What is Windows 7 Certificate Manager?
Different Kinds of Certificates
There are several different kinds of certificates. Personal certificates can be used to set your personal identity when you access a secured network. Intermediate certificates are frequently used to authenticate other certificates. And root certificates are used to establish the identity of other systems on the network, such as computers or servers, with which you connect. Let us take a look at each one of these in kind.
Windows 7 Certificate Manager
As an administrator, you have the permissions to view or manage the certificates. If you not logged in as an administrator, you must log off and log in again. The Certificate Manager will allow you to see the details about your certificates, how to modify them, or delete them, or even to request new ones.
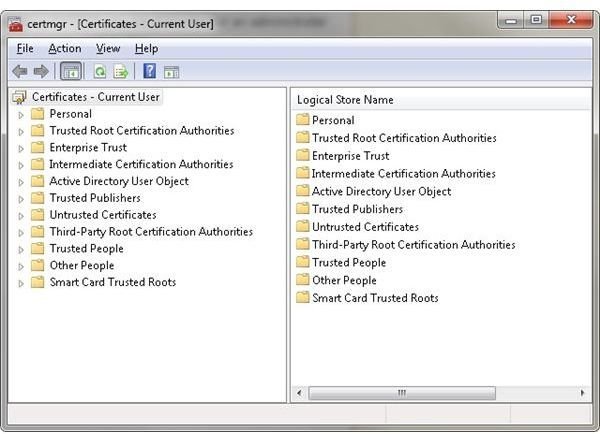
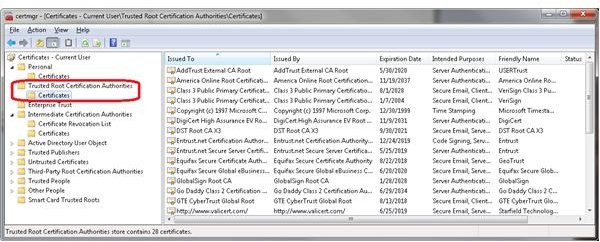
Here is how it works: You can open the Certificate Manager by clicking the Start button, typing certmgr.msc into the search box, and then pressing enter. You may be prompted for password or confirmation. If so, type the password or provide confirmation.
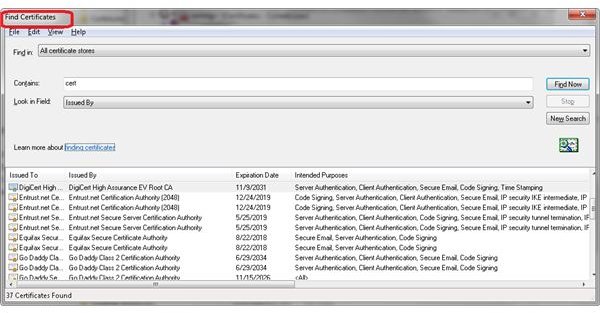
When you open the certificate window, the certificates will be displayed, and information about them, in the right pane, will be described. The Intended Purposes column identifies what each certificate is used for. Requesting a new certificate with the same key or a different key is possible. (Keys are encryption devices that are frequently furnished for you automatically.)
You can also export or import a certificate. But whatever action you want to perform, the steps are the same; just click the certificate, click the Action menu, pursue the All Tasks, and finally click the command that identifies what you want to do.
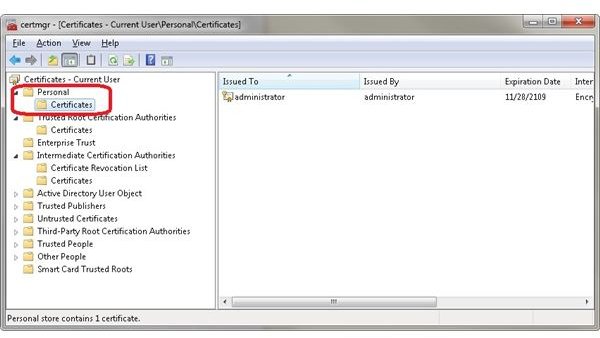
Personal Certificates
Personal certicates are important authentication markers. They are assigned by a certificate authority (CA) to a user. A CA is a third party operative that is trusted by users and organizations that are used to verify the matching of public keys of a user to an identity, such as the e-mail name, bank account, or other identification information.
Intermediate Certificates
An intermediate certificate lays between the server, or site certificate, and a root certificate. The intermediate certificate will complete the chain to a root certificate that is trusted by the security features of a browser.
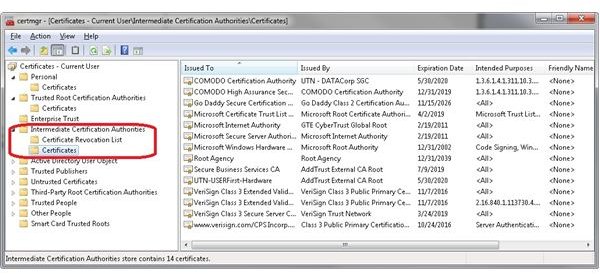
An intermediate certificate also means that you must take and complete an additional step in the installation process. This will enable your site certificate to be locked or chained to the trusted root; it will not display errors in the browser when someone visits your web site.
Root Certificates
In computer security as well as cryptography, a root certificate can be either an unsigned public key certificate or a self-signed certificate. Typically the root certificate meshes with the Root Certificate Authority.
A root certificate is also part of a public key infrastructure scheme. This means that a digital certificate is verified using the chain of trust. The trust anchor, or head of the chain is the Root Certificate Authority.
By the same token a public key acts like an electronic document that takes a digital signature and binds together the public key with a persons identity. Usually the information comes in the form of a person’s name or the name of an organization, their address, and other similar and relevant information. The certificate will verify that a public key belongs to an individual.
Summary
The Windows 7 Certificate Manager can be used to oversee the operation of several different certificates. They are issued by a Certificate Authority that offers the certs for different operations including personal, intermediate, and root.