How to Surf Anonymously: Get Lost in the Crowd
Want to surf anonymously? Perfect privacy on the World Wide Web is not possible, but it is possible to achieve a level of obfuscation that will prevent all but the most determined entities from tracking your Internet travels.
One way to obtain obfuscation comes from using a network called “Tor,” which is short for “The Onion Router.” Tor was originally designed by the US Naval Research Laboratory. Then it became a project of the Electronic Freedom Foundation. Now it’s sponsored by a non-profit organization called “The Tor Project.”
Onion routing relies on volunteers distributed throughout the world who donate server time to the Tor network. An important concept in Tor is that an Internet message is routed through the network in such a way that each server provides an anonymous outgoing connection. The next node in the network, therefore, does not know from which other node the packets (message) originated. Traffic within in the network is encrypted in transit. It’s only turned back into “clear text” at the point of departure, which is called the “exit node.”
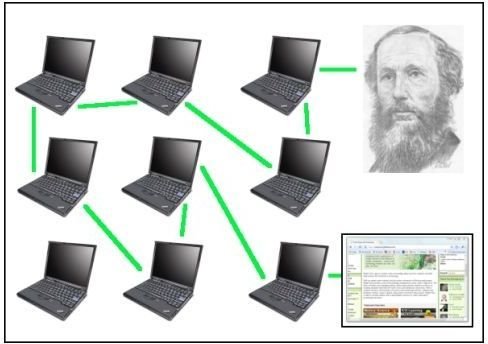
The image below shows a user, a network of servers, and the path, or “virtual circuit” that the user’s request for a web page goes through. The connections between the servers, in green, can also be thought of as “tunnels.”
Distributed Network
It’s called onion routing because the levels are like the layers of an onion. A message may originate on the surface layer. Imagine it going to the next layer as one might peel an onion. Each lower layer is not aware of where the message came from. Unless it’s an exit layer, the traffic that passes through stays secret and encrypted.
Traffic Analysis
Traffic analysis is a form of surveillance. It happens when an entity (an ISP, backbone provider, or government agency) performs “deep packet inspection.” A packet, in Internet terms, consists of a header and a body. The header describes where the packet is bound and the body contains your content – parts of a web page or an email. The header contains information about the data’s size, destination, and timing. Even if the data is encrypted, the header allows the inspectors to infer who is talking to whom over a public network. (1)
Tor works by hiding you among the many other users of the network. Interestingly, the more people who participate in Tor, the better the privacy becomes.
Using Tor in Windows
Tor for Windows comes in a bundle that includes a special, Tor-enabled version of Firefox. If you already use Firefox, it is still worth downloading the bundle rather than Tor by itself because it allows you to have one browser for regular surfing and another browser for hiding your tracks.
The downloaded file will extract to a folder called “Tor Browser.” In that folder will be an .exe file called “Start Tor Browser.”
Image

Clicking this causes the Vidalia Control Panel to appear. It showed a green progress bar labeled “Retrieving network status.”
Vidalia Control Panel

Vidalia promptly fussed about another instance of Firefox running (yes, and with about nine tabs open that contain pages I’m consulting for this article) and advised me to close that other instance. Hmm. Bookmark all in a new folder . . . Tor then exited when I clicked the notification dialog.
Okay. Start it again. Vidalia found the network much more quickly the second time, and I noticed a green onion icon in the system tray. A few seconds later, Firefox (the portable version) opened, and after a while, a page loaded that said, “Congratulations. You are using Tor.”
You Are Using Tor.

Hey, I’m surfing anonymously. Requests that I type into my browser are going to some anonymous server in the Tor network and being bounced around the world (who knows) before ending up at the web server – which thinks I’m coming in from somewhere else.
Well, I don’t know if I’d really call it “surfing.” It’s more like wading in the surf . . . or molasses. This is very slow. It took a little over eight minutes to load brighthub.com.
Back in the Vidalia Control Panel, I clicked “View the Network.”
Network Map
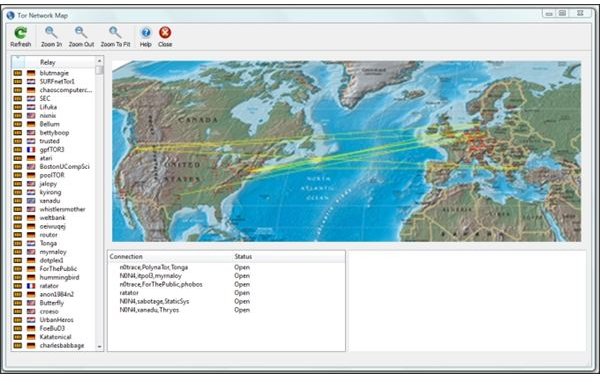
Soon after, I clicked “Help.” The help file informed me, “The network viewer lets you see relays in the Tor network and where your traffic is going.” No wonder it’s not quick. From the yellow trace on the map, I can see that my traffic crossed the Atlantic Ocean eight to ten times.
Of course, all I’m really doing at this point is surfing. To really get the best use from the Tor network, I’d need to set up my email and Instant Messaging clients to connect through Tor. And then there’s the host of applications on this machine that are constantly checking back with their mothership.
This is just the surface. True anonymity would require a lot of work.
Next we’ll look at those “anonymizer” websites. Do they work as well as Tor, and are they faster?
References:
1. Tor Overview
Other Articles by this Author
How to Download YouTube and Other Embedded Media Files in Firefox
Google Chrome Web Browser Security Features
How to Burn DivX and Xvid Media Files to DVD
The Calculator and the Scrapbook: Super Note-taker Evernote is Everywhere