Enabling Custom Level IE Security Settings
Enabling IE Custom Level Security
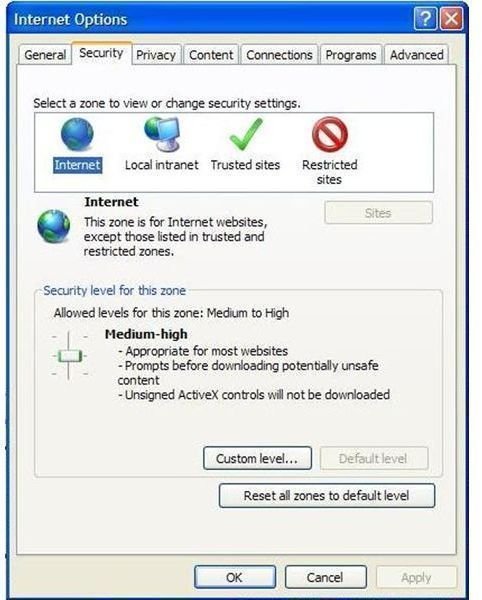
Accessing the IE security settings menu is easy. Open the browser window and click on:
- Tool
- Internet Options
- Security
At this screen the user may notice that ‘Custom Level’ on security settings is greyed out. Conversely, custom security levels may already be defined. Check the four IE security zones:
- Internet
- Local intranet
- Trusted sites
- Restricted sites
Set up varying levels of custom security. For example, the user may choose to select ‘high,’ medium,’ ‘medium-low’ or ‘low’ for a setting. He may choose to add sites to the safe or restricted list (or remove sites).
Custom Security Windows Setting: a Good Idea
IE security settings are the computer’s watchdog. When set at the highest levels possible, they prevent a good many hack attacks and worm or virus infestations. On the downside, the highest security settings make Internet surfing a bit of a chore.
Depending on the setting, constant prompting to solicit a user’s okay for accessing a site that might not meet the highest security certificate levels becomes laborious. This then leads to the greatest danger associated with enabling IE custom level security: the temptation to turn off IE enhanced security settings altogether.
Failing to Take Advantage of IE Enhanced Security
It goes without saying that a computer without proper security features set in place provides little to no security against malware. Learning how to configure security settings takes a bit of a learning curve and getting used to. This makes it an activity rarely undertaken by the average computer user.
As a result, default settings frequently remain in place. When they are changed, there is the risk of inadvertently minimizing a crucial security component to allow for a ‘quick fix’ to counteract frustrating user prompts. This makes custom level security a doubled-edged sword that may strike the user as much as the hacker.
Properly Configured IE Custom Level Security
Before the novice computer user decides to disable IE enhanced security configuration settings in favor of the default, it bears stating that custom level security’s benefits actually outweigh the risks – as long as it’s properly set up. As a general rule of thumb, the top four settings for enhanced– but still workable– Internet security involve ActiveX controls, navigation settings, and desktop installs.
- ActiveX controls are hackers’ vehicles for installing malware into a targeted computer’s operating system. The ideal security setting disables the option to “let previously unused ActiveX controls run without prompt." It is never wise to let computer processes take place without at least prompting the user ahead of time.
- Unsigned ActiveX controls should never be downloaded to a computer. Signed versions should only be downloaded after prompting the user. Set IE custom level security accordingly.
- Disable the setting that allows the user to “navigate Windows and frames across different domains.” Remember that user control is the ultimate weapon against hacker attacks and dubious websites with malware downloads. Never give up more control over the computer’s behavior than is absolutely necessary.
- Switch the security setting to issue a prompt before the ‘installation of desktop items.’ This hearkens back to the advice to not relinquish the power to approve of – or deny – the installation of an application on the user level.
Enabling IE custom level security is a good idea for any system, as long as the computer user is willing to undergo a minimum amount of training.