without taking down the entire network; and
- Providing another obstacle to human intruders who might gain logical access to a network-attached device.
But as with any security control, segmentation is not a panacea. VLAN controls can be bypassed with widely available products. Since a motivated black hat hacker can break through segmentation barriers, this control should not be considered alone for regulatory compliance.
For example, some vendors might try to sell a VLAN product to segregate PCI-controlled data as a way to minimize PCI compliance costs. Businesses who buy into this cost-reduction argument, and which fail to support segmentation with other controls, are putting themselves and their customers at risk.
In addition to IPS solutions, other controls to consider as support for segmentation include:
- Blocking all packets without a legitimate source address (e.g. packets with a source address outside the protected network’s IP address space); and
- Blocking all packets from an external source which use an internal address as a source address.
Both of these settings prevent IP address spoofing, one commonly used method to bypass VLAN access control lists.
Finally, segmentation itself can be a business risk. If not properly designed, it can present an obstacle to both IT and business operations.
The network should be segmented only as far as is appropriate, given data sensitivity, server criticality, and the organization’s willingness to accept risk. The basic premise that complexity is the enemy of security should be kept in mind during network design. Further, adding segments just because you can can lead to:
- Unexpected and unnecessary network performance issues;
- Higher than necessary costs for network devices; and
- VLAN and user access management challenges.
The Final Word
Yes, there are ways to bypass network segmentation used as a security control. However, this is true for any security control. The key is to see network segmentation as one layer of several which support each other. Each layer checks to ensure the other layers have done their jobs or have not been compromised.