Best Home Network Applications You Can Find Online
We all know that despite broadband or cable packages being sold as x Mbit, we don’t always receive that bandwidth. It is also a known fact that some ISPs throttle certain traffic such as P2P, regardless of what you are sharing. It seems to be automatically assumed that any Bit Torrent traffic is illegal, even though many Linux distributions are downloaded by it, and even Blizzard’s World of Warcraft uses it for game patches.
There are a couple of tools available that allow you to check the health of your internet connection, whether your ISP throttles Bit Torrent traffic, and to help stop people snooping on you. While I certainly don’t advocate illegal file sharing, I do believe you should get what you pay for, and that includes your internet connection.
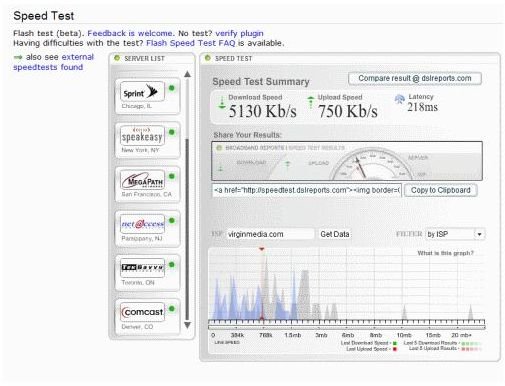
So let’s start with a health check on your connection. For that we will visit our friends over at DSLReports.com and run their Speed Test. It is one of the highest regarded bandwidth tests out there, so is a good indicator of the state of your connection.
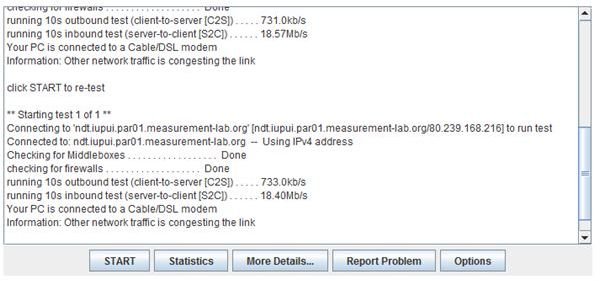
If you want more information on the state of your connection, the clever people at Measurement Lab have another tool that can check the wider network for congestion, throttling, and any other malaise that may affect your connection speeds.
To use it simply select a server nearest your home and click on it. Then click Start to run the test. It may take a few minutes, but will then return with the results.
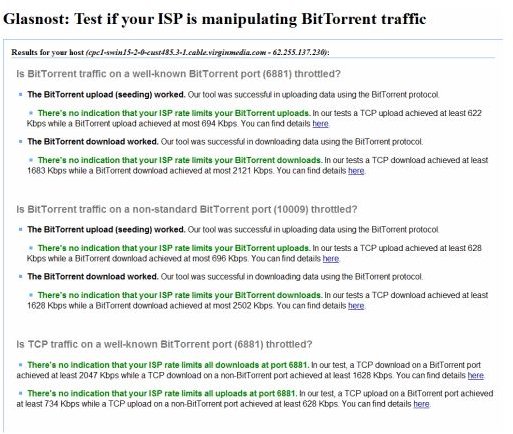
The last web-based tool we are going to look at is the Glasnost tool. This is a tool that simulates a Bit Torrent transfer while studying how the network handles the traffic. It can detect if the packets are being sniffed and throttled and has a good reputation for reliability. If like me, you use P2P networks for legal purposes, this is a good test to run to ensure you aren’t being penalized for how you use your connection.
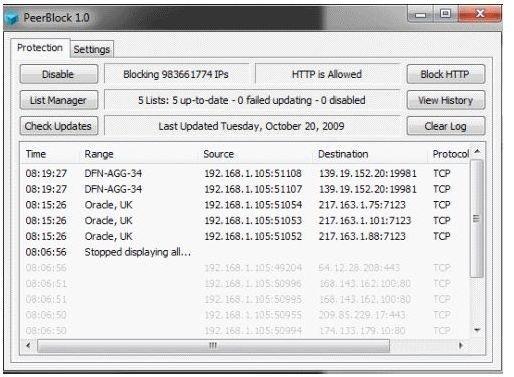
The last tool is PeerBlock. This is a reworking of the older PeerGuardian application which you could run, which prevents unwanted communications to and from your computer. These communications aren’t always the RIAA or an official organization, PeerBlock can also stop spyware and adware traffic from coming and going from your computer.
Even if you don’t use P2P networks, this is a useful tool to run on your PC. Best of all, it’s free. It works by using a database of known “bad” IP addresses and blocking traffic to and from your computer to them. The weakness of the system is that it is dependent on having accurate and up-to-date information to be worthwhile. There is also the option to completely block HTTP traffic, which is the main method spyware communicates with the outside world.
This method takes a little patience, just like when you train a new firewall, as your favorite sites will need to be manually permitted through the application. Try it, you will be amazed at how much communication goes on with your computer without you knowing it!