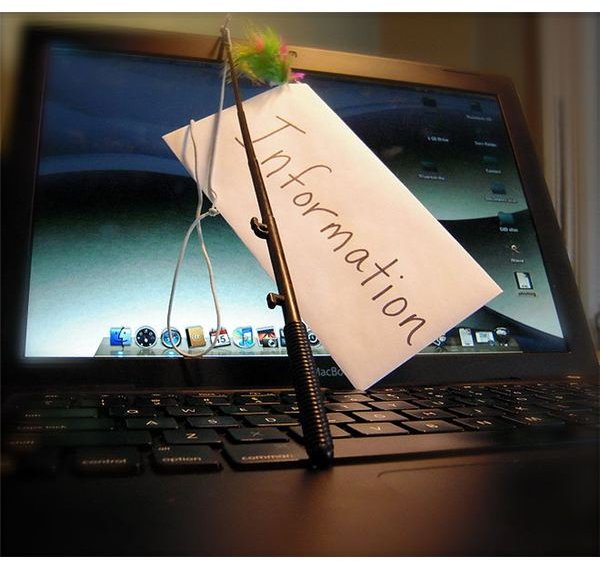
When it comes to cybercrime training, organizations like to rely on a plentiful approach to educate consumers. Cybercrime courses, blogs, podcasts and service bulletins are just some of the way the computer user can hone his skills against cyber attacks of various kinds.
What is Cybercrime?
Cybercrime training organizations fortify computer users against the threats defined by the Federal Bureau of Investigations. According to this entity, cybercrime cases include:
- Internet fraud
- Malware spread
- Child pornography
- Intellectual property theft
While this Cybercrime definition may appear to cover a large number of differing exploits, the facts show that these activities take place for the unjust enrichment of the perpetrators. This leads investigators and creators of cybercrime courses back to the basic methodology for empowering the consumer: determine who profits.
More often than not, this determination has the power to alert a consumer whether an email is a scam or a real notification. Case in point is the infamously famous Nigerian inheritance scam that promises countless riches in exchange for modest fees. Once the consumer takes the time to think through the proposal – and how the proposal got to him – it is pretty clear that a cybercrime is waiting to be committed.
Cybercrime Courses
As outlined in the enumeration of cybercrime facts above, not all cybercrimes are as quick and easy to spot. In fact, some malware, fraud and intellectual property theft approaches are so well crafted that the average consumer is more likely to be taken in by them than not. This is where cybercrime training organizations and their training materials come in to help.
McAfee Audio Parasitics: For ‘Geeks’
Known as “Computer Security’s Red Pill," (1) McAfee creates regular podcasts that feature lively discussions on all things having to do with malware, trends, and security industry insights. Consumers are entertained while being educated about the trends and issues that currently face computer security insiders. Already 85 episodes strong, recent highlights included the Microsoft and Adobe advisories or the dos and don’ts of computer security.
Cybercrime Training from Google: Interested Web Surfers
Not generally considered one of the major cybercrime training organizations, the Google online security blog(2) highlights monthly issues and problems as they occur. Coupled with its Browser Security Handbook(3), Google bloggers help the average web surfer with little to no technical background to understand the psychology behind cybercrimes, the setup of a scam, and also the means of delivery, depending on the browser the consumers relies on.
Microsoft: Internet Explorer Users
The online consumer who relies on Microsoft products for the daily internet experience will do well to check in with the Microsoft Security Response Center(4). Cybercrime training in blog form, occasional postings highlight configuration issues, Windows problems and the latest hack attacks that take aim at the software giant.
National Cyber Security Alliance: Parents, Educators and Small Businesses
Perhaps the most useful collection of cybercrime courses materials comes from the National Cyber Security Alliance via the Stay Safe Online site(5). Tackling also cyberbullying, computer protection and safe surfing practices, the site aims at educating the broadest audience possible about the dangers of cybercrime.
Sources
- McAfee. “Computer Security’s Red Pill ” (accessed April 25, 2010)
- Google Online Security. “Online Security Blog ” (accessed April 25, 2010)
- Google. “Browser Security Handbook ” (accessed April 25, 2010)
- Microsoft. “Security Response Center ” (accessed April 25, 2010)
- National Cyber Security Alliance. “Stay Safe Online ” (accessed April 25, 2010)


