Comparison between DES, 3DES, AES and Blowfish (Data Encryption Algorithms)
Introduction
Computer encryption techniques have been divided into 2 categories, Symmetric and Asymmetric encrypting techniques.
In symmetric encryption technique, both sender and receiver use a shared key to encrypt and/or decrypt the data. The only problem with this technique is that if the key is known to others the entire conversation is compromised.
In asymmetric encryption technique, both sender and receiver use a separate key to encrypt and decrypt the data. For example, key 1 can only be used to encrypt the data, whereas, key 2 to decrypt the data. However, this technique is more prone to attacks as the sender and receiver continuously exchanges the key in order to encrypt or decrypt the data. Thus, we require a combination of both techniques in order to build a stronger encryption technique.
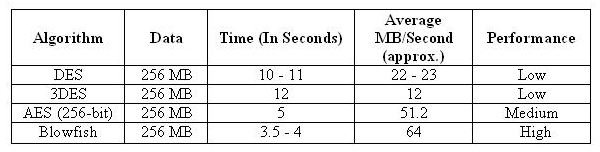
Various data encryption algorithms under comparison are DES (Data Encryption Standard), 3DES (Triple DES), AES (Advanced Encryption Standard) and Blowfish.
Data Encryption Standard was the first encryption technique based on the Lucifer algorithm proposed by IBM. Being the first encryption standard it had many defects and several exploits were discovered which made it very unsafe.
Triple DES is an enhancement to DES, which provided triple security in comparison to DES. The algorithm is same, only the encryption technique is applied thrice in order to increase the level of security.
Advanced Encryption Standard was proposed by National Institute of Standard and technology (NIST) in order to replace DES. The only known attack to AES is the brute force attack that allows an attacker to test combination of characters in order to break the security. However, Brute Force is not an easy job even for a super computer if the number of combination is arbitrarily high.
Blowfish is the most commonly used algorithm around the world, developed by Bruce Schneier, the president of Counterpane Systems, a firm that deals with cryptography and security. Blowfish is known to be the secret-key cipher that uses a variable number of bits ranging from 16 - 448 bits and encrypts the data 16 times to make it impossible for a hacker to decrypt it. Until now, no attack has been discovered to break the blowfish encryption. (B. Schneier)
Performance Comparison
As far as performance comparison is confirmed, AES and blowfish perform better in comparison to others.
For a data of about 256 MB, following were the results.
The performance of each algorithm depends on the configuration of the system used. These tests were conducted on P4 2.1 GHZ CPU running Windows XP SP1.
The above test clearly shows that Blowfish is the best of all, where the performance is very high. Also, AES had a high performance rate in comparison to DES and 3DES, and the throughput is almost 1/3rd of them.