What I find truly amazing about Linux is the number of options it affords to do just about any task. The protocols available for copying files from one Linux server to another is another great example of its flexibility.
Linux File Transfer Options
Aspects to consider when choosing a file transfer method for a Linux server include:
Security – Most servers require some level of confidentiality when transferring files, along with a mechanism for authentication of both the user account and the machine to which the connection is being established.
Data Compression - Frequent large file transfers may require compression to save bandwidth, especially if those transfers are performed over a WAN (Wide Area Network) where the cost of bandwidth is at a premium.
Speed – Low overhead is essential. A large number of connections using a slow file transfer protocol can degrade server performance from a sprint to a crawl. So it is essential that an efficient protocol is used.
File transfer protocols supported by Linux are virtually endless. The most common protocols in use today include CIFS (Microsoft Windows file sharing) also known as SMBFS, NFS (Network File System), FTP (file transfer protocol), TFTP (Trivial File Transfer Protocol), HTTP (Hyper Text Transfer Protocol), HTTPS (same as HTTP but with Secure Socket Layer encryption), and SSH. With the exception of HTTPS and SSH, all of the protocols above transfer files without employing encryption (natively) and have security vulnerabilities that would rule out the protocol itself as a serious file transfer protocol option between Linux servers. While HTTPS does afford adequate security in the form of both encryption and client/server authentication, HTTPS does not natively support compression. This leaves only SSH which supports all three requirements listed above.
SSH - The Linux File Transfer Protocol of Choice
Most (but not all) Linux distributions include the SSH (Secure Shell) service by default. In addition to the security aspects above, SSH provides remote command line access, file copy and other operations such as XWindows forwarding and port forwarding. The most widely used SSH package for Linux is the freely available OpenSSH. OpenSSH sessions are secured using RSA based host authentication and Blowfish encryption (currently the most common default encryption settings) although other encryption and authentication methods are also supported.
How to Copy Files from Server to Server with SSH on the Command Line
The SCP command is typically employed to perform file copies through OpenSSH, although SFTP (secure FTP) is also supported. To copy a file from one Linux server to another, open a command line terminal and follow the example below:
scp /local_directory/local_file username@hostname_or_IP_address:~/remote_directory
or to copy a file from the remote Linux server to the local Linux server:
scp username@hostname_or_IP_address:/remote_directory/remote_file /local_directory
A few notes for clarification:
Local Directory – This refers to a directory on the local server.
Local File – A file, which will be copied from the local server to a remote server.
Username – The name of the account whose credentials will be used to login to the remote server.
Hostname – The DNS or hostname of the remote server.
Remote Directory – The destination directory on the remote server for the file to be copied.
Remote File – A file located on the remote server that will be copied to the local server.
Notice that SCP uses the simple “SCP From To” syntax to copy files. When you start an SSH session using either of the commands above, SSH will request the password for the account username issued in the command before the session is established and the file copy is completed.
How to Copy Files from Server to Server with SSH in XWindows
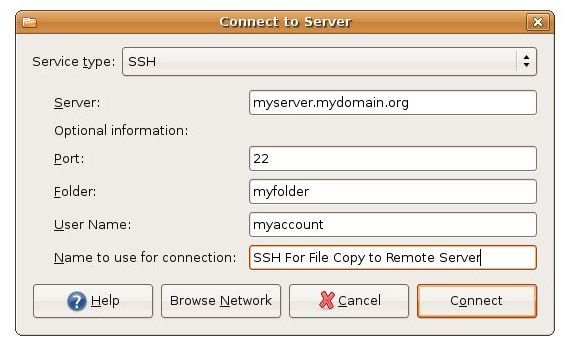
SSH sessions can also be established through XWindows for those that prefer a graphical interface (although not recommended for servers as XWindows poses a security risk). For example, in Ubuntu, an SSH session can be establish by clicking the Places menu typically located at the top of the desktop display, then Connect To Server. A window will open and present a list of options. First for Service Type select SSH, and then enter the URL or IP address of the destination server in the Server field. Usually leave the Port field blank so SSH will use the default port, which is 22. In the Folder field enter the directory path where you want to copy files to the remote server. In the User Name field type the name of the account that will be used to authenticate the SSH session. Next, enter a descriptive name for the session in the “Name to use for connection” field (to save the settings for future SSH sessions). Now, click Connect and enter the account password when requested and press Enter to establish the session that will open a window to the remote server directory enabling you to drag and drop files to the remote server as if the remote directory were local.

Troubleshooting Tips
OpenSSH has had a history of security issues that have been addressed in the most current release. So in order to ensure that your Linux server is secure, make sure the OpenSSH package stays up to date.
If you cannot establish an SSH connection and receive an error that states “Connection Reset”, confirm that the server firewall is not blocking SSH by issuing the following command:
iptables –list
which will list the current firewall rule set including whether or not SSH (on port 22) is accepted by the server host.
If you cannot establish an SSH connection and receive an error that states “Connect Refused” then check to confirm that the SSH service is running by issuing the following command:
netstat –anp | grep 22
If the above command returns back to the command line then you will need to confirm that SSH is installed, and that it is configured to run at startup.
For Further Information
Now that you know how to securely transfer files between Linux servers, you can find out more about how to use SSH, its feature set and configuration, by typing “man ssh” in the terminal and by visiting the OpenSSH web site.