Phishing Mac - Not Just a Windows Problem
Mac’s Security Features
Macintosh computers come with a secure configuration and built-in security features. Apple’s newest version of OS X, the operating system known as Snow Leopard, helps improve the security of Mac OS X as it automatically provides protection from PC viruses. Snow Leopard also includes a built-in anti-malware, but the Mac is not immune to security threats like phishing attacks.The OS software does help prevent against such attacks from anti-phishing features in Safari. This, however, is not a 100% solution to protect against phishing threats.
About Phishing
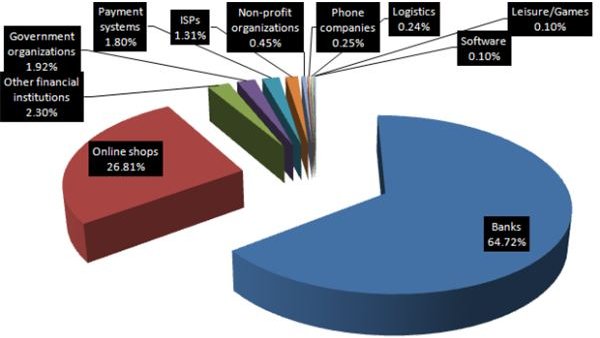
The term phishing refers to the extraction of information from some outsider (like an Internet hacker or site) trying to get to someone else’s personal information from a remote computer. It is a common attack (see phishing statistics) that continues to be an ongoing problem for Mac users. Phishing may take the form of a bogus e-mail request for users to reconfirm personal data. This may be a giveaway to what is really a phishing attack.
Phishing sites try to lure people to phony, fake Web sites. They are impersonators! Know that phishing scams can lead to identity theft.
If you have any doubt about such requests, do not respond. Use your gut instincts. If you are a victim of a phishing attack, some other party will be able to use your financial accounts fraudulently.
The right protection against phishing for Mac OS X is to use some kind of security software like VirusBarrier X6 (offers anti-phishing). It protects Macs from all known network-based threats, including phishing attacks.
Report phishing: Mac users can help other users avoid becoming victims of phishing scams by sending an email to phishing-report@us-cert.gov.
Security for Mac
Macintosh computers need some type of “Endpoint Security,” like McAfee Endpoint Protection for Mac, which provides anti-phishing protection for the system. “Safari also uses anti-phishing technology to protect you from fraudulent websites.” [1] Safari is Apple’s Web browser for Mac. It will give users a warning if they are trying to go to a known phishing site. Safari does however lack anti-phishing tools for Mac users. Therefore, to improve security for the Mac, it is better to go with either Firefox or Opera because these two browsers have built-in anti-phishing tools. Alternatively, there is OpenDNS–an Internet security and DNS service. “Millions rely on OpenDNS to track and protect against fraudulent phishing exploits.” [2]
Note: Mac users can always install some pop-up blocking software as well to help prevent phishing attacks. One such software is Pop-Up Zapper, a shareware application for Mac. It is able to Zap away most pop-up ads, which Mac users find useful not getting interrupted by annoying pop-up ads.
Advice:
-
Check Apple’s security updates page regularly (site: https://support.apple.com/kb/HT1222) for continuous protection.
-
Check SecureMac regularly for Mac security news.
-
Check periodically the Internet for potential phishing Web sites.
Security Alert: MacDefender (or Mac Defender) as well as Mac Guard, MacSecurity and MacProtector are phishing software–a security threat causing malware and a Trojan infection–meant to target computers running Apple’s Mac OS X. Apple has however updated the Mac OS X Snow Leopard systems to remove both threats.
Latest security news: The SecureMac team reported a new version of the BlackHole RAT 2.0 Trojan Horse for Mac OS X. Beware! This is a new threat that can remotely send a restart, shutdown or sleep command to the Mac. It can be detected by MacScan. A 30-day free trial of MacScan can be downloaded by visiting https://macscan.securemac.com/. Price: $29.99 (USD).
Check out the MacScan review. Do realize it can protect your security and privacy, as well as to detect, isolate, and remove spyware, keystroke loggers, and Trojan horses for Mac OS and Mac OS X. In short, MacScan will accommodate the anti-phishing tools needed by Mac users.
Although Mac OS X can reduce the risk of a security incident and additional security software can be installed, Macintosh users also need to be proactive and learn to protect themselves from phishing attacks that are taking place on the Internet. (See next section.)
How to Avoid Phishing
Here are some tips how Mac users can help themselves be on their guard not to reveal information to outsiders about their on-line activities.
Tips:
- Be suspicious of impersonal emails and links.
- Do not open “phishy” emails.
- Don’t click on unknown or untrustworthy links that ask for personal information.
- Only open email attachments when you know who is the sender.
- Scan all email attachments.
- Use a phishing filter, which are built into your Internet browser, to avoid suspicious or fraudulent sites.
- Only fill out on-line forms that are asking for personal information on secure Websites.
Advice: For more tips, Mac users should visit Anti-Phishing.info and/or AntiPhishingScams.com to learn how to stop and avoid phishing!
Image Credits: VirusBarrier X6 and Phishing Sites (as shown in images section)
Images (Credit: PandaLabs) - Possible Phishing Sites
Sources and References Section
[1] Why you’ll Love a MAC - Better OS: https://www.apple.com/why-mac/better-os/
[2] OpenDNS - Leading Anti-Fraud and Phishing Protection: https://www.opendns.com/features/phishing/
-
How to Spot Phishing: https://www.dummies.com/how-to/content/how-to-spot-phishing.html#glossary-phishing
-
How to recognize phishing e-mails: https://howto.cnet.com/8301-11310_39-10396786-285/how-to-recognize-phishing-e-mails/