You need file encryption online when you are storing your data on a remote server. You also need file encryption when you are sending mails. This article reviews the most used file encryption online techniques for data transfers and then reviews some online encryption services.
File Encryption Online – Need for Online Data Encryption
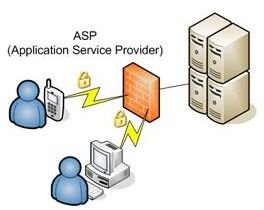
File encryption online is important when you are dealing with cloud storage or when transmitting data over a network/Internet to protect it from hackers and unauthorized people.
As the need for online storage becomes important, file encryption online also becomes important. You may ask why online storage! The answer is - backup, file sharing, and message sharing (even emails). When you send an email, it also has to go through several servers before it reaches the recipient. If you do not encrypt the email, someone snooping on your computer may interpret the email as soon as it leaves your computer.
In cases of a large file, you often store it online and send the link to others with whom you wish to share the file. Some examples of such online storage systems are MSN SkyDrive, Office Live WorkSpace, and Google Docs. As these cloud storages contain important files, these service providers provide some sort of encryption so that your data is safe from hackers and unauthorized people. Managed remote online storage services offering Software as a Service (SAAS) take care that they encrypt the data even before it leaves your computer. The best examples of such SAAS are Mozy and Idrive.
Though there are several encryption methods, most of remote storage providers offer you TLS or SSL encryption. Even banks and other online gaming sites involved in money transfer employ the same technique to protect your data. You know you are using “online encryption” when you see that the “http” in URL changes to “https.” Most of the time, you can also see a lock symbol against the URL or in the browser frame.
There are also some negatives to data encryption. The recipient needs to have the same software to decode the encrypted data and make it readable. Most of the email SAAS that offer encryption allow you to encrypt the data and create a password. When you send the email, these services store the encrypted email on their servers and send a message (with password) to the recipients. Recipients may use the link in the SAAS message in combination with the password to access the email. You will agree that this is a tedious process. We shall check out some free online encryption services on the next page that may prove beneficial to you.
In case of networks, sometimes it is possible that unauthorized people can access encrypted data packets. This is possible using a process that we call traffic analysis. The process studies the pattern of data packets and examines each in order to crack the encryption. Some software that help with traffic analysis are i2, Memex, Orion Scientific, and Visual Analytics. Wikipedia has a good article on cracking file encryption online using traffic analysis .
Before checking out the free online encryption services, let us take a bird’s eye look at SSL and TSL.
SSL and TLS - Most Used Methods on Free Online Encryption Services
.
Both Transport Layer Security (TLS) and Secure Sockets Layer (SSL) are cryptographic algorithms used in networks to protect data from authorized people. Though TLS offers greater security, several networks and file encryption online services employ SSL, as it is cheaper than TLS.
The TLS protocol allows communication without any fear of interception of data in transmission. TLS employs RSA level security with 1KB and 2KB bit strengths. On the contrary, the SSL uses only 128bit encryption in its third version. This is why it takes up less bandwidth and hence is cheaper to use by anyone – be it individuals or file encryption online services.
Free Online Encryption – Microsoft Windows Live SkyDrive
I have always looked for the best free online encryption services to store my backup such as employee records, etc. Researching for free encryption services, I also encountered some paid encryption services that claim to do better. However, they too are almost the same when it comes to encryption.
After much research on different free online encryption services, I now use MSN SkyDrive to share screenshots for dealing with issues on forums and to back up my downloaded music, etc. It offers free online encryption with 25 GB of free space. It employs SSL – on the fly. This means that as soon as you upload the files to Windows Live SkyDrive, they are encrypted. Similarly, when you select to download a file, the free file encryption online service decodes it and then lets you download it.
NOTE: Your data is NOT safe during the upload or download process at these sites! We have a Bright Hub article that sheds light on Microsoft Remote Storage Systems . I suggest you use some of the best free file encryption software to add safety even during transit**.**
Free Online Encryption: CRYPO
CRYPO employs different techniques to allow you encrypt your files and emails. The technique includes hashing. The online encryption technique of hashing means adding a certain number to the ASCII codes of characters in your files. While decrypting, the addition is removed to offer you the original characters. As the number is random, it becomes difficult for others to break the code.
CRYPO also offers URL hiding and Javascript encoding services in addition to mail encryption. Its mail encryption service works the same way as Comodo, which is explained below.
COMODO Email Encryption Service – Free Online Encryption for Emails
You must have heard of Comodo. It is one of the leading organizations that offers computer security software that include Comodo system cleaner , BoClean and much more. Comodo also offers free online encryption for emails with its digital signature software. It employs its own encryption technique for emails. You can download the software from their website. Once installed, you can send the email IDs for which you need the certificates. However, I am not truly satisfied with its email encryption feature. As discussed on the previous page, though it encrypts the email, recipients won’t be able to read it unless they too install the software. If the recipient does not have the software, Comodo sends a link for the email with a password to them so that they can read it on its server.
The plus side is that the file encryption online software is free. You may ask all your contacts to install it.
File Encryption Online Services - Conclusion
These are just some of the free online encryption services available on the Internet. However, I recommend the ones employing SSL so that others do not have to go through additional steps. For sending encrypted emails, I would recommend you get a SSL certificate from Verisign. For storing confidential data, use file encryption online services like Mozy that offers security even during the upload/download process. For use with free online encryption services that do not offer secure SAAS, you can always use any free file encryption software.