6 Top Computer Forensic Tools
Computer forensic is gaining popularity, why? The usage of computers is now directly proportional to the crimes related to computers. These crimes are termed as cyber-crime. Have you noticed that we have all started to depend on computers for a majority of work? Can you imagine a day without computers and internet? Let us see about computer forensics and the tools used to detect a cyber-crime.
Computer Forensics – What It Is?
According to Wikipedia, “Computer forensics is a branch of forensic science pertaining to legal evidence found in computers and digital storage media. Computer forensics is also known as digital forensics.” (Ref. Fig 1 – Computer Forensics)
Image Source: atp-p51
Fig 1 – Computer Forensics
Computer Forensics – Why It Is Used?
1. During legal proceedings, systems used by the defendants and litigants are analyzed using computer forensics tools.
2. When there is software or hardware failure, computer forensics tools is employed to recover lost data.
3. To understand how a computer works, to debug it and to for performance optimization, computer forensic tools are used.
4. When organizations want to terminate an employee, they gather evidence through computer forensics tools.
5. When the system is attacked by an intruder, computer forensics tools is used to analyze how the intruder or the attacker was able to break-in the system and what he did in the system.
Computer Forensics Tools:
As we now know what computer forensic is and why it is used, let us discuss about various computer forensic tools that are used to investigate computer crimes.
1. Disk imaging software: With the help of disk imaging software, contents of the hard drive as well as the structure of the files can be traced. Structure means file organization and the relationship between these files. Plenty of disk imaging software are available in the market.
2. Hashing tools: This tool is used to compare data present in the original and the copy of the hard disk. When comparing the data, hashing tools analyze the information present in both the original and the hard disk copy, assigns a unique number. When both the numbers match, it means no violation has been made else it is not a perfect copy.
3. File recovery programs: Is it possible to recover lost data? Yes, with the help of computer forensics, lost data can be recovered. There are file recovery programs; using these programs, it is possible to recover lost data. These programs search the computer for data that are not deleted but are marked to delete and recover the data.
4. Software and hardware write tools: Hard drive can be reconstructed bit by bit using these write tools. They don’t change the information present in the hard drive; they just make a copy of the hard drive.
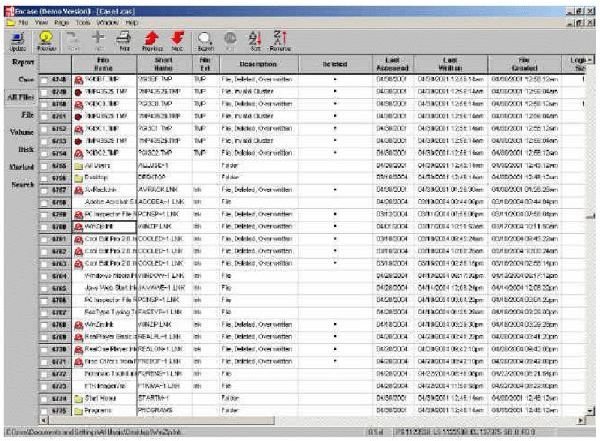
5. Encase: This is one of the most widely used commercial computer forensic tool from Guidance Software in the year 1998. With this tool, one can perform various tasks like disk imaging and verification and analysis of data. Have you heard of unallocated spaces? These spaces may contain valuable information in context with a cyber-crime investigation. With Encase, it is possible to inspect these unallocated spaces and collect the necessary data. (Ref. Fig 2 – Encase software)
Image Source: forensicfocus
Fig 2 – Encase software
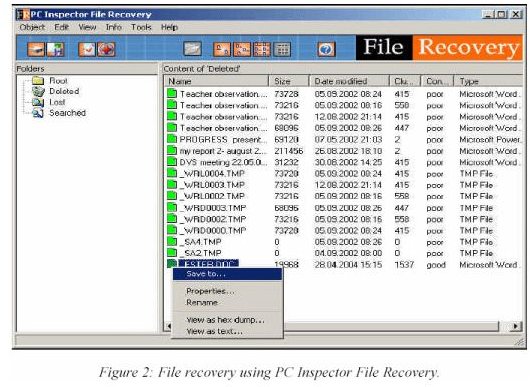
6. PC Inspector File Recovery: This is a free computer forensic tool from AccessData and helps in revealing and recovering the contents stored in any type of storage media that is connected with the computer even if the content is deleted. (Ref. Fig 3 – PC Inspector File Recovery)
Image Source: forensicfocus
Images
With the help of these computer forensic tools, analyzing a computer crime becomes easy. If a person wants to take up a career in computer forensics, he/she can take up certification tests available in this field.
