Putting in place private security forces and security devices does not fully guarantee the safety of customers, employees and property. Hence, business organizations are advised to assign the task of monitoring these measures to experts who have adequate knowledge on how to audit building security.
A Matter of Keeping the Security Systems Up to Date
The appraisal and examination of a building’s security system should not be relegated as part of an internal control review nor should it be taken in the same context as that of a building inspection exercise. Apparently, advancements in technology and sophisticated methodologies have likewise influenced the capabilities of criminal elements. But the recent incidents of anarchy in one of London’s busiest areas show that threats to safety can take any form of activity.
Although this denotes that there are no failsafe guarantees, the recent occurrences give emphasis to the importance of re-assessing the security checks and measures that are in place. An outside organization may be hired to perform the assessment, but business owners should be able to tell if the organization being hired really knows how to perform an audit of a building security system.
Basically, it should be conducted not as a reactionary measure but should be maintained as an ongoing process of establishing and identifying current issues and concerns that require the integration of relevant policies.
Find below an example of an audit plan that serves as a guideline for assessment. It will help you immediately ascertain if there are issues that need to be addressed without further delay.
Developing the Plan

1. Define the Objective of the Audit
There should be a clear definition of the objectives to be attained since the entire building’s security cannot be assessed with just one sweeping motion. A general statement is too broad and all-encompassing; hence it would be best to identify specific areas of concern to avoid redundancies of tasks that are being performed as part of internal control reviews and building inspections.
As an example, the objective of the audit plan is to determine the effectiveness of barriers against physical entries to ensure the safety of the customer, visitors, employees and contractual workers while working within the building’s premises. It also will prevent any acts of burglary or theft over company property including informational assets and personal belongings, and other damages that may arise from such acts, which include sabotage, arson, vandalism or the spraying of graffiti.
2. Establish the Scope
In establishing the scope of the audit, indicate the premises covered–whether it’s the entire building or a specific area of concern. The latter is usually determined by the need to immediately reinforce security with policies and measures for on-the-spot implementation.
3. Set the Criteria
This section makes mention of the standards to be observed and the related policies that are currently in place for the risk prevention and mitigation strategies that have been previously formulated. Examples of standards are ISO 27002, BS 1722: Fences; BS 1722-14:2001 Fences. (Specification for open mesh steel panel fences); BS 362: Specification for thief resistant locks; BS 4737: (all parts), and Intruder alarm systems, just to name a few.
4. Specify the Audit Methodologies to Be Used
There should be a clear statement of the methodologies to be used to ascertain that all team members are performing the audit examination according to the plan of execution. Some examples of such methodologies include, but are not limited to:
-
Survey questionnaires for all building occupants.
-
Interviews with the designated officer-in-charge of the security management for the specific area or the entire building.
Advertisement -
Interviews with staff in relation to their work places or areas of concern to ensure that only first-hand information will be used as bases.
-
Review of written policies and procedures.
Advertisement -
Actual testing of the security implementation and its current integrity, in light of recent developments that can affect the present security set-up.
5. Indicate the Time Frame
The plan should make mention of the date the examination and evaluation will actually commence and the date of completion, as well as provide in details the time frames for each intended plan of action. This includes the dates for report submission and follow-up regarding the implementation of approved recommendations.
6. Perform the Security Risk Analysis
Security policies and actual practice vary between different departments; hence, all analysis should be developed on a per-area or a per-department basis. In connection with this aspect, the following important steps should be noted:
-
Begin the risk assessment by asking all department members to answer the questionnaires.
Advertisement -
Summarize the results of the survey questionnaires.
-
Compare the actual practices against the standards and the policies to determine compliance.
Advertisement -
Test each security procedure to assess its integrity in view of the current set-up and in light of recent methodologies being used by criminal elements.
-
Conduct the interview to gather additional information.
-
After each test, identify the areas of vulnerability and susceptibility to risks or threats.
-
Prepare documentation of the observations, particularly the deviations from the standards and from the policies.
-
Discuss all deviations with the officer-in-charge of managing departmental security and be sure to secure his explanations or reasons for deviating from the standard or the policy.
-
Observe any risk strategies that have become obsolete or ineffective in light of new developments in technology.
-
Determine if there have been any occurrences of actual breaches.
-
Test the barriers to physical access and the scope of restrictions or if all mechanized devices are working.
-
Evaluate the security equipment and devices in place to ascertain the quality of information provided as well as the reliability of the procedures implemented in storing or releasing back-up records. Take note of equipment items that are frequently in need of repairs.
- Examine all locks and the frequency by which locks or dial combinations are being replaced within a given period. Determine the reasons or explanations why they had to be replaced.

- Take note of minor discrepancies or inefficiencies inasmuch as the slightest infraction could present an opportunity for anyone who intends to use them for unscrupulous purposes. Examples of these minor infractions include:
a. Doors of secured areas are often left unlocked every time a staff goes out.
b. Lack of sufficient information in the visitors’ registration logbooks.
c. Some staff are allowed to roam the premises without any ID tags worn or displayed for immediate identification.
d. There is non-maintenance of an ID issuance register.
e. Visitors are allowed to roam around the premises unaccompanied by the host official and/or without visitor ID passes.
f. Inconsistencies or haphazard methods in the performance of security checks on all personnel and visitors that enter the premises.
g. Untrained staff members are allowed to perform security-sensitive tasks (see image at the left of a bank security guard sleeping while on duty).
7. Evaluate the Physical Structure of the Premises
Evaluate and test the existing policies and procedures to determine their suitability and adequacy of measures being implemented based on the after-policy improvements made on the building and its premises.
-
The building may have undergone refurbishment, renovation, new additions, and new technological add-ons, altered floor plans and layouts, which call for additional measures to be instituted as policies.
-
New complexities may likewise require increased governance, additional security checkpoints, assignments of security personnel or alert and monitoring systems.
-
Interview all personnel about their knowledge in identifying indicators of possible security threats that may be present in the building, i.e. bomb threats, unusual activities and unauthorized entries. Know employees’ perception of the risks and threats involved and the actions they intend to take.
-
Test responses to security breaches and evaluate how well the related policy measures are being handled. Include an examination of the records reporting any incidents of security breaches.
-
Ascertain the kind of governance being implemented in relation to security matters to determine if the people inside the building are aware of their significance. Check memorandums, reprimands and handbooks.
-
Know the information being given by the frontline staff and the night-desk clerk.
-
In view of the increased risks from bombs being placed in parked cars near buildings, determine the security policies instituted to address this issue.
8. Gather Feedback from External Sources
Understand how customers or visitors feel when visiting the premises through questionnaires or interviews when necessary. Gather information from around the immediate vicinity, which may have relevance to the present state of security of the area.
9. Submission of Reports and Recommendations
All observations, exceptions and analyses gathered should be brought forward with their corresponding recommendations. Although the primary goal is to assess the present conditions and status of the building security, the ultimate goal of the audit exercise is to institute corrective measures that will improve the system. Recommendations should not be brought forward in terms of generalities but should go into specifics to ensure that the problems will be properly addressed.
10. Performing Post Monitoring on Approved Recommendations
Anyone who knows how to audit building security is aware that the final step is the performance of follow-up procedures. This is to ensure that the flaws have been corrected and that the safety of the customers, employees, the organization’s property and informational assets are kept secured.
In addition to the formal report and recommendations, organizations that are in the business of conducting security audits include an executive summary of their findings and professional assessment. This summary is often used to satisfy certain regulatory requisites for an independent review of a building’s security system along with its policies and procedures.
References
- Image by Olympus E-420. – A police officer in riot gear at the London student protests , 9 December 2010.Wikimedia/ CCA 2.0 Genetic
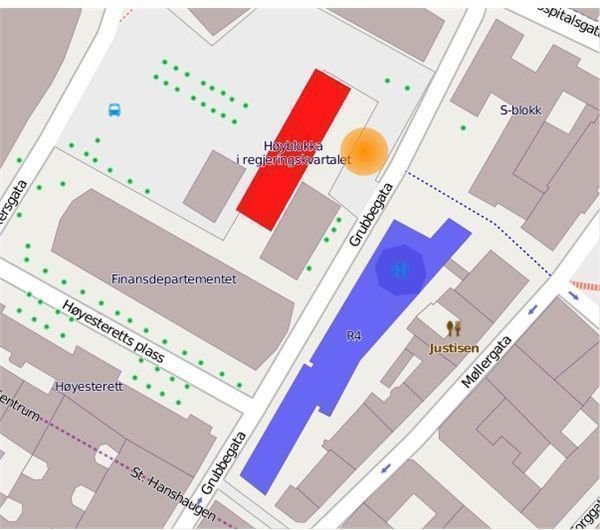
- Image by Albin Olsson – Map over the 2011 Oslo attacks .Wikimedia/ CCA SA 2.0 Generic
- Image by Anthony Newman – Aftermath of some of the previous night’s looting
around Ealing Wikimedia/ CCA-SA 2.0 Generic - Image by Huaiwei – A CISCO officer and security guard conducting routine
patrols around the Esplanade’s grounds.Wikimedia/ CCA-SA 2.5 Generic - Indiana.edu Safe and Responsive Schools Security Audits and Inspections – http://www.indiana.edu/~safeschl/security_audits_and_inspections.pdf
- By Snyder, Loren - A Closer Look At SECURITY AUDITS -http://www.facilitiesnet.com/facilitiesmanagement/article/A-closer-look-at-SECURITY-AUDITS–1725#
- Image by V85 (talk) – Security guard sleeping on duty . Wikimedia/ CCA 2.0 Generic



