Trojan Hunter 5 download is a fully functional software that you can try for 30-days. Give it a shot so you can test its real-time protection against Trojans and other types of malware.
Free Trojan Hunter 5 Download
Mischel Internet Security Ltd., a UK-based security company, provides anti-Trojan software, Trojan Hunter. The program is designed not only to detect Trojans, but also to completely remove them. Some antivirus software includes detection for Trojan horses but removal is often not complete. TrojanHunter compliments antivirus protection by accurately removing detected Trojans.
The program is available for home (single and family license, $39.95 and $59.95, respectively) and business users. A technician and site licenses are also available. The free TrojanHunter 5 download lets you use the program for 30-days and it’s fully functional (except removing detected Trojans). TrojanHunter 5 runs on Windows 2000, XP, Vista, and Windows 7 (32-bit and 64-bit).
Features and Performance of TrojanHunter 5
There’s plenty of features in TrojanHunter version 5 and we’ll list not only the key features but the bells and whistles that I find quite useful:

Key Features of TrojanHunter
- TrojanHunter Guard - Real-time protection module against Trojans and other types of malware . TH Guard sits in the notification area in Windows to monitor the computer for any Trojans and malware activity.
- TrojanHunter Scanner - The scanner module can be used to run manual, custom, full, quick and context menu scanning on files, folders, ini file, registry and active processes.
- Advanced Trojan Analyzer - An advanced scanning technology.
- Scheduler - Automatic updates and scan scheduler for the TrojanHunter program.
- LiveUpdate - Built-in product updater.
- Quarantine Manager - The safe storage of detected and removed Trojans from computers.
Extra features in TrojanHunter
-
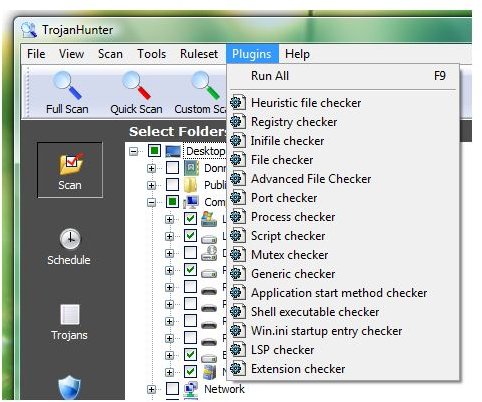
Plugins - Advanced scan plugins to manually check the system for malware or Trojans. It lets you run a quick check for Trojans on specific areas or settings in Windows:
 Advertisement
Advertisement -
Useful Tools - Process and Netstat Viewer, Autostart Explorer, Windows List, and Mem String.
-
Trojan List - The database of Trojan horses that TrojanHunter currently detects.
Advertisement
The performance of TrojanHunter to monitor and scan the computer is quite acceptable. No lag during a scan even if you are playing a full-screen PC game. TrojanHunter Guard only uses 7MB of memory and will use up to 70MB of memory during a full system scan. The scanning process is fast and it finished scanning the 250GB hard-disk in less than an hour. The scanner gave me a false detection on some legitimate and clean files, but the default setting of TrojanHunter is good. TrojanHunter will not automatically remove or clean detected Trojans or malware unless you change the settings to do so.
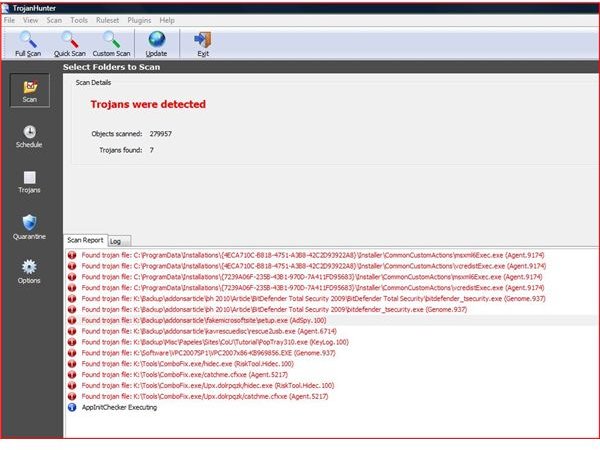
Note that the scan results in the above image are false positives except the selected item which is a misleading application that TrojanHunter correctly identified. The files TrojanHunter scanner has detected have been submitted to the vendor for corrections on the signatures.
The only minor issue that I noticed is that the TrojanHunter scanner program will not run if I open it via TrojanHunter Guard. The problem does not occur if I launch TH scanner from Quick Launch, desktop shortcut or from the All Programs menu.
Using TrojanHunter When Possible Trojans Are Found
If TrojanHunter finds possible Trojan files in your computer, it means the detection could be positive. Once you have access after the TrojanHunter 5 download, the program provides an option to submit the files without having to use an email program.
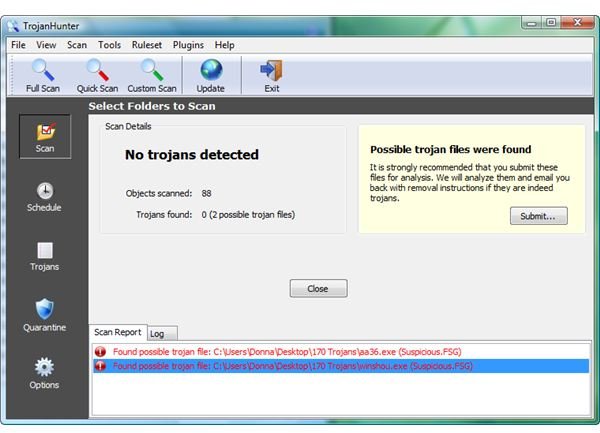
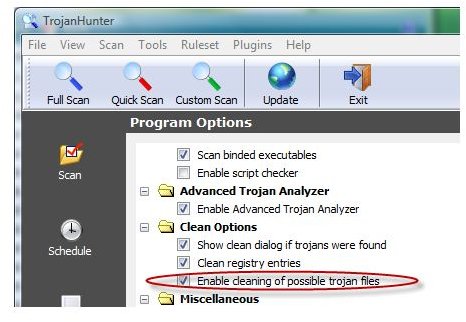
However, if you’ve configured TrojanHunter to clean possible Trojan files , the cleaning module will automatically quarantine the files.

It is recommended to keep the default settings if you are not familiar with the files detected as possible Trojan files. See “How Do Trojan Horses Work? ” to find out why Trojan files are not something you want in your computer.
You should also double-check the detection by submitting it for analysis so that the TrojanHunter malware research team will put in a Trojan or malware threat name the next time they update its definitions.
Screenshots taken by the author courtesy of Mischel Internet Security (https://www.trojanhunter.com )



