Are we under attack? Hacking is alive and well and becoming ever more present in both government and private sectors. Who is responsible? How are they doing it? How bad is it? What can be done to stop it? These questions are being asked more frequently than ever before.
How Safe Are We?
With every moment that goes by someone, somewhere is somehow trying to commit cyberattacks. Don’t believe me? Let’s refer to excerpts from actual articles on information management and national security.
The FBI is always a valid source of information, at least for budding criminal threats. The Deputy Assistant Director of the Federal Bureau of Investigation (Cyber Division) seems to have a few concerns about the threat to national security stemming from cybercrime.
GovSec/FOSE Conference Washington, D.C. March 23, 2010
“…We as a nation are so vulnerable to this threat that, based upon my first hand knowledge in this area, I am convinced that given enough time, motivation, and funding, a determined adversary will always be able to penetrate a targeted system.”
We can also take a look at what the Department of Energy has to say about the cybercrime vulnerabilities of the US Power Grid.
According to a report from the Department of Energy’s inspector general , Gregory H. Friedman, “Security over the Nation’s power grid remains a critical area of concern. Recent testimony before Congress disclosed various issues, including the existence of significant vulnerabilities in the power grid’s infrastructure and many utilities that were not in compliance with the standards.”
Suddenly, I’m not feeling very safe.
Scareware Injection Attacks
Recently, injection attacks have been escalating at an alarming rate. In fact, Sarah Jacobsson Purewal, from PC Magazine had this to say in an article she wrote on April 1st, 2011.
“Hundreds of thousands – and possibly millions – of websites have been hit with a cyberattack that some are calling ‘one of the biggest mass-injection attacks we’ve ever seen.’”
The security company Websense discovered the LizaMoon attack on March 29, 2011. it is a massively expanding injection attack. The attack gets its name from the original domain of lizamoon.com. Websense also provides a list of all known websites that the LizaMoon attack has been used upon.
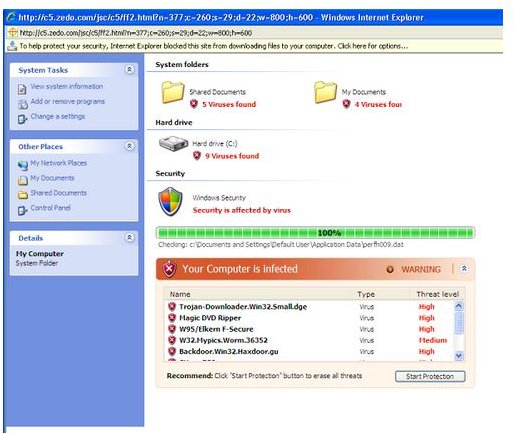
Injection attacks get their name from using the technique of injecting embedded code into a legitimate website, which when visited redirects the user to a rogue website which appears to perform a virus scan on your PC. Of course, this is fake. It’s only a Java script which mimics a real anti-virus program.
If the user decides to actually purchase, install and run this program claiming to solve all their non-existent security issues, then they have just been had. It’s a complete fraud, and the user has been robbed of their hard-earned money.
According to the Department of Justice (which is a pretty reliable source wouldn’t you agree?) cybercrime is alive and well. One example of cybercrimes being committed can be found here.
- Department of Justice Disrupts International Cybercrime Rings Distributing Scareware (June 22, 2011)
This document explains how two individuals were indicted for the installation of fraudulent security software known as “scareware.” This is basically malware that tells a user of a horrible virus that has been found on their machine, and that if they don’t buy this “anti-virus software” to fix this problem, horrible things will happen.
One of the methods of infection occurs when an individual visits a website which performs a fake computer virus scan on the PC, which then installs malicious onto the users PC. Once the software is installed, the computer locks up, and the user receives a barrage of pop-ups telling them that their computer has just been infected, and they must buy this “software” to correct the problem. If the software is purchased,“the problem” appears to be fixed and all is well, when in actuality the malicious software is just disabled, but still remains on the user’s machine.
If payment is not received, all files, folders and data on the PC become inaccessible. Wonderful.
What Does This Mean to Me?
Based on conclusions made on the data provided from known cyber attacks, a few things are made apparent.
It is clear that cyberattacks are occurring in both the government and private sectors. No one is safe. As long as you have a computer connected to the Internet, you are vulnerable to a cyberattack. A second observation, as the examples of both government and private attacks have revealed, is that cyberattacks can be both wide-spread and quite damaging. Another natural conclusion from reading the articles would be that the future will only bring new types of threats with varying levels of consequence.
But what does this mean?
Knowledge is king. Most successful attacks occur not because of their ability to go undetected, as most anti-virus programs work well at alerting the user of potential threats, but because of bad decision making on the user’s part. Be cautious. Awareness is the key.
It is important to understand that although security threats are a real possibility and will continually evolve, defenses against these threats are always evolving too. If you think of it as becoming an informed consumer, always looking for the most information you can get to make decisions, you will be well equipped to keep your computer safe. Also, getting into the habit of learning about the latest security threats, how to recognize them and what defenses are available to combat them will serve you well in the future.
What Can We Do?
As previously mentioned, most attacks on PCs are a result of the user’s own carelessness. I don’t mean that in a malicious way, but individuals need to be very vigilant when it comes to maintaining adequate malware protection. This is easily accomplished by allowing your anti-virus/malware software to perform automatic updates. This way, one doesn’t have to be bothered with remembering to perform regular software updates.
Also, being aware of what websites you surf is very important. Stick with websites you know are legitimate, but if it is not obvious, any good malware detection program, if set up correctly, will warn you of a website’s questionable legitimacy.
In addition, never download any software if you are unsure of its origin, content and legitimacy.
If you maintain an attitude of skepticism when surfing the Internet and downloading any software, most problems should be avoided.
When in doubt…don’t click it!
References
Sources:
Scareware Screenshot; Google Images, Licenced for Commercial Reuse
GovSec/FOSE Conference Washington, D.C. March 23, 2010
Sarah Jacobsson Purewal, from PC Magazine: Millions of Sites Hit with Mass-Injection Cyberattack , April 1, 2011