Hey - before you go hacking your teacher’s PC, why not think for awhile about what you’re doing? What will you do next - steal his car? There are lot of consequences to hacking into another person’s computer and I’ll cover them all in the article below.
The Dangers of Hacking
Hacking is a dangerous game. Unless you know exactly what you’re doing, and who you could harm, then you shouldn’t attempt it.
From a moral point of view, if you don’t know what the outcome will be and aren’t willing to take responsibility for your actions, the consequences of hacking into another person’s computer could be considerable.
This guide explains a few things that you should consider before hacking a PC. Whether you’re sat in front of the target PC or you’re attempting to access it online, you’re playing a dangerous game. Hacking is a pastime that can leave you in serious trouble with the police and even government security services around the world, such as the MI5 and FBI.
Why Hack?
Why do you want to hack your target? We’ll assume that no-one reading this article is a professional hacker; you’re either trying to find out a bit more about hacking, or you’ve tried it before and are looking for some pointers to help you with your latest intrusion.
Because that’s what it is – digital breaking and entering, without the owner’s permission. Hacking means taking a risk. There is the risk of capture, the risk of being made an example of.
By hacking into someone’s PC or network you can gain access to personal, sensitive or business information, but detection, discovery and detention could follow soon after.
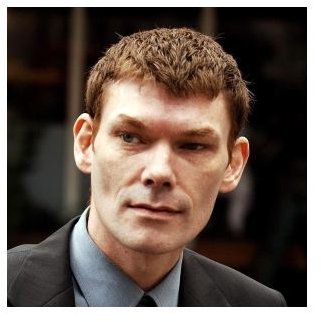
In 2001 and 2002, British hacker Gary McKinnon committed the largest military hack of all time, with the US claiming that he caused $800,000 worth of damage . While he claimed that his motivations were honourable , as of 2010, McKinnon is currently awaiting extradition.
(Image from UfoeAlieni.com )
Who Are You Hacking?
You should also consider who you are hacking, and what this would mean to the victim. While a bank or financial institution might have protection and enough on-site specialism to be able to avoid being hacked, you should remember that investors – be they everyday people with their savings lodged in the bank or actual shareholders – don’t have that luxury.
If you’re hacking into another person’s computer – either in person or across the internet – you might be doing it for a joke, or perhaps to prove a point.
Hacking a computer in person at best means trying to guess a password, at worst getting around some sort of physical encryption such as a keycard. Given that hacking is tantamount to a physical intrusion, think about it. Would you burgle this person’s home?
Legal Consequences of Hacking into Another Person’s Computer
As we’ve seen with Gary McKinnon, the legal consequences of hacking a big network are considerable; hacking your neighbour might not be personally devastating, but it would be immoral.
Of course, the legal consequences of hacking into another person’s PC depend entirely upon detection. Even if your victim suspects an attack, it is likely that they won’t know where it originates from unless they are specialists in the field of network security. As such, you would be hacking risk-free unless you were careless.
But you would also be guilty of a crime, whether caught or not. Morally, this behaviour would be wrong.
For safe, police- and litigation- free hacking, the use of a second computer with its own internet connection (perhaps via a tethered mobile device) as a target for hacking could prove a bigger challenge than your neighbour or colleague. By setting up your own defences, you will learn how to protect against intelligent attacks.
Read more about Ethical Hacking to understand legal ways to use your skills.