Need to check your online databases for vulnerabilities? HP offers a free tool to check your website for SQL Injection vulnerabilities. HP Scrawlr crawls your website looking for exploits and flaws in your code. This software is free and easy to use.
Introduction
SQL databases are the world’s fastest database. With SQL millions of transactions can take place each second and PHP and ASP code handling the SQL connections; poorly written code can make your site vulnerable to attack. Hackers can insert code to take control of your server’s database. Protecting your SQL database is important. Testing software and the security of your network should be a part of your security audit. HP offers free software to scan your website for SQL vulnerabilities. Scrawlr is legal to use on your website and should not be used on sites not owned by your organization. Security Analysts should have this important tool as part of their arsenal of security tools to perform penetration test.
It is important to test your SQL websites for vulnerabilities. Finding vulnerabilities now will help to prevent data loss in the future.
HP Scrawlr
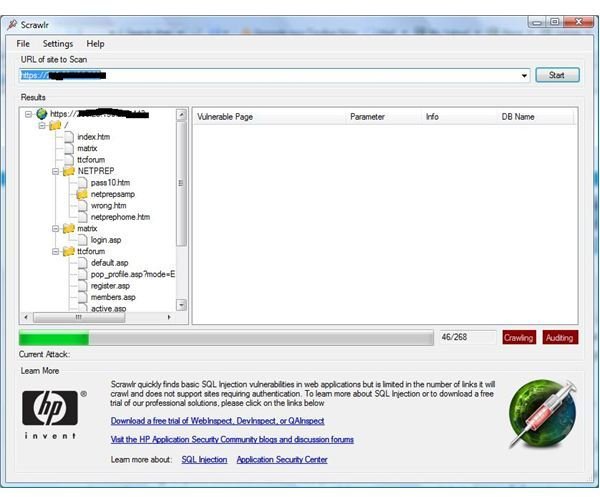
Hewlett Packard offers a free tool to crawl your website and look for vulnerabilities. Scrawlr was developed by HP’s Web Security Research Group to look at each individual web page for SQL Injection exploits and vulnerabilities. The program is very fast and uses HP’s intelligent engine technology to create and dynamically perform SQL Injections during the operational run. It gives a simple report so the administrator can analyze the results. If the program is successful, you can see the database and tables.
SQL Injection
Hackers can use simple SQL commands to insert, delete or take control of your entire database. By finding the database on the web, simple commands are ran against the database thus returning confidential data that can be copied and saved to the Hacker’s computer. Here’s an example of a simple SQL Injection:
This is bypassing login forms. Here’s an example of the actual application code:
SQLQuery = “SELECT Username FROM Users WHERE
Username = ‘” &
strUsername & “‘ AND Password = ‘” & strPassword & “‘”
strAuthCheck = GetQueryResult(SQLQuery)
If strAuthCheck = "" Then
boolAuthenticated = False
Else
boolAuthenticated = True
End If
During a typical login, a end-user goes to the site and submits their username and password. The Query goes to the ‘Users’ table to see if there is a row within the table that contains a username and password. With bad ASP code or PHP code, the hacker may be able to this type of code to get in.
Injection Code-
Login: ‘ OR ‘‘=‘
Password: ‘ OR ‘‘=‘
This gives SQLQuery the following value:
SELECT Username FROM Users WHERE Username = ‘‘
OR ‘‘=‘‘ AND
Password = ‘‘ OR ‘‘=‘‘
By leaving this information without a valid username but placing quotes and the word ‘OR’ or the symbol ‘=‘ , the hacker may be able to bypass this login screen.
Conclusion
While there are thousands of ways to perform an SQL Injection, this is far from being perfect ‘hacker’ code. This article is not about ‘HOW-TO’ hack, it is how to help protect your website. HP is only one of many tools that you can use against your own website. Penetration testing is important in protecting your assets. It helps to not only test your code, but also helps to test your firewall. HP lists these limitations on their Scrawlr software :
· 1500 Max Crawled URLs
· No Script parsing during crawl
· No Flash parsing during crawl
· No form submissions during crawl (No POST Parameters)
· Only simple proxy support
· No authentication or login functionality
· Does not check for blind SQL injection
While no software is perfect, all vulnerability and exploit testing helps. You should never be given a blind sense of security by running just one test from one software application. Kudos to HP for creating a software that ‘helps’!
This free document from HP shows how SQL Injections work. PDF Document
Scrawlr Download



