Examples of Network Security Diagrams: illustrating Common Security Methods
What is Network Security?
Life would be grand if we could all exchange information freely and never worry about any malicious intent, stealing or sabotaging of our information. However, we do not live in a perfect world, so we need to be concerned about the safety and security of any data we send across any network.
Since we rely more and more each day on the Internet to manage our bank accounts, our medical records, and our credit card payments, we need to protect this valuable information. This means we must turn to network security .
But what is it really?
The field of network security was conceived with the intent of designing security methods to protect our most valued assets from the continuing threat of cyber criminals.
When referring to network security, we are really referring to a three-dimensional solution; consisting of hardware, software and physical security methods used to combat any security threat. In particular, devices such as routers, IDS’s and firewalls are hardware devices used within a network to add security to all its users.
Anti-virus software and VPN’s are some of the software tools used to add additional protection for any network.
The most secure networks combine hardware, software and physical security methods together, offering the most protection to all users of any network. Let’s have a look at a few common tools utilized to secure modern networks.
Examples of Network Security
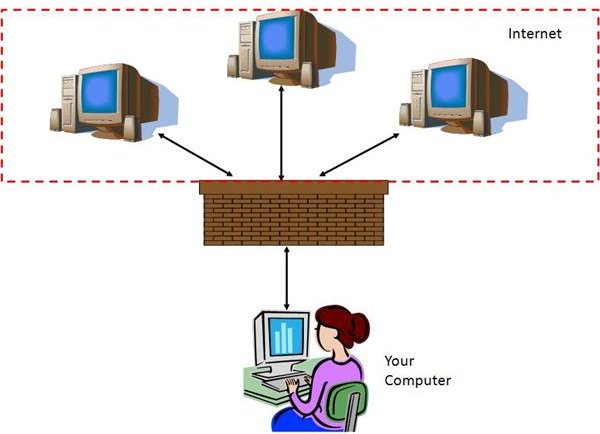
Firewalls:
One of the most basic and easily implemented methods of network security is the firewall. A firewall can be either software based, such is what is provided with Windows, or hardware based, such as a router. The basic idea behind a firewall is to allow authorized access to a computer while blocking unauthorized access. This is accomplished by configuring access conditions based on user defined rules, IP addresses, and port accessibility.
If you think of the original use of the term firewall, to keep a fire localized to a confined area, you will have the basic idea of the methodology behind a computer based firewall. It keeps your computer isolated from the outside world.
VPN’s: Virtual Private Networks
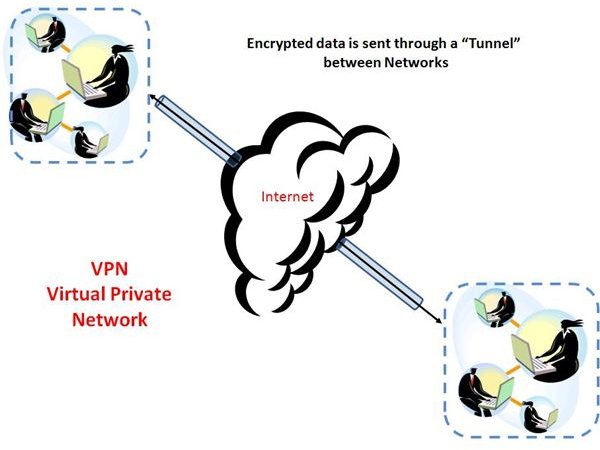
VPN’s are used to establish an encrypted connection across a network while using the Internet as its transmission medium. The benefit to this is two-fold. First, it’s inexpensive. Instead of installing additional equipment and services to create a secure connection between one place and another, a VPN uses the Internet, which is already in place. The second benefit to this is the fact that a secure data connection is established. VPN connection software encrypts the data being sent between one place and another. This is known as tunneling. It receives its name because of the idea of tunneling your data through the Internet while being encapsulated in an encryption “tube”.
IDS: Intrusion Detection System
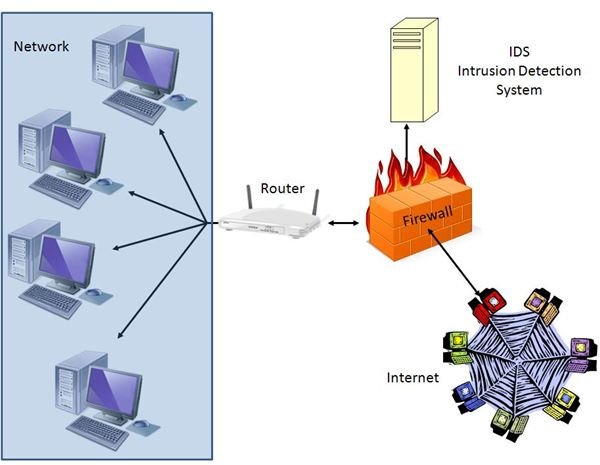
Intrusion Detection Systems consist of a combination of both hardware and software and work in conjunction with an existing firewall. IDS units are used to detect an intrusion threat to a computer system. IDS configurations use data analysis algorithms to compare data packet construction and frequency to established packet content definitions. If the packet construction observed does not match the packet construction expected, when compared to previously configured definitions, an alert is signified. Depending on the configuration of the IDS, the observed traffic is either blocked or let through to be marked for observation at a later date.
Securing Your Network
There are many types of security methods used to secure a network. Through the examples of network security diagrams, I hope to have provided a basic understanding of how some of these methods are intended to work. If you would like to obtain additional information about the basics of network security, I have included a link to another helpful article on network security basics.
Whatever method you decide to use, I hope you use caution and care when connected to or installing a network. Viruses, identity theft, CC fraud, and cyber crime are examples of threats that become possible once a computer is connected to a network. However, as we all know, a computer isn’t much good to us these days unless it is connected to a network of some sort.
Being vigilant and careful with whichever security method you choose to employ is of paramount importance. With all the security methods available to protect a network, the most important is user awareness. Make sure to be especially careful with whom you deal, what you say, and what access you provide your users.
References
- Diagram of IDS: Authors creation using Microsoft PowerPoint
- Authors own experience and knowledge
- Diagram of VPN: Authors creating using Microsoft PowerPoint
- Diagram of Firewall: Authors creation using Microsoft PowerPoint