Introduction to the Just Enough Security (JES) Method of Information Security - Part One Is An Overview Of The Program
Just Enough Security - An Overview
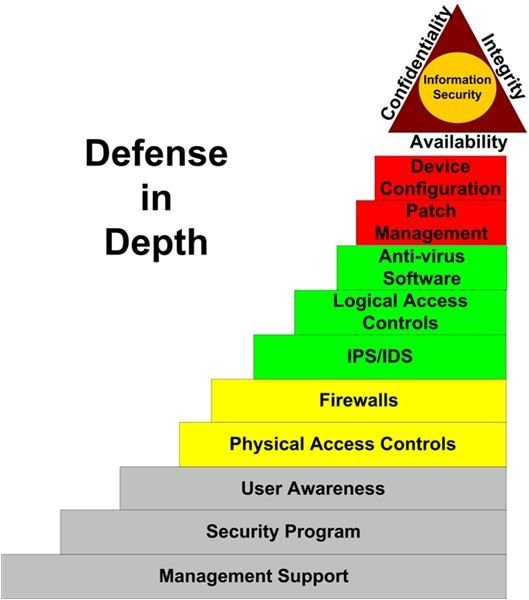
The Just Enough Security (JES) model is based on the premise that it takes layers of controls to effectively protect information assets. Also known as “defense-in-depth”, layered security takes on many forms. The JES model is my take on an approach for planning, implementing, and managing an organization’s Information Security effort. See Figure 1.
The objective of layered security is the implementation of a variety of controls, working in concert, neutralizing the efforts of threat agents. A threat agent attempting to compromise the confidentiality, integrity, or availability of a system protected by a layered security environment passes through several different tests before reaching its target. These layers comprise administrative, physical, and technical safeguards. To be truly effective, this model must extend to all company owned devices, whether located on the company network, at home, or at a customer site.
Is it necessary to implement all layers to ensure security? Not necessarily. That’s the point of JES. Which layers to implement, and to what extent, is a risk management decision. In other words, security controls should be applied to the point at which business risk is lowered to a level acceptable to management. No more, no less. In the following sections we look at each layer and how it fits into an overall security effort.
Management Support
The foundation of any security program is management support. Support should be comprised, at a minimum, of effective policies, adequate budgets, and consistent enforcement. Efforts to change user behavior and to implement security measures carry no weight unless there is visible executive support from all levels of management. Visible support isn’t just the hanging of a few posters around the lunch room. Effective support is evident in the project approval process, in the presence of a meaningful awareness program, and in how management deals with violations of security policy. It’s reinforced in management and employee meetings, memos, and if appropriate, the annual report. In other words, management support of information security should be manifested as a part of the organization’s culture.
Security Program
An organization’s security program defines and facilitates the security objectives of management. It consists of policies, procedures, standards, and guidelines. Policies are high level statements of management’s goals and objectives. They don’t provide step-by-step directions; such directions are provided by procedures. A policy should consist of at least three elements:
- Purpose
- Scope
- Compliance
The purpose of a policy clearly explains the objectives it’s intended to achieve. It should also reflect management’s commitment to a secure enterprise. Scope describes all enterprise technology and activities affected by the policy. Finally, compliance defines consequences if the policy is not followed. It’s the compliance piece - necessary to strongly encourage implementation - that’s often missing from security policies.
Procedures are the administrative, physical, and technical recipes for producing a secure enterprise. They’re derived from and support management policies. The step-by-step nature of procedures helps ensure consistent compliance with security policy.
Along with procedures that support security policies, standards and guidelines form the security handbook of an organization. Standards are mandatory configurations and approaches to technology implementation. Guidelines assist implementers and managers with issues that are not specifically covered by standards. Unlike standards, guidelines do not define mandatory outcomes, only outcomes for which “best effort” should be applied.
User Awareness
Unless fully engaged in the company’s security efforts, end-users can be an organization’s greatest threat. Continuous awareness training is the best way to obtain end-user participation in a security program. Training should include:
- Review of policies, standards, and guidelines
- Implementation and configuration procedures
- Password protection
- How to deal with social engineering attacks
- Proper protection of workstations
- Logging off before walking away from a device
- Use of systems by unauthorized users
- Elimination of potential shoulder surfing opportunities
- Proper handling of PDAs, laptops, cell phones, etc.
- Proper handling and disposition of media
- Backup tapes
- CD-ROM
- Floppy disks
- Other types of storage devices
User awareness begins with new hire orientation. Existing employees should receive training at least annually. In addition to formal training, daily reminders should be everywhere in the workplace. Posters and login messages are two good vehicles for reminder distribution. Managers should talk about security whenever appropriate during daily interaction with staff. Finally, first line managers must ensure that attention to security compliance is part of every operational task.
Physical Access Controls
The effectiveness of the security program is directly proportional to the effectiveness of the physical access controls surrounding information assets. Strong passwords, biometrics, and other logical access methods will not prevent the financial loss associated with theft or physical destruction of critical business systems. Further, the level of effort applied to extracting information from secure devices within the normal business environment will probably fall far short of the effort applied in a ciminal’s basement.
Physical access controls include locked doors, cable locks, and security personnel. Only IS personnel whose day-to-day duties require it should have physical access to the data center. Also, educating users on the proper physical control of laptops, PDAs, and other mobile devices is an important factor in the prevention of information loss or compromise. This includes immediate notification of the appropriate manager if a portable device is lost or stolen.
Firewalls
The term “firewall” was traditionally used to describe a barrier that prevented fires from spreading. In a network, a firewall serves a similar purpose; it protects an organization’s network from malware and other threat agents seeking to enter through connections with the Internet or other external networks. These connections are usually your network’s weakest points. Security personnel can also place a firewall at the entry point into each subnet containing your most critical information. This helps prevent threat agents already on your network from spreading to your mission critical systems. So what is a network firewall?
A network firewall is a collection of programs that protect the resources of a private network. These programs can reside on a dedicated device or on a server configured to act as a firewall. In either configuration, the firewall performs the same basic function; it inspects packets to determine if their content matches the criteria that allows traffic to pass to or from your internal or protected network.
IPS/IDS
There are two primary types of Intrusion Protection Systems (IPS) – network and host. Network-based IPS systems protect the entire network or a network segment. Host-based IPS systems reside on and protect individual systems. The same is true of Intrusion Detection Systems (IDS). The primary difference between IPS and IDS is how each reacts to a potential attack. An IDS device reports the attack so that a human can react. Once an IPS device detects an attack, however, it can react automatically based on business defined rules. Most devices today combine IPS and IDS.
In an ideal environment, malicious code and unauthorized users are always denied access to critical systems. Security controls in such an environment prevent authorized users from destabilizing their systems as well as the network. But who works in an ideal environment?
Host-based IPS is a layer of protection that attempts to “catch” activities not blocked by the layers lower in the JES model. These activities include, but are not limited to:
- Deleting files
- Moving files
- Copying files
- Installing executable files
- Registry modifications
- Denial of service processes
Network IPS looks at network traffic, attempting to recognize attack patterns and other anomalous behavior. Once a potential attack is identified, the IPS device can block traffic, shut down one or more services, or a number of other actions defined by policy.
Logical Access Controls
Logical (technical) access controls include hardware or software components that prevent either unauthorized users from gaining access to information resources or authorized users from gaining access to information for which they have no data owner authorization. Logical controls include passwords, biometrics, and tokens. Regardless of the controls used, they should:
- Have minimal impact on end-user productivity
- Be reliable
- Be effective with a ROI resulting from their initial and ongoing deployment costs
How logical controls are implemented is just as important as which controls are selected. The following is a list of guidelines.
- Relying on strong, easy to forget passwords may be a mistake for your organization. Strong passwords consist of upper case and lower case letters, numbers, and one or more special characters. Users often post strong passwords on their monitors or in other office locations that are less conspicuous but just as accessible. If you choose not to use strong passwords, make sure you look at compensating controls.
- Establishing an effective account policy is crucial to a logical access control implementation. The policy should include
- Automatic password expiration, usually 60 to 90 days
- A minimum password length, typically 6 to 8 characters
- Password history to ensure a password is not reused when it expires
- A threshold of login attempts that when exceeded locks the user account, usually set at 3
- A lockout duration that deters brute force attacks
Finally, it is a good idea to combine password controls with another access control, such as biometrics. This is known as two factor authentication. If a password is compromised, the second control will help stop unauthorized use of system resources.
Antivirus
Malicious code attacks are the most common type of penetration into a company’s internal network. According to the CSI/FBI 2005 Computer Crime and Security Survey (www.gocsi.com), almost 33% of business losses related to security incidents are from virus attacks.
Why, when 96% of the nearly 700 respondents to the survey have an antivirus solution in place, did virus attacks retain the number one position? One explanation is the theory that target organizations often incorrectly report denial of service attacks as virus attacks. Another cause may be the failure on the part of many organizations to maintain current virus signature files. Hundreds of new worms and viruses are released each month. Without a consistent effort to keep antivirus solutions current and operational, every connected end user device is a potential open door into your network. This is especially true of email systems.
Email has become one of the primary tools used by propagators of malware. Unsuspecting users opening attachments or distributing apparently harmless chain email can cause internal infections even on networks with strong perimeter controls. Make sure you’re aware of the types of attachments allowed to pass through your email system. For example, any type of executable file is a threat and should be stripped from a message before it’s delivered.
Another point of entry may be remote home devices. Unless an organization implements a remote access solution that checks for the presence of an operational and up-to-date antivirus package, it is opening a gaping hole in its security perimeter. New technologies, such as SSL VPN, provide the means to check for personal firewalls and antivirus applications before allowing a device access to internal resources.
But no matter how up-to-date an antivirus solution may be, there is always a delay between the time new malicious code is identified and when your software vendor provides an update.
Patch Management
Unless a system is properly patched, an attacker can take advantage of one or more of the many publicly known vulnerabilities. Organizations that delay the implementation of an effective patch management process may face increasing costs associated with attacks that exploit these weaknesses.
Patch management, as referenced in JES, is a set of policies, processes, and tools used to ensure that all systems are at the proper patch level. Processes include:
- Checking vendor resources for new patches
- Checking systems for current patch level
- Regularly testing and applying patches to operating systems, firmware, and business applications
These processes can be very time consuming and expensive if done manually. Many larger organizations are prime candidates for one of the many automated patch management solutions available today.
Device Configuration
Device configuration vulnerabilities are prime targets for malicious attacks. There are two primary paths to secure device configurations. First, customers must continue to apply pressure on software vendors to distribute applications in “secure mode”. In other words, when a business installs an application, it should install in a secure state. All services and add-ons that allow potential network or malicious code access to a system should be disabled by default.
The second path relies on the secure deployment of systems that may not yet support a secure state installation. This is known as “system hardening.” System hardening includes:
- Keeping business applications and operating systems at the most current version. This provides not only the ability to take advantage of new security features. It also ensures the availability of security patches.
- Ensuring all systems require appropriate authentication.
- Ensuring remote access for the purpose of administration or support is controlled by strong authentication methods.
- Disabling any service or port not required for the intended function of the system
- Controlling device configurations through the use of standard system images that are locked to prevent modification.
- Using the security features included in the operating system to restrict access to information.
- Ensuring systems are properly configured to perform backups.
Device configuration is one of the layers over which businesses have a great deal of control.
In Part 2, we put these layers together into an ongoing security process.
Tables and Figures (Hover for caption, click to enlarge)
Key Terms
Brute Force Attack - There are two types of password attacks: dictionary and brute force. In a dictionary attack, a cracker compares a list of dictionary words to each password. This is the fastest method, since most users invariably use common words found in the dictionary for their passwords. If a dictionary attack fails, a cracker will often try a brute force attack. In this type of attack, every letter, number, and special character combination is compared against the list of passwords. If given enough time, a brute force attack can crack almost any password.
Compensating Control - A compensating control is a process or technology that helps to make up for the lack of a primary control. For example, if your organization insists on assigning weak passwords to the local administrator accounts on your servers, a compensating control might be to implement much stricter controls on physical access to the data center. Since local accounts are used by someone actually standing at the server keyboard, imposing strong physical access restrictions can help reduce risk.
Firmware - Put simply, firmware is a program on an integrated circuit or “chip”. Many hardware devices contain firmware that performs tasks ranging from boot up activities to fundamental operating and housekeeping tasks.
Patch - A patch is a small fix to a program that corrects a problem. Security patches are regularly released by software and hardware vendors to eliminate newly discovered vulnerabilities in their products.
Personal Firewall - A personal firewall is an application that resides on and protects an end-user device from external threat agents. It operates in much the same way as a network class firewall.
Shoulder Surfing - When a person looks over another’s shoulder to see what keys she presses to enter her password, that’s shoulder surfing. Shoulder surfing is a term used to describe any activity whereby a person watches a user perform some action that may result in the unauthorized and unintentional revelation of confidential information.
SSL VPN - A VPN, or Virtual Private Network, is a secure connection between two points, usually at distant locations across the Internet. A VPN connection is often more secure than one with a device on the same internal network. The common method of implementing VPN is with IPSec (Internet Protocol Security). However, a new VPN technology is emerging based on SSL (Secure Sockets Layer). SSL uses certificates and public and private key encryption technology. SSL VPN brings more functionality to the network administrator and is usually much easier to implement than a traditional IPSec VPN implementation.
Token - A token is a physical object, usually about the size of a credit card, that identifies the person carrying it to a system or network. A token is typically used with a PIN.
Two Factor Authentication - There are three principle approaches to authenticating a user to a system or network. These approaches include the use of something you know, something you are, or something you have. An example of something you know is your password. Your fingerprint is an example of something you are. A token is an example of something you have. The use of any two of the three approaches is called two factor authentication.