Computer hacking has hurt a lot of people by stealing bandwidth, copying personal information, hijacking identities, and spreading cyber attacks. Although individuals often seem hit the hardest by the hacking underworld, corporate victims of hacking represent a whole separate category of loss.
Victims in the Shadows
The dark world of corporate hacking has made some hackers rich as corporations scramble to avoid bad publicity, plug security holes,
and sometimes even hire hackers to test their security practices. These corporate victims of hacking lose proprietary data, production time, and reputation and are often some of the least publicized victims of the Information Age.
On the side of the corporate victims of hacking is the federal government which often uses its power to seal records and keep hi-tech intrusions off the front pages where they could inspire more attacks and deter customer confidence. Still, word of corporate hacking attacks gets into the public domain, especially when customer data such as social security and credit card numbers are compromised.
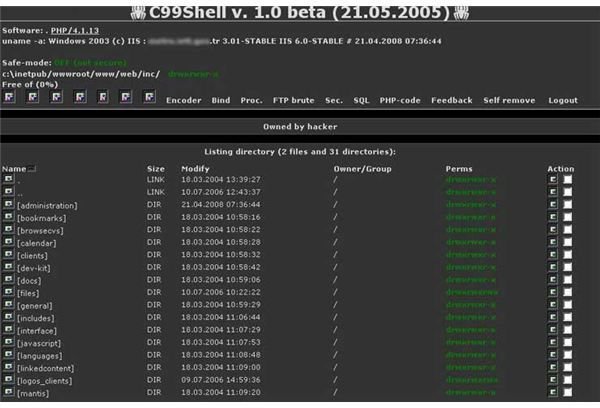
Image Credit: Wikimedia Commons/Samukt
Escalating Hacking Incidents
As more and more businesses become corporate victims of hacking, more aggressive legal actions are being taken to punish hackers for their deeds. A college student that hacked email accounts belonging to the former governor of Alaska was brought to trial and penalized for his behavior. Similarly, those hacking corporate networks are being hauled into court, such as the famous case where five corporations including 7-Eleven were hacked .
Prosecuting hackers may prove to be an ineffective method for dealing with hackers, as evidenced by the growing international flavor of cyber crime.
Perhaps one of the most widely publicized hacking stories of 2010 involved the way Google’s Chinese operation was hacked, leading to no small stir as Google exited China proper in protest, leaving its market to be filled by its native rival, Baidu.
When stolen sensitive American documents appeared on the Internet, the American government became a victim of cyber crime, although it may not fit the strictest criteria for hacking, but it did represent a serious security issue existing within the United States military and the American government. According to some reports , the document dump included evidence that suggested that the Chinese government was behind the attack on Google, making it one of the first corporate victims of hacking perpetrated as part of government policy.
Also in 2010, the Chinese government was implicated in several high profile cyber attacks on the United States in media reports including some from the New York Times . For a short time, the hacking was so massive that it hijacked network traffic from the United States Congress and the Department of Defense, routing it through servers in China where some suspect national security information may have been siphoned off. The Wikileaks documents purportedly contained information that substantiated these suspicions.
Learning the Lesson
Although the many corporate victims of hacking represent just some of the casualties of an escalating cyber terror war which many fear the United States government and business sector is losing. Aware of the danger involved in becoming hacking victims, corporations have increased their spending on Information Technology security, beefing up an industry that once seemed to be in decline.
Unfortunately, the skills of hackers with resources furnished by powerful governments continues to eclipse the pace at which security countermeasures are developed. For this reason, corporate entities must make a conscious effort to beef up their security budget while staying on the cutting edge of newly developed countermeasures.
With high profile victims like Google and the United States Government, all businesses should understand once and for all that they are at risk and that serious action must be taken to prevent them from becoming corporate victims of hacking.