Guide in Securing Bluetooth in Windows or Bluetooth Wireless Device
Bluetooth Security
Bluetooth wireless connections are found in many wireless devices such as printers, smart phones, laptops, PDA’s, keyboards, cameras, game controllers and even a desktop or laptop mouse. These wireless devices are exposed to attacks if not properly secured.
If you have any device that has Bluetooth technology, you need to ensure that it is secure to prevent attacks. A Bluetooth connection should be turned off or disabled when not in use.
How Hackers Attack Using Bluetooth Wireless Technology

If the Bluetooth device or module is enabled and set to discoverable mode, it will send a signal to other Bluetooth devices that are near you. When a hacker or attacker finds your device, the person can attempt to pair his device with yours to perform Denial of Service (DoS) attacks on Bluetooth devices. Once the attacker succeeded in pairing the device, they can start hacking by stealing your information from the connected or paired device or use your device to send unsolicited images, text or video to other Bluetooth devices or even to your contacts.
The attacker can also install viruses, Trojans, Bluetooth worms or other types of malware to steal information or damage the Bluetooth-enabled device. The hacker can use commands on the device to read, copy, modify and delete phone book contacts or information on your calendar and notes. They can also secretly listen to conversations if the hacked device is a mobile phone like an iPhone or Blackberry. It does not matter whether the device is using Symbian, Linux, Windows, iOS, Mac or Android operation systems.
Securing Bluetooth in Windows or Any Bluetooth module
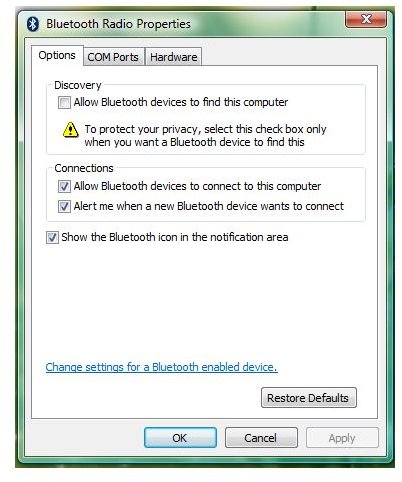
Below are some of Bluetooth windows security settings to help mitigate risks related to Bluetooth wireless technology:
-
Disable Bluetooth and only enable when ready to use.
-
Configure Bluetooth to notify you of incoming connections. Reject unknown requests to connect to your Bluetooth device or module.
-
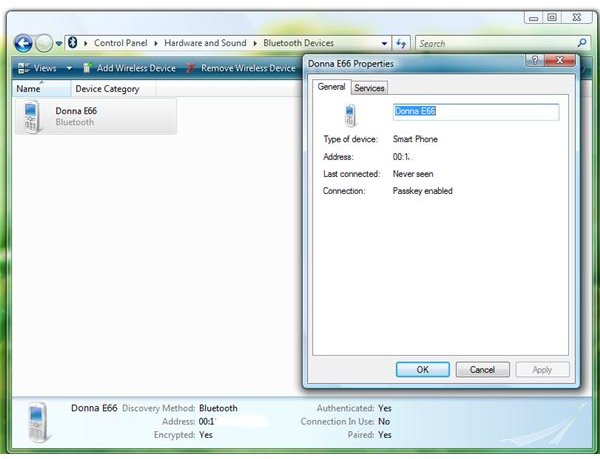
When pairing or connecting Bluetooth devices, always use a passkey or PIN.
-
Avoid using an easy to guess passkey or PIN such as 123, 1111 or 1234.
-
Use a PIN that is at least 8 characters long. Note that Bluetooth allows up to 16 characters on passkeys.
-
If you have enabled and paired a device using a Bluetooth connection, set the device as hidden.
-
Use antivirus software on Bluetooth devices such as a laptop, PDA, smart phone or desktop.
-
Set the Bluetooth-enabled device to use the lowest power range.
-
Install the latest service pack and critical updates for the operating system that include fixes to known Bluetooth stack vulnerabilities.
-
Delete the Bluetooth devices that are no longer in use using Bluetooth Device Manager. These might include old mobile phones that were previously paired to the laptop or desktop.
-
If you are using third-party Bluetooth software, check for updated versions from the manufacturer’s website and install the new version when available.
Image credits: Screenshots taken by the author. Bluetooth logo https://commons.wikimedia.org/wiki/File:Bluetooth_bw.png By DBGthekafu [GPL (www.gnu.org/licenses/gpl.html) or Public domain], via Wikimedia Commons
