Amazon’s Kindle Fire set the media alight with security and privacy concerns when it was announced. Much of the initial attention was focused on whether the Silk browser was performing a man-in-the-middle attack on its users. Amazon responded, but aspects of Silk’s architecture are still concerning.
Split-Browser Architecture
Amazon Silk, the Web browser on the Kindle Fire, uses a “split-browser” architecture. Unlike most Web browsers, Silk doesn’t just connect to a Web server and download a Web page to your device. Silk connects to Amazon’s servers instead of connecting to the website. Amazon’s servers download the Web page on your behalf, process it and send it to your Kindle Fire.
Amazon Web Services performs the grunt work that your device would normally perform. Amazon’s servers have more available bandwidth than your Kindle Fire’s connection and much greater processing power. Amazon’s cloud-computing service renders the page on Amazon’s servers and creates a small file that represents the page. The small file is sent to your Kindle Fire, which displays it as the Web page.
This architecture results in faster download speeds and rendering times on your Kindle Fire. The drawbacks are security and privacy concerns.
Encryption and Man-in-the-Middle Attacks
The initial problem with Amazon’s Silk browser and security was its approach to encrypted connections. When you connect to a secure website, such as your online-banking site or any website that collects your credit card number, your Web browser establishes a secure connection with the Web server. The secure connection is displayed as an URL starting with “https://” in your Web browser’s address bar. Web browsers also show lock icons for these SSL connections.
What’s Silk’s approach? According to the Silk FAQ, Amazon “will establish a secure connection from the cloud to the site owner on your behalf for page requests of sites using SSL.” Many websites and commentators took this to mean that Amazon would establish the connection to your bank and send the results to you. This would introduce an extra party into your secure transaction – no longer would the connection just between your Web browser and your bank. It’d be between your Web browser, Amazon and the bank.
In security terms, this was similar to a man-in-the-middle attack. Amazon clarified what Silk actually does on October 18, 2011. In a response to the Electronic Frontier Foundation, Amazon’s Jon Jenkins stated that “secure web page requests (SSL) are routed directly from the Kindle Fire to the origin server and do not pass through Amazon’s EC2 servers.”
If Amazon’s servers were compromised, only unencrypted traffic could be snooped on. Amazon, as a large online retailer, has experience and a strong record in security. Still, high-profile attacks in the past, including the attack on Sony’s PlayStation Network, have highlighted how vulnerable large corporations can be to security problems.
Privacy Concerns
Amazon’s servers log the Web addresses you visit, a token representing your browsing session, and your device’s IP and MAC addresses for 30 days. Amazon uses this data to troubleshoot its service and identify problems. Silk also caches parts of websites you visit on Silk’s servers, similar to how other Web browsers build a cache on your computer.
Amazon promises not to misuse this data and claims browsing history cannot be associated with an IP or MAC address. It could still be demanded by law enforcement or stolen by malicious hackers that gain access to Amazon’s systems. Silk only stores and caches personal data on Amazon’s servers when you use its split-browsing mode.
On the other hand, Amazon Silk can actually make your Web browsing more private. The traffic between your Kindle Fire and Amazon’s servers is encrypted, so you can use an open wireless network without other people snooping on your traffic.
A Solution
Amazon Silk includes an option that can disable the split-browser architecture and enable “off-cloud” mode for all websites. You can access this option on the first page of Silk’s settings menu. Silk functions as a traditional Web browser in this mode, connecting to websites, downloading content and rendering them entirely on your Kindle Fire.
Websites take longer to render in this mode because the Kindle Fire doesn’t have the performance Amazon’s servers do and because your Internet connection is likely not as fast as Amazon’s. Silk also uses off-cloud mode when Amazon’s servers aren’t available, so you can still browse on your Kindle Fire when Amazon’s servers are down.
The best solution may be to think twice before using Amazon Silk for anything that’s sensitive, yet not secure. You can enable “off-cloud” mode from the settings screen before doing anything you don’t want Amazon knowing about.
An Innovation? Think Again
While Silk’s split-browser architecture may seem like an innovation, Opera’s been doing something similar since 2005 with its Opera Mini browser. Opera Mini brings improved browsing speeds to cellphones with an architecture similar to Amazon Silk’s. Silk will likely offer greater performance advantages to Kindle Fire users, given that it’ll be rendering Web pages designed for computers. Opera Mini is already rendering slimmed-down pages for cellphones.
Opera Mini does route secure Web page requests through Opera’s servers. As the Opera Mini FAQ states, “If you do not trust Opera Software, make sure you do not use Opera Mini to enter any kind of sensitive information.” The same applies to Amazon Silk and Amazon when you’re not using a secure website. It’s not just a matter of trusting the company’s intentions; it’s trusting them to secure their systems.
References
- Electronic Frontier Foundation: EFF Gets Straight Privacy Answers From Amazon About New “Silk” Tablet Browser; https://www.eff.org/2011/october/amazon-fire%E2%80%99s-new-browser-puts-spotlight-privacy-trade-offs
- Amazon.com: Amazon Silk Terms & Conditions; http://www.amazon.com/gp/help/customer/display.html/?nodeId=200775270
- The Telegraph: Millions of Internet Users Hit by Massive Sony PlayStation Data Theft; http://www.telegraph.co.uk/technology/news/8475728/Millions-of-internet-users-hit-by-massive-Sony-PlayStation-data-theft.html
- Opera: Opera Mini FAQ; http://www.opera.com/mobile/help/faq/
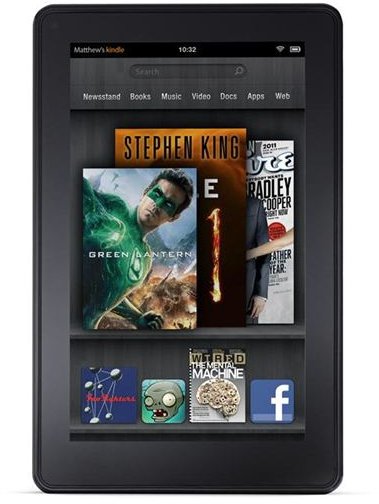
- Image copyright Amazon.com
- Amazon.com: Amazon Silk; http://www.amazon.com/gp/help/customer/display.html//ref=amb _link_357584342_3?ie=UTF8&nodeId=200775440&pf_rd_m=ATVPDKIKX0DER&pf_rd_s=center-21-0&pf_rd_r=1KFPCER73E2ZEW6GS26V&pf_rd_t=201&pf_rd_p=1321395082&pf_rd_i=B0051VVOB2