Security researchers recently found a potential breach in the system used to protect secure websites. We explain the problem, what internet firms are doing to rectify it, and what measures you should take to stay safe online.
What is SSL and what does it do?
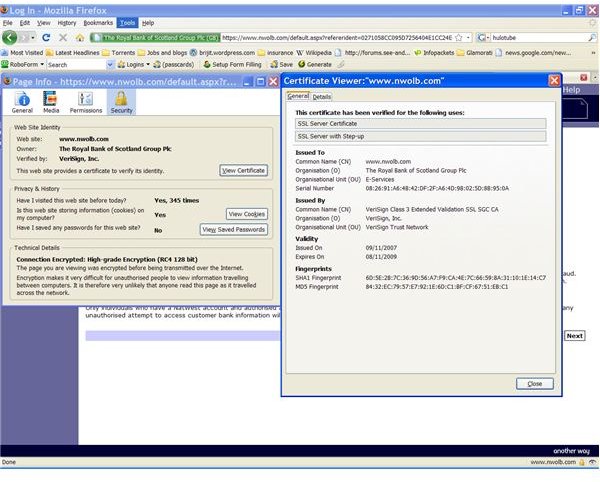
SSL stands for Secure Sockets Layer, one of the safeguards used to protect data sent to and from a secure webpage. These are the ones which begin with https:// rather than https:// and bring up a padlock symbol in the bottom-right corner of most web browsers.
SSL is used both to encrypt the data (put it into code) and to check that a page really does belong to the organization it claims. This is done through a third party firm (a certification authority) checking a digital certificate assigned to the site.
So what is the problem?
A team of security researchers have managed to forge a security certificate and have it verified by a certification authority. They said that, in principle, this false certificate could be used to make any website appear legitimate to a web browser.
How were the researchers able to breach SSL?
The researchers are keeping the precise details of their solution secret to avoid giving hackers too much information. However, the main problem they exploited is that some certification agencies use an outdated encryption system known as MD5.
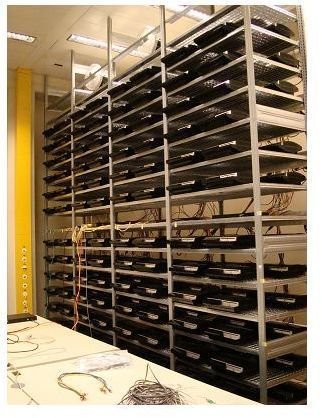
This system uses what is effectively a password of 32 letters or numbers. When the system was created in 1991, it seemed complex enough that hackers couldn’t efficiently figure out each password. However, with today’s increased computing power, that has proven possible: the researchers used a bank of 300 Playstation 3s to, put simply, try out every possible password until they found one that worked.
Could hackers take advantage of this problem?
If hackers were able to figure out the exact techniques used, they could theoretically take advantage of the weakness of the MD5 system. However, the computing power to do so effectively would require either spending a great deal of money buying machines, or would require the hackers to lease a large firm’s computer services (though it could be difficult to use them for such activity without being discovered).
Even if the hackers could produce their own bogus certificate, it would only be of any use if they found a way to redirect internet users to a fake website without being detected. This was possible in the past thanks to a flaw in the way website addresses (such as brighthub.com) are translated into IP numbers (which identify the particular computer where the site’s pages are physically stored). However, this flaw was fixed last year in a major industry-wide collaboration.
What is the industry doing in response?
Verisign, one of the firms criticized in media coverage of the researcher’s report, has now dropped the MD5 system completely (though it had planned to do so in a month). Along with most other firms, they have adopted the more modern system SHA-1. That system effectively uses a password which is more than 18 million trillion digits long. Even though computer power is constantly increasing, it doesn’t seem conceivable that SHA-1 could be cracked using the same method as the researchers used on MD5 – or at least, not in our lifetime.
Do I need to take extra precautions?
The news shouldn’t make any difference to the general principles of internet safety, which include:
- Never type confidential data into a page which doesn’t begin with https://.
- When visiting a site where you will be typing confidential data, always type the website address in directly rather than following a link from another website or in an e-mail.
- Never follow a link unless you are sure you know and trust the person or site which provided it.
- Always make sure your security software (such as an anti-virus scanner or firewall) is produced by a reputable firm and that you download and install any updates for the software.
Where can I find out more?
The full report by the researchers is available at https://www.win.tue.nl/hashclash/rogue-ca/ . Although there is some technical jargon and some complex processes are explained, the report is written clearly enough that people who are particularly interested in the subject should find it informative.
Images