How can we protect ourselves from becoming a victim of phishing? What are available phishing detection tools? What are the phishing effects, if you have become a victim?
Phishing Detection
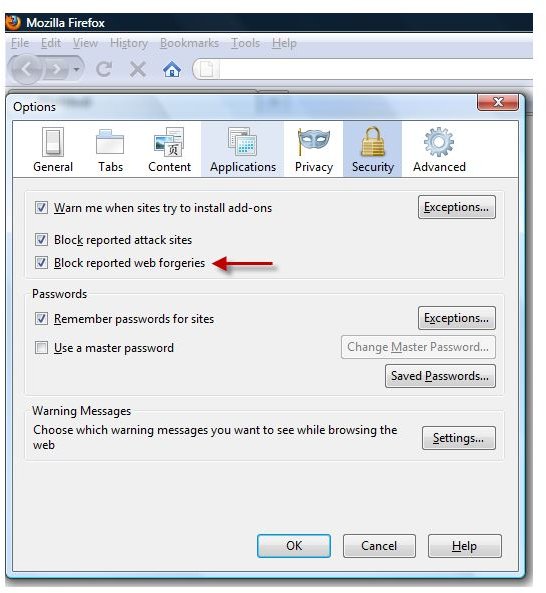
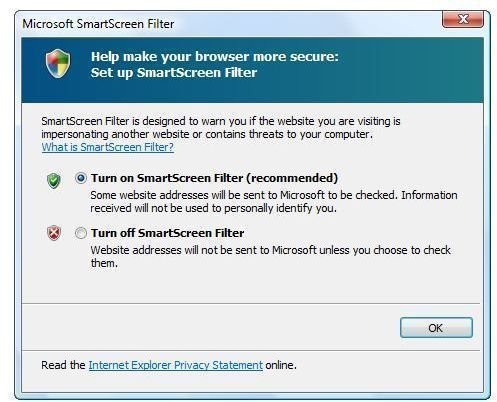
Detecting a fraudulent website or e-mail is done by enabling the protection offered in security software, browser or e-mail programs. Some antivirus programs provide protection against spam and phishing messages, while browser and e-mail programs will filter fraudulent messages by disabling potentially malicious links and images in the message.
Browser and E-mail Phishing Protections
The default Windows Mail program in Vista and Windows 7 includes definition files that are used to detect e-mail messages considered phishing or junk email. Microsoft Outlook also includes the same definition files to protect users viewing fraudulent messages. Microsoft releases an update for junk e-mail filters via the Microsoft Update website for XP and Windows Update application in Vista and Windows 7. Users may also download the definition files to protect against unwanted messages from the Microsoft Download center website . Third-party e-mail programs like Thunderbird also provide protection from phished e-mails.
Web browsers such as Internet Explorer, Opera, Firefox and Google Chrome include phishing detection and protection too. The anti-phishing protection in the browsers is enabled by default because there areso many people who have become victims of fraudulent websites and messages.
The vendors of email and browser software usually use anti-phishing tools to verify the sender and URLs if spoofed. Most of the vendors are using databases that they gathered from several sources such as Spamhaus, SURBL, SenderScore, etc.
Antivirus and Internet Security Suite Detects Phishing
Most antivirus software will block a phished webpage to protect their customers from viewing a webpage that trys to trick users into entering personal and confidential information such as credit cards, full name, mailing and e-mail addresses. However, not all antivirus programs provide protection against phished emails. Sometimes protection is only available in a commercial license of the antivirus software or in Internet security suite software.
It’s recommended to take advantage of phishing or spam protection in any software you use, especially if you are not an advanced-user able to identify a spoofed webpage or message. Even advanced-users can fall into phishing emails and webpages if they too are not looking closely enough before clicking a phished URL in a message or in a website. Web-searches on the Internet are also used by scammers to direct users to phishing websites. The antivirus program that has protection against phished sites or emails should be able to identify the bad links, and prevent users from visiting the page.
Phishing Effects
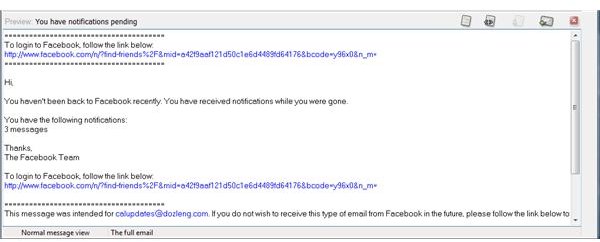
Phishing messages or websites have affected millions of people in the world. Most of them not only lose their money but also their identity. Scammers can also damage the reputation of the victims, if the unsuspected victim is not aware of the incident. In some cases, some people have lost their job because of phishing. Others lost their business contacts or friends after a scammer was able to access their login credentials to email or social networking accounts, because the scammer successfully annoyed everyone in the contact list.
User’s excuse of “Sorry, I’m a victim of phishing attacks!” may not be enough to bring back the trust that the business contacts or friends have given to them before. It’s like driving a car recklessly, because any account, services or device we use is our responsibility. We need to maintain and ensure proper security settings to prevent becoming a victim and also, to prevent affecting other people.
Image credit: Screenshot taken by the author.