Discover How Internet Traffic is Routed
Overview
How internet traffic is routed from one place to another is not a topic that can be explained in a few sentences. Let’s start with the basics.
“Transmission Control Protocol/Internet Protocol” or less formally “TCP/IP” is the process that defines how “packets of information” move from place to place (machine to machine) and which basically forms the backbone of internet traffic routing.
However, there are several flaws in the security of internet traffic routing, which allowed the online traffic to be hijacked, and routed via Chinese servers, for almost 18 minutes on April 8, 2009.
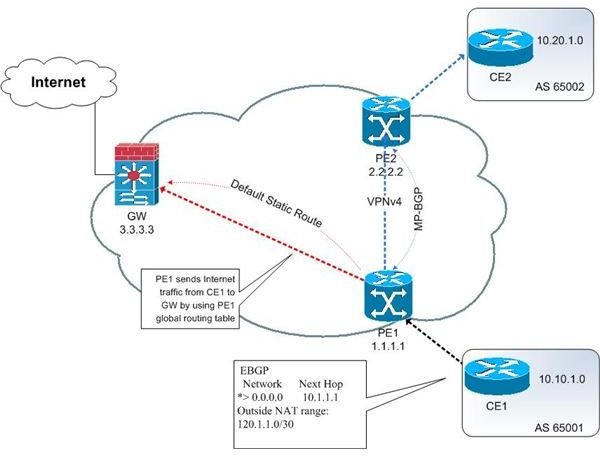
Image Credit: Cisco.com
Basic Rule of Internet Traffic Routing
A rule of thumb in internet traffic routing is that every router stores information about the routers electronically “near” to it. It always tries to send traffic to the router that is closest to the destination. In this game of passing-the-ball, information packets are routed from one place to other, and finally they reach the destination after several hops. Traffic routing is done on basis of trust of other networks, as a single service provider can never route traffic across the nation, let aside the possibility of doing it throughout the globe.
“Border Gateway Protocol” is used in the process of internet traffic routing. It causes internet routers to maintain a list or table of the other networks accessible (reachable) among autonomous systems. During packet transmission, a router consults this table to determine the path to the destination and the next router it should communicate with. This information is updated automatically.
Other protocols are used in the packet-switched networks that make up the internet, but when multiple service providers are involved in the process, the path that the packets take can become really odd. Let’s look at an example.
Illustration of Internet Traffic Routing: Hot Potato Routing
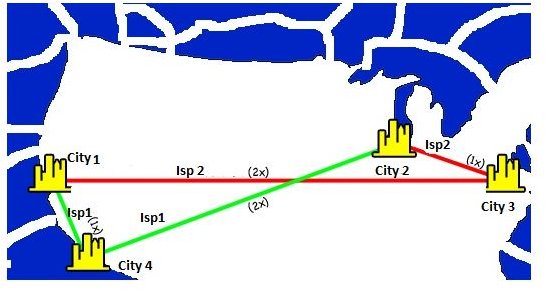
Let’s consider a hypothetical example with the help of diagram to the right, in which we’ve assigned each connection with an associated “cost” of 1x or 2x, and considered 2 ISPs (Internet service providers) routing traffic within 4 cities.
When you analyze how Internet traffic gets routed from City1 to City3 and City2 to City4, the most obvious path would be packet 1 getting routed directly from City1 to City3 on 2x link of ISP2, but in reality it gets routed from City3 to City2 on the 1x link of ISP1, and then travels through the ISP1’s network from City3 to City1.
This is referred to as “hot potato routing”, in which, each ISP tries to get packets out of their network at the earliest, smartly forcing someone else to bear the bill of shipping it across the border.
The bizarre thing is that both the ISPs end up paying lot more than the actual cost involved in sending packets directly to their destinations through their respective networks. And, the time taken in such form of routing is also higher.
The reason why routing in done is this fashion is because the internet is made up of autonomous interconnected systems. It’s impossible for first ISP to figure out what the second ISP is doing with packets, and vice versa. Ultimately each ISP is trying to get the other one to pick up more of the load.
Now, let’s see what happened on April 8, and how a significant portion of internet traffic was routed through one of the servers in China.
Traffic Routed to Chinese Servers on April 8
Well, it may be a tricky question to answer. Basically, before the traffic could be routed, the name servers (that are part of the Domain Name System that translates human-friendly terms like brighthub.com into numerical web addresses that computers understand) were hijacked. The major issue was the lack of security in Border Gateway Protocol due to which someone at an ISP reprogrammed a router, and it believed that a Chinese server was the closest router to reach the destination (and a reliable source to pass on the information packets).
The amazing thing is that lot of information in those packets had also originated from U.S. government and military sites, and there was a good possibility of the information being intercepted by the Chinese servers.
This wrong routing prevailed just for about 18 minutes, and far worse the redirected traffic even included commercial websites such as IBM, Microsoft, Dell, and Yahoo!
So, in short, traffic to and from sites was wrongly forced to believe that the best route to reach the destination was through the Chinese servers! This has been the center of criticism, serious worries, and calls to action to improve the security flaws in the working of Border Gateway Protocol, and the overall traffic routing system that caused this mishap. If this could happen once, then it can surely happen again, so it’s important to find out the root cause of the incident, and fix it for good.
For now we can just hope that such a thing doesn’t happen again, and the Internet traffic gets routed only through reliable routers, and doesn’t get intercepted on the way; we’ll keep you posted as and when more updates become available on this matter.
References
BV Software, LLC - A big secret to Internet traffic
Glyndŵr University - Internet Traffic Policies & Routing - (PowerPoint)
Washington Times - Report on Internet Traffic Routed via Chinese Servers