A new book, titled Worm, seeks to give the complicated story of one of the biggest computer worms in existence. While Conficker is an interesting beast, it seems like it’s getting a whole lot of attention by people desperately wanting it to be a great villain.
The Conficker worm holds an interesting place in computer security history. It caused quite a fright when the much feared April 1st 2009 activation date rolled around, then slipped back into relative obscurity. A new book on the subjective, simply titled “Worm,” has raised the issue again by describing the Conficker incident as “The First Digital World War,” fought by a small group of security experts trying to get to the heart of the conspiracy.
As you may have guessed, that’s a fairly sensationalist version of events. So, what really happened?
A Strong Start
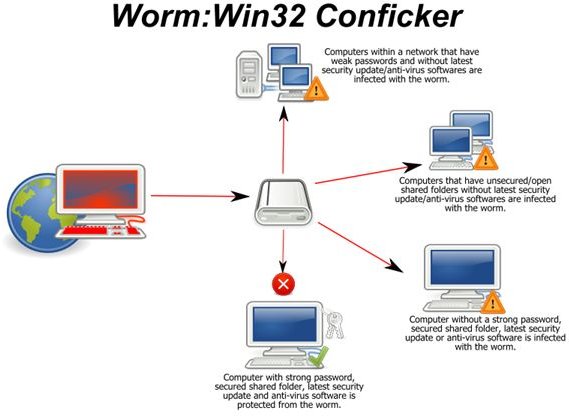
Conficker was first found in 2008 when it infected a number of honeypot networks. These networks are decoys that intentionally leave themselves open to malware to keep track of new variants and programs that are released into the wilds of the Internet. The program utilized an exploit present in the port used for file sharing and printer networking. Even if a user didn’t take advantage of these options in Windows, the options were turned on by default, leaving the hole in their system open.
Conficker was a bit worrying, primarily because of its odd behavior. It reproduced itself with great speed and without any input from the computer’s owner. This meant that if one weak link in the chain was infected, any other unprotected computer in the network would soon have it too. It could even automatically carry out dictionary password cracking to get onto locked accounts. The malware was heavily encrypted, using a new protocol that only a small upper echelon of the tech community knew about. The worm was also quite small, barely being larger than an average word document, and didn’t seem to have any explicit behaviors written into it, except for a few odd traits.
Every day, the Conficker worm would generate a long list of domain names in a somewhat random fashion. Amongst hundreds of decoys, there might be a domain that was either owned by the worm’s controller or infected and being used without the real owner’s knowledge. The worm would run down the list it created and check for updates. If it found one of the right domains in its list, then it could install updates and potentially take new orders.
Every day, Conficker would create a list of domain names that it would check for updates and new orders. Normally this would be a home run for the anti-virus group. Domain names can be monitored or shut down, and it would offer their first real lead. Unfortunately, by adding hundreds of innocent and apparently random domain names, and changing the list daily, the worm could find and download its updates long before investigators could see which domains were actually supplying the updates and take any action.
It was also a fairly resilient program, tending to hide itself well. It was designed to not only disable updates for standard security programs, but it actually patched the vulnerability that it used so that other lesser malware wouldn’t exploit it and raise suspicions. It even reset all of the system restore points to prevent a rollback. In short, it was a fairly hardy program.
The worst part, perhaps, was that it was deciphered that a major update, feared to be an “activation” code, was scheduled for April 1st, 2009 . Since millions of computers were believed to be infected, this could be a major disaster for users and networks around the world.
The Response
The book “Worm” deals heavily with the response phase, because it admittedly conjures up some fun images and a story that could be a decent movie. A small group of specialists formed what would come to be known as The Cabal. They were dedicated to finding weaknesses in the Conficker worm and hopefully figuring out a way to shut it down completely.
It’s important to note the one genuinely interesting aspect of Conficker. While many viruses are released into the Wild, it is rare that the creator will update their virus to counteract actions taken by security professionals trying to stop it. But Conficker was. It quickly patched a vulnerability in its encryption algorithm and took steps to actively counter The Cabal’s attempts at diagnosis.
For example, the easiest way to shut Conficker down was to investigate the domain names that it generated each day. The problem was that Conficker didn’t make the list until shortly before it checked, and the time of the check was based not on the easily changeable computer clock, but the clocks on major websites, like MSN.com and Google.com. This left no easy way to fool it into generating the list early. After the team found a complicated way to trick the worm, it started drowning them with larger lists that took too long to check, eventually reaching 50,000 domains.
Conficker really hit the news after a good old-fashioned bounty was offered by Microsoft in early 2009. $250,000 was offered for information leading to the arrest and conviction of the authors of the malware virus. This bounty remains unclaimed.
Doomsday Comes
After a lot of background work, April 1st, 2009 rolled around and there was a fair flurry of articles spurring on claims of a new Y2K. Since you’re reading this article, Conficker obviously hasn’t killed the Internet yet.
Very little happened on the activation day. A new algorithm was put into place that made the worm far harder to defeat, and a malware packet was downloaded by worms when they successfully contacted a live domain. The malware was incredibly simple, merely sending out lots of spam emails about a fake antivirus program. After two weeks this stopped.
The new update officially defeated The Cabal. It dropped the list of domain names technique for a more simple and elegant system of peer-to-peer communication. Updates for the worm would be released into the wild, and passed on through a daisy chain effect. This is effectively impossible to stop from a top-down perspective, so the great hunt was over.
After the big day, very little else happened. As of this moment, the Conficker worm is merely the creator of a fairly big botnet that appears to be doing nothing. The specialists that chased it for all this time warn that the first malware packet was merely a test to show that it was live, and that a major DDoS attack could happen at any moment (in short, all the computers could call a website or system at once and overload the server, forcing it to shut down).
The Real Threat
I’ll start off by noting that I don’t want to understate the potential danger. Malware in general is dangerous. You need to protect yourself. Keep your Windows patches up-to-date and watch for signs of infection. And yes, a botnet that numbers in the millions could be a big deal.
That said, a lot of paranoia was for nothing. “Worm” appears to really play up the stakes of the chase. While I’m thankful that anti-virus companies and hobbyists take the time to work on counter-malware technologies, this was not the plot to a Hollywood movie. It was a basic day at the office, and the malware writers finally figured out a way to win a minor victory in the end.
Botnets themselves are not “dangerous” in the sense of being a major threat to everyday life. Some of you may remember the campaign by Anonymous, in which several credit card and bank websites were targeted with DDoS attacks (the potential doomsday weapon for Conficker). Except they utilized far simpler tools that literally anyone could use. The sites were slow for a while and eventually shut down to ride out the attack. The world went on without missing much of a beat. Yes, they could theoretically use the botnet to target a major website and moderately inconvenience people. I’m sure that there are vulnerable payment processors that could be shut down for a day or so by an attack. It’s a one-shot deal though.
There’s a bit of a reason why botnets don’t like to make the news. As much as Conficker is described as some immortal monster, it’s always been fairly easy to diagnose and remove. The anti-virus company Sophos offer a fairly effective removal tool, and diagnosing the worm is usually as easy as looking at a simple “eye chart” which tests to see whether certain websites are being blocked. If it ever does anything big enough to make the news, it’s just a matter of education to clean it up.
This is quite evident in a recent Conficker infection at the Greater Manchester police station. An employee brought in a USB drive that was infected with the virus, and plugged it into a computer on the network. The virus spread, generated a lot of attention for itself and parts of the network had to shut down while the IT team cleaned it out. Nothing was lost, except the free time of some tech workers.
In the end, Conficker might send out some more spam and be an annoyance. It might even take down a website you really need to use when you really need to use it. In reality, the fears over Conficker probably caused more harm than it ever will. Scammers were quick to use the fear of the Conficker name to trick people into downloading fake virus scanners. Factor in the “boy who cried wolf” element and you’ve got a lot of damage. When botnets of a similar size gather thousands of personal pieces of information every day, and viruses exist that are designed to interrupt the operations of nuclear reactors, Conficker just seems a little overblown.
References
- A Battle Versus Whatever It Is (Worm Review), http://online.wsj.com/article/SB10001424053111903791504576589042730188586.html?mod=googlenews_wsj
- Antivirus Companies’ Worst Fears Realised as Conficker Does…Nothing, http://www.guardian.co.uk/technology/blog/2009/apr/01/conficker-worm-virus-april-effects
- Image Credit: Wikimedia Commons/Artem Karimov
- It’s Conficker Day, So Where’s the Meltdown - http://nakedsecurity.sophos.com/2009/03/31/conficker/
- Microsoft Offers $250,000 for the Head of Conficker Author, http://nakedsecurity.sophos.com/2009/02/12/microsoft-offers-250000-head-confickers-author/
- Conficker Removal Tools
- Conficker Outbreak at Greater Manchest Police, http://nakedsecurity.sophos.com/2010/02/02/conficker-virus-outbreak-greater-manchester-police/
- The Enemy Within (The Article Worm Expands Upon), http://www.theatlantic.com/magazine/archive/2010/06/the-enemy-within/8098/4/