HijackThis is a free but powerful utility to inspect a system. It is not recommended to use by non-advanced users because it is not a malware scanner but a diagnostic utility with ability to remove unwanted files on a PC. Removing legitimate applications can cause damage instead of fix.
What is HijackThis?
Trend Micro HijackThis will inspect the settings in Windows and will display the browser and Windows settings after the scan. The scan results do not determine whether an item is bad or not. It is not recommended to delete anything using HijackThis without proper guidance. A scan using anti-spyware or anti-malware program is recommended instead of using HijackThis to remove malware. The download location of HijackThis is publicly available at Trend Micro website. You can download the installer version or standalone utility.
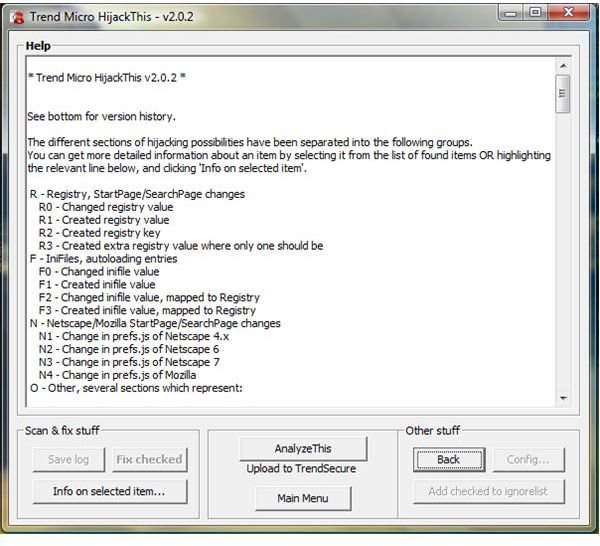
Another usage of HijackThis is to learn more the settings on your computer without using several tools. The help or info window in HijackThis is the first to check in determining each inspected group (see Figure A). And if you want to know more what detailed information of the inspected item is, you will highlight an entry before clicking the “
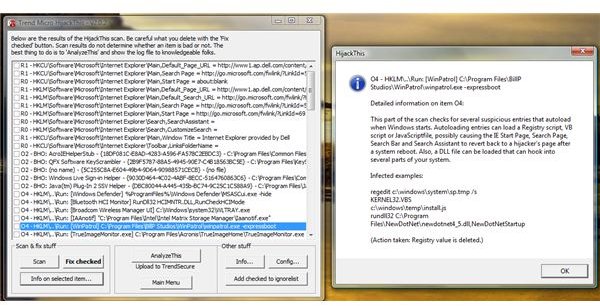
” box.
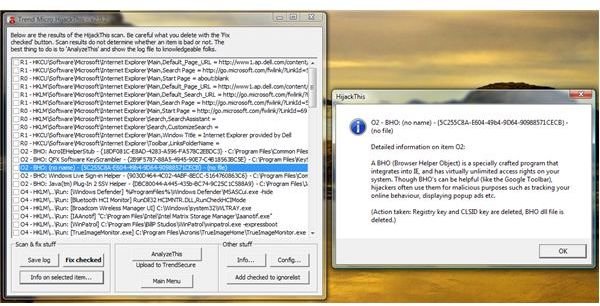
For detected items which do not have enough information (for example, no file or path of the application), it can be good or bad (see Figure B). To determine if the unknown item is good or not, you can go to SystemLookup website to find more information. If you have WinPatrol Plus , you can also use it to determine if the item is safe or not. If the SystemLookup shows it’s a legitimate and safe entry, you should see the status with green L. If it’s bad item, expect a red X. Red X means you have to run a scan using up-to-date anti-malware scanner. When you see a yellow O, the particular entry has questionable status. It means there are malware scanners that will detect it while others do not. It can also mean that the product have behaves or associated to a program that have privacy or security issue. Example of the product that has O status is here .
If you prefer to allow HijackThis analysts to analyze your log (for free!), let HijackThis generate a log in a notepad which you will copy and paste as your post in the HijackThis forum. The “AnalyzeThis” button will bring up the page that list many recommended HijackThis forum . When you click the “AnalyzeThis” button, the copy of your log is sent to Trend Micro for data collection so hit that button only if you wish to participate.
You can use HijackThis to remove remnants of a program you have removed or if a malware scanner failed to remove the remnants.
Options and Tools in HijackThis
HijackThis can be configured to create a backup before deleting entries. This is selected by default and it’s why it’s also recommended to run HijackThis in its own folder so all backups are in one location.
The safe entry in the scan window can be added in the Ignore List in HijackThis to prevent HijackThis in re-scanning again the particular entry. If there’s new item for the particular group (see Figure A), the new entry should appear in the HijackThis log. If a new version of HijackThis is released, you should allow it to re-scan everything by deleting the “ignore items”. Deleting the ignore items does not delete your application but will be removed only in the “ignore list” tab which HijackThis will display again after the scan.
HijackThis also provide other system utilities in managing Windows:
- Startup list log generator – to show the detail information of your startup items
- Process Manager – it is similar to the Task Manager in Windows. If your PC is infected and the malware disabled the Task Manager, you can use this option to manage the processes in Windows. It can also list the associated DLL files initiated by the particular process. Save the list in a notepad.
- HOSTS file manager – view or edit the Windows HOSTS file
- Delete file on reboot – If a file can’t be removed, you can use this option to delete the file when the system is restarted
- Delete a service – some malware will add itself as service to re-load itself whenever a user killed the processes or task. By using this option, the offending service will be deleted (use only if you know what you’re doing because there are many legitimate and important services in Windows)
- ADS Spy Utility - Scan the system for hidden Alternate Data Streams
- Uninstaller Manager – similar to Add/Remove Programs in Windows
Advanced HijackThis scan settings
HijackThis can be configured to calculate the MD5 checksums during the HijackThis scan or inspection. Calculating the MD5 checksum will help determine if the application on your computer is really what it reports. You will need to compare though the calculated checksum with the available version (earlier and newer) until you’ll see that it is not added by spyware.
Many PCs are infected everyday and it’s always recommended to have handy tools like HijackThis - but, in inexperienced hands, it can cause problems so be sure to use with care!