The advantages of virtual private networks are many, but in this article we will take a break from looking at those advantages. Instead, we will look at some of the disadvantages of vpn tunneling.
When looking at the pros and cons of VPNs, it is quite easy to focus on the advantages that the VPN technology offers, because there are so many, but any objective look for a technological solution must also look its disadvantages. Fortunately, the cons of VPNs are significantly less than the pros. VPN solutions are well known for their flexibility and cost saving characteristics, but in this article we will take a look at some of its disadvantages, which include issues with security and performance.
Security Issues
One of the advantages of using a VPN is that it allows remote users to securely access the enterprise’s systems. Unfortunately, this also makes the network susceptible to security breaches. Often, a remote user will use unsecured assets, such as a personal laptop, to access the enterprise’s network. If this device has a virus or some other malicious software, it can compromise the network once the user has authenticated his access request and successfully logged on to the servers.
This form of network security threat is difficult for network administrators to manage, because there is a need to rely on the responsibility of the users to ensure that the network remains secure. This is challenging to do because the network access device is not under physical control of the network administrator. Whether or not an employee is given a device to be used exclusively for the company’s business, there can be no guarantee that the employee will do so.
Performance Issues
Leased lines or a dedicated data services can give an organization guaranteed bandwidth regardless of the traffic load on the network or the requirements of competing entities. In contrast, there can be no bandwidth guarantee on public networks unless elaborate resource sharing protocols such as MPLS are used. Ironically, the use of these protocols, in VPN solutions, tend to knock off a few performance points from the data connection’s bandwidth.
Though a properly installed VPN can prevent some of the performance issues associated with supporting multiple protocols and data transmission mediums, VPNs are only as fast as the slowest Internet connection between the two endpoints. In addition, most IP applications were designed for low-latency and high reliability network environments. This means that network performance issues will become more pronounced with the increasing use of real-time and interactive applications. While some applications can be reprogrammed or reconfigured to work with increased latency, getting this workaround to work with some applications can be challenging, if not impossible.
Similarly, it might be difficult to get VPN solutions from different providers to work with each other due to the different standards and protocols that may be in use. This should become less of an issue as service providers adopt more generally accepted standards and the industry becomes more mature.
Complexity
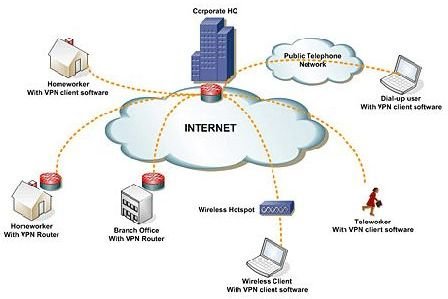
VPNs often use multiple network topologies, protocols, network hardware equipment and service providers to establish a single VPN tunnel. Using several data services providers can make a network more robust, but at the same time, trying to get several network components to work well together can only create complexity, especially if most of these components weren’t designed to work together.
In order to get a VPN to work well, an enterprise might need to employ additional network specialists to configure and administrate the network or acquire additional equipment; all of which may make the VPN solution more costly to implement and maintain.
Summary
VPNs offer several advantages to an enterprise. However, there is no doubt that there can be some security, performance, complexity and cost issues if the VPN solution is not installed and managed properly. Fortunately, the pros and cons of VPN are skewed to the positive side.