Don’t leave yourself open to online threats and rogue software. These can be the cause of data theft and even financial loss, which is a shame as you can easily protect yourself with a firewall.
Why You Need a Firewall
One of the most important pieces of software that you can have installed on your Windows, Mac or Linux computer is a firewall. Designed to protect your device and data from intrusion from the Internet and prevent software accessing networks without permission, firewalls are a key tool in securing your computer.
Understanding how a firewall works isn’t necessary, but it is useful to get some background as to how this type of software (or hardware) works, at the very least for you to understand the benefits of such an application.
Getting to grips with the basics of firewalls and debunking any myths that you might have encountered is also a good idea, just to give you a clear idea on what they can and cannot do.
- How Does a Firewall Work?
- The Benefits of a Firewall
- Firewall Basics: Separating the Truth From the Fiction
- Firewall Basics Part II: Ways to Stop Outside Intruders
- Firewall Basics Part III: The Pros and Cons of Firewall Methods
- A Beginner’s Guide to Firewalls: An Introduction
- A Beginner’s Guide to Firewalls: Packet Filtering Firewalls
- A Beginner’s Guide to Firewalls: Debunking the Top 5 Myths About Firewalls
Windows Firewall
As the most widely-used operating system in homes and offices around the world, Windows is a particular target for the people who create online threats and attempt data theft. As such the operating system features a built in firewall.
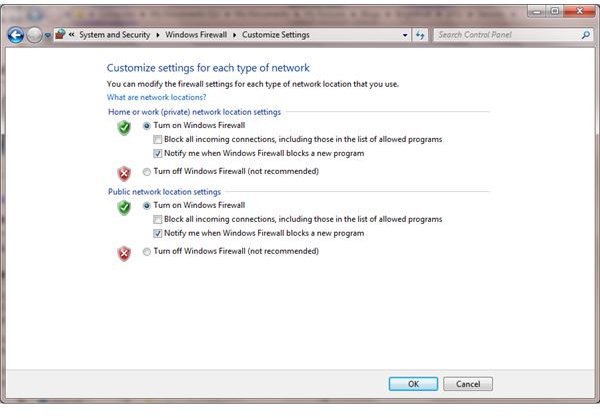
If you have read the guides listed above, the Windows Firewall should be pretty easy to use, and it is simply a matter of ticking boxes to enable or disable it. Should you discover that it is disabled or you have problems, however, then there is a pretty good chance that your Windows computer has an infection of some kind. In this case, you will need to run anti-virus software to establish the cause and type of malware, and then remove it.
- Help! How to Turn on Your Windows Firewall
- Fixing Windows Firewall Problems
- Turn Off Windows Firewall with Regedit
- How To Get the Most From Windows Firewall
- Help! My Windows Firewall is Disabled
Linux and Firewalls
Any computer that connects to the web needs a firewall, even a Linux machine. Thanks to the wider selection of Linux distributions and apps there is an increasing risk of intrusion onto even the most secure operating system, and the most common way of doing this is with the open source Iptables tool.
Note that some Linux distros such as Mandriva have their own firewalls; also note that with Linux you can setup your computer as an Internet gateway, which commonly features a firewall.
- Linux Iptables: An Introduction
- Managing Linux Firewalls with Iptables
- Linux Firewalls Made Easy With Fwbuilder
- Setting up an Internet Gateway Computer in Linux
- Configuring the Mandriva Firewall
Firewalls on Mac OS X
Even Mac OS X computers aren’t safe from Internet threats to such an extent that they don’t need a firewall. Like Windows, OS X features its own firewall software, something that rarely needs any configuration.
Should changes need to be made to the Mac OS X firewall, the user interface for this function is very easy to use. As with most security-related matters, if you don’t understand the risks, don’t access the firewall as you might accidentally disable it!
- Firewall Setup Guide for Mac OS X
- Guide To Internet Security For Macs
- Top Internet Security Software for Macs
- Secure Your Mac
- Configuring Mac Computer Privacy Options
Best Firewall Software for Windows
Although Microsoft builds its own firewall software into Windows, there are plenty of alternatives from standalone applications to vast Internet security suites. Some of these are free, while others are paid for, and all have their fans and evangelists.
Trying to establish which firewall software is best can ve tricky, so checking out some comparisons of the different firewall applications available will prove useful. There is also an alternative to software firewalls that you should consider: hardware firewalls
- Best Firewall: Software or Hardware?
- The Top 5 Standalone Firewall Solutions
- Top Free Firewalls for Windows 7
- Top Ten Firewalls 2010 - Comparison of Firewalls
- Who Offers the Most Effective Firewall Software?
- Comparison of Windows Firewalls
Hardware Firewalls
Coming in all shapes and sizes, hardware firewalls can either be single computers built to run as a firewall and nothing else or even part of a router or modem.
Whether building your own hardware firewall or taking advantage of the hidden functions on your router, a hardware firewall will allow you to directly control things such as port blocking as well as enabling you to setup a console from your computer to the firewall for easily accessing the device remotely to reconfigure it.
- Blocking Ports on a Firewall - Which and How?
- Do You Need to Know How to Turn Off Your Netgear Firewall?
- Choosing the Right Routers to Secure a Laptop
- How to Set Up an ADSL Modem/Router
- Network Security with T1 Firewall Routers
- Configuring Cisco Router Firewall via Command Prompt
- How To Disable a Firewall On a Linksys Router
- How To Build Your Own Firewall
Configuring and Testing Firewalls
Understanding about and installing a firewall is only half the job – this isn’t going to protect your computer on its own. Instead, you’re going to need to be able to correctly configure your firewall. The most complicated aspects of configuration are usually hidden away, only to be accessed via power users and administrator consoles, but being able to test your firewall and be aware of how to make it more secure while permitting the required access privileges of your software is vital.
- Keys to Effective Firewall Protection
- What You Need To Know About Firewall Leak Tests
- How To Make Your Firewall More Secure
- Removing a Firewall – How Do I Get Rid of My Firewall?
References
- Screenshot provided by author.
- All references from https://www.brighthub.com