So far, our first recommendation to the users to defend themselves against malware was to turn on the automatic updates. Now, we will take a different approach and discuss how turning on the automatic updates may turn against you.
Introduction
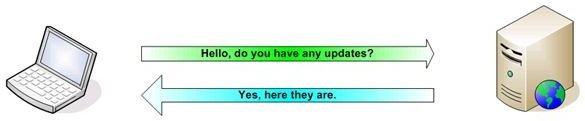
Every person who has even a basic knowledge on security turns on the automatic updates on his computer and recommends everyone to do it. Automatic updates download the latest security patches, bug fixes and other necessary updates from Microsoft’s website and install them to your computer. You may be asking what may be wrong with this picture. It’s very simple…
The Anatomy of the Attack: Ippon
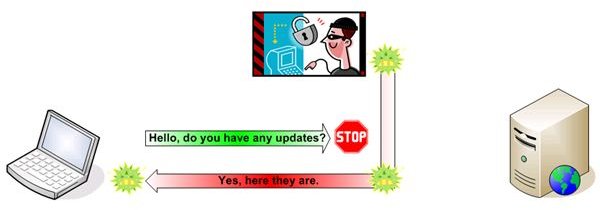
To be able to download updates you have to be connected to the Internet for sure. When your computer detects an Internet connection, it sends an update request to Microsoft and if there are any updates available, the server responds with the necessary information, such as KB (Knowledge Base) number, what it does, the update’s explanation, size etc.. What if someone intercepts this conversation?
When you are connected to the Internet from a public place, such as a café from a wireless connection, the attacker captures your computer’s request to the server and immediately sends the malicious code to your computer. Your system thinks that it has received a reply from the update site and it installs it, compromising itself.
Or, the second way is to send fake update information to the computers to provoke the software to start their update services and download the updates.
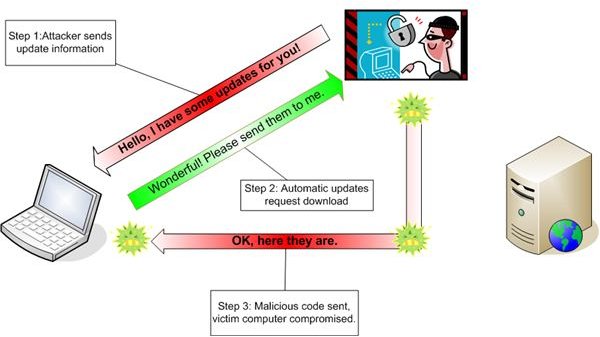
This exploit is called Ippon, which means “Game Over” in Japanese. It is announced just a couple of days ago in DefCon by Itzik Kotler and Tomer Bitton.
Are Windows Users Safe?
Are Windows users protected against such an attack? Microsoft used to be vulnerable to these types of attacks and they have fixed the security holes with KB 818529 and discussed a similar subject in Microsoft Security Bulletin MS06-014 . These two date back to 2004 - 2006 thereafter Microsoft began signing their updates. They might have patched (questionably) the vulnerability for the operating system but same holes are still there for the ActiveX controls. As far as the operating system updates are concerned, Microsoft updates are digitally signed and considered to be immune to spoofing. But the other programs installed on the system leave the computer vulnerable.
If you want more information on this subject, you can read this article about Automatic Patch-Based Exploit Generation.
Are Linux Users Safe?
Linux users are safe. The logic behind is not a standard Linux-Windows debate, but rather the “repository” concept of updating the software. A repository is a central pool that holds programs, utilities, operating system kernel, updates and everything related to the system. Linux software are tested based on diligence first and convenience second: for a program to be accepted to the official repository, it is checked many times, tested for security, stability and then passed on to the “testing” repository. After a long time of “testing”, if it is “clean and clear” it is allowed to the “stable” repository. All the mirror repositories are synchronized nightly with the main repository.
Now, for an attacker to inject malicious code to a Linux repository, he has to break into the management accounts to be able to place the code. Second, he has to break the repository keys, which are signatures of the repository. Then he has to infect all the mirror repositories, and he has to do it within a day, before the nightly synchronization is committed. This is theoretically achievable but not practically.
Free Open Source Software
Since open source software’s codes are open to the public, the code is reviewed by millions of eyes and a malicious code is very unlikely to escape from them and make its way to the repositories. On the contrary, closed-source systems like Windows and Mac OS are viewed by a limited number of “eyes”; if they don’t detect, then systems are more likely to be compromised.
What can Users Do About Ippon?
Personally I recommend a couple of things:
- In no case update your system from a wireless connection. Never. Ippon is most likely to be initiated in the wireless networks, because wireless networks do not require attacker’s physical access. You may be sitting in a café and the attacker could be sitting in the park.
- Don’t turn automatic updates off, but change it so that you are notified of the updates but you will decide when to install. Wait for a couple of days and if everything is clear, allow them to be installed.
- Disallow all the programs from updating themselves in the background. Adobe programs are notorious about this, they try to update themselves every single fraction of time.
- No matter which operating system you are using, stick with the open source software. See if there are any equivalents to your closed source programs, such as your office suite, e-mail program, download manager etc..
If you ask what is the technically safe way to avoid an Ippon attack, I have only one recipe: connect to the update site via a secure VPN.