While visiting a secure website, you may receive a security alert stating that revocation information for the security certificate is not available for this site. Check this article on how to solve the security warning in Windows.
Alerts When Visiting a Secure Website
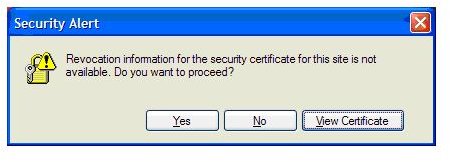
When you visit a secure website you may see a security alert dialogue box stating “Revocation information for the security certificate for this site is not available. Do you want to proceed?” The dialogue box provides an option to view the certificate of the secured domain or webpage. You don’t have to panic but you will need to scan the certificate for more information.
Image Credit: Xobni Forums/Francois https://community.xobni.com/xobni/topics/revocation _information_for_the_security_certificate_for_this_site_is_not_available
What is Security Certificate Revocation Checking?
Microsoft, Mozilla and other browser vendors have installed root security certificates that have passed their requirements. You can view the trusted certificates using the browsers’ advanced settings. The browser vendors and Microsoft have arranged with Certification Authorities (CA) to provide and update the list of revoked certificates. Checking of public key certificates is done using three methods:
- Certificate Discovery
- Path validation
- Revocation checking
Please note that by default the Windows operating system checks the certification revocation status via certificate revocation lists (CRL). For more information, visit https://technet.microsoft.com/en-us/library/cc700843.aspx
Visiting a secure website will not display a security alert or warning, if the security certificate is valid, not expired or authorized. However, if you receive a security alert stating that revocation information for the security certification for the website is not available, it means the security certificate has been revoked or found in certification revocation lists (CRL). It can also mean that the security certificate is valid but the CRL distribution point is unavailable.
Other reasons for the security alert are that your computer time or date is set incorrectly or the browser is configured to automatically detect a proxy server settings but no proxy server is configured.
What to Do if You Receive a Security Alert on a Secure Website?
If you visit a secure website and the browser displays the “Revocation information for the security certificate for this site is not available” warning, you need to check the certificate by viewing it. If the date is expired, report this to the administrator of the website. If the date is valid, check with security certificate issuer about the validity of the security certificate. You should also ensure that Windows has all the necessary updates, especially the Update for Root Certificates .
An Automatic Root Certificate update is enabled by default in XP, Vista and Windows 7 and you can find it in the Group Policy console of Windows:
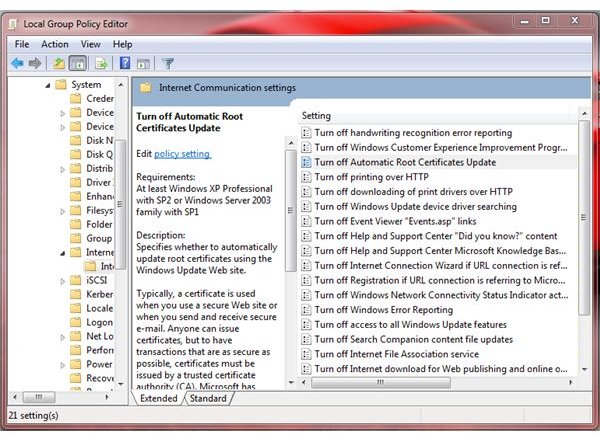
It is recommended to keep the settings as is to help protect your computer and personal information. If you a phishing or rogue distributor website is using a stolen or fake security certificate, the browser should display a security alert about the security certificate. This is true if the security certificate is listed in the revoked certificate lists.
Other internet users have reported that the time or date in Windows is not set correctly and when they corrected the time/date settings, the revocation security alert upon visiting a secure webpage is gone. If the time and date is correct, try to clear the Secure Sockets Layer (SSL) state by going to Internet Options, clicking the Content tab, and then clicking “Clear SSL state”.
Another possible solution is to re-register the following dll files:
- regsvr32 softpub.dll
- regsvr32 wintrust.dll
- regsvr32 initpki.dll
- regsvr32 dssenh.dll
- regsvr32 rsaenh.dll
- regsvr32 gpkcsp.dll
- regsvr32 sccbase.dll
- regsvr32 slbcsp.dll
- regsvr32 cryptdlg.dll
Or automatically re-register the .dll files by using the Microsoft Fix it 50191 solution.
If the above work-around will not help you, it is really best to scan the certificate for validity. Do not rush into visiting a website that has a security certificate issue unless you are quite sure that it is not a fake or malicious website or has not been compromised. In some cases, a legitimate or valid security certificate is issued to rogueware and malware distributors, which is a tough situation that Internet users face. It is recommended that you review the certificate practice statements by security certificate issuers. Example: VeriSign published their statement in PDF format at https://www.verisign.com/repository/CPS/ .
Using antivirus program that will prevent visiting rogue or malicious websites, which may or may not use secure protocol (HTTP), is also recommended. Please note that turning off the server and publisher’s certificate revocation in the browser is not recommended.
Image Credit: Screenshot taken by Donna Buenaventura