Sniffing Data with Ettercap for Linux and Windows
What is Ettercap?
Ettercap is an application that can be used to wiretap networks. This tutorial is designed to test your own networks and see the packets of data that can contain critical data. While Ettercap was originally designed for Linux, Ettercap NG can be downloaded to Microsoft Windows.
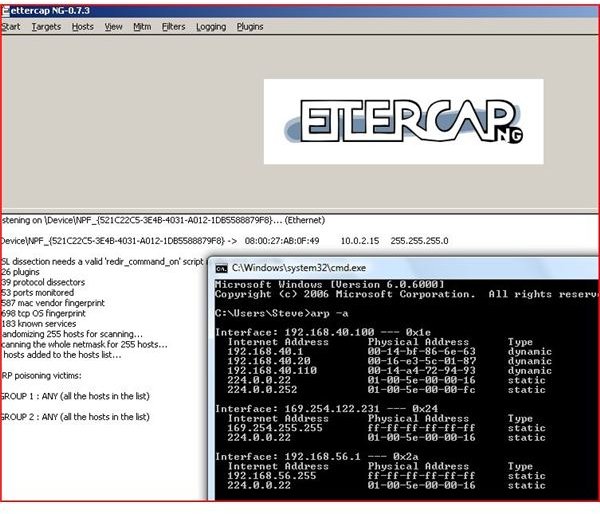
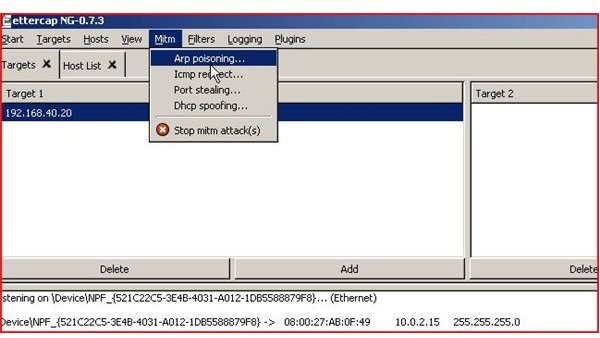
Ettercap NG is a suite of tools that performs a man in the middle attack on a local area network (LAN). This utility can be used for ARP poisoning and ARP Spoofing. What is ARP? Address Resolution Protocol is the process where your computer resolves the networking and contact information for a computer. Once you contact a computer on your local area network, an ARP entry is made. This entry resolves the IP (internet protocol) address of the computer to its MAC address. ARP posioning can tell a computer that it has contact with a legitimate computer when in reality, the computer is connected to a malicious computer.
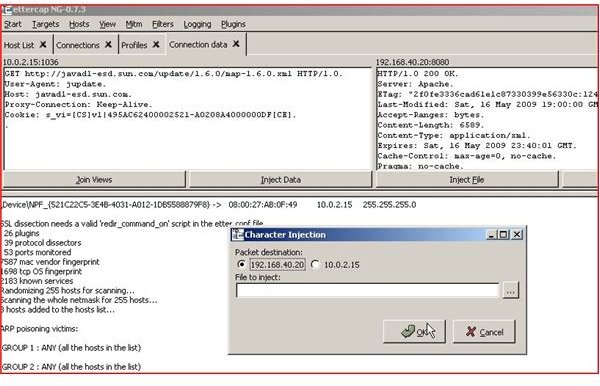
By performing man in the middle attacks, data can be intercepted and analyzed. Ettercap is powerful enough to capture SSL and SSH (secured ciphered protocols). By having these features, one can inject characters into a server’s application and keep the connection live (active).
With the capability to capture passwords on the following protocols, Ettercap can show you the weaknesses in your network. The protocols FTP, POP3, TELNET, SSH, MySQL, HTTP, IRC, ROUTING PROTOCOLS (RIP and BGP), SNMP, LDAP, VNC and others, are just a few that can be captured.
While this software can be used maliciously, it is a very needed tool for a system administrator. This application can be used to test current encryption standards being used on your local area network and test switches and routers for arp poisoning prevention.
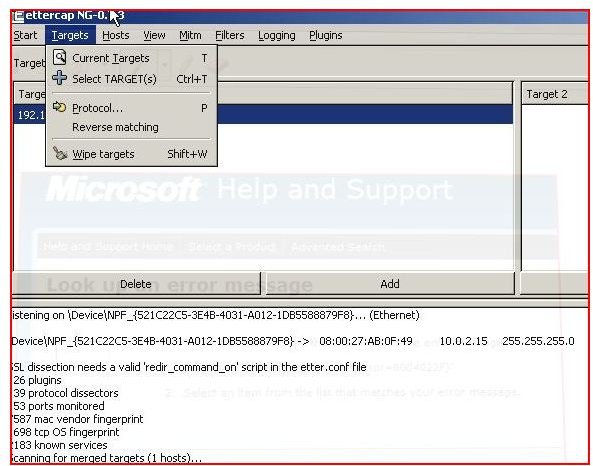
Using Ettercap is easy. Once an adapter is selected, the user can select hosts, scan the network, start sniffing and select a Man in the MIddle attack (MiTM). Data can then be viewed live, files can be injected if the other network device is not hardened and data can then be captured. Use caution when scanning a network and make sure you have permission.
Using Ettercap
Prevention
Using switches that have arp inspection features can help prevent arp poisoning. Also by using strong encryption (higher is better - yet your performance in applications may take a hit) strong passwords, session checksums, biometrics and multi - factored security can help prevent man in the middle attacks.
With these type of tools available publicly, administrators and security analyst should take great care in securing their network. Remember someone could be listening to and capturing your critical information.
If you enjoyed this article, be sure to check out Bright Hub’s Wireshark Sniffing, Ettercap Wifi Sniffing and WIFI WEP cracking tutorials!