Using Trend Micro Encryption Email for Windows, Windows Server, or Citrix Server
Sending an email without securing the message itself is like sharing a confidential or personal message with anyone who will bump into it. It can be read or tampered with without your knowledge. Companies are using digital signatures for their outgoing emails or newsletters so the recipient knows the message has come from them and has not been tampered during the delivery process. They also use a high-level privacy system by ensuring the messages and email attachments are sent with encryption.
The program, Trend Micro Encryption e-mail that will encrypt and digitally sign e-mails is free for personal use which means home users will be able to take advantage of the security and high-level of privacy that companies are using. The next sections of this article will describe Trend Micro email encryption installation instructions and how to use.
Simple to Use or Install
Program setup is quick and simple. The program will only require a valid email address to be protected and then validate the email address to start using the encryption tool:
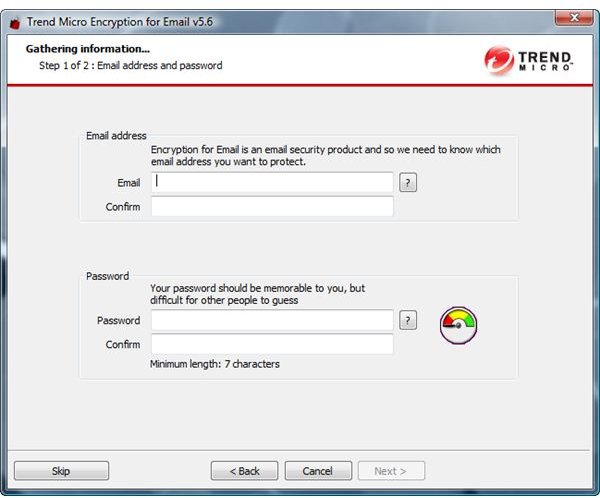
The tool will finish the installation by storing certificates to be used in signing and encrypting any messages using an email program or when sending messages using a browser:
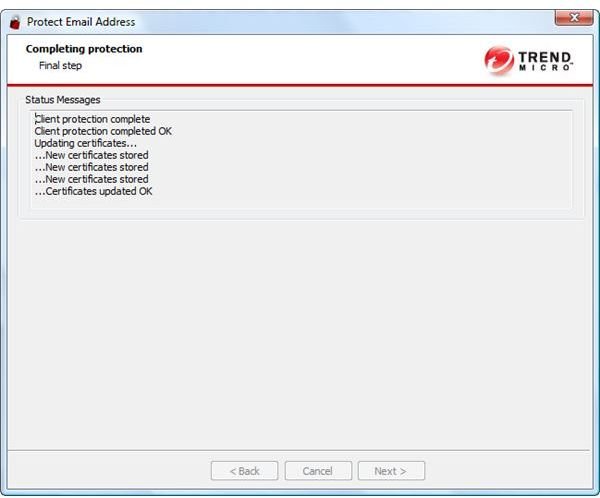
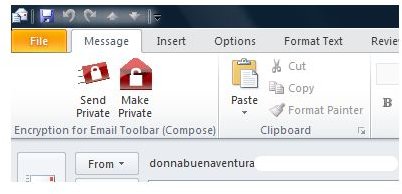
The end-user will be able to start sending secure and private email messages after the installation and after validating the protected email addresses:
Installation of Trend Micro email encryption on Citrix or Microsoft servers is recommended for business users. The above is for client or home computers using Trend Micro Email Encryption Service, which is free for personal use. A trial of 30-days is an option for a business or company.
Web-based Email and Digitally Signed Messages
The program will run on Windows Vista, XP and Windows 2000. It also supports email and browser programs such as Internet Explorer, Firefox, Thunderbird, Windows Live Mail and Microsoft Outlook. By installing the plugin for Windows, end-user will be able to digitally sign any message when using email program or when sending email messages using web-based email programs in a browser. Below is an example of digitally signed email message when using Internet Explorer and Windows Live Hotmail account:
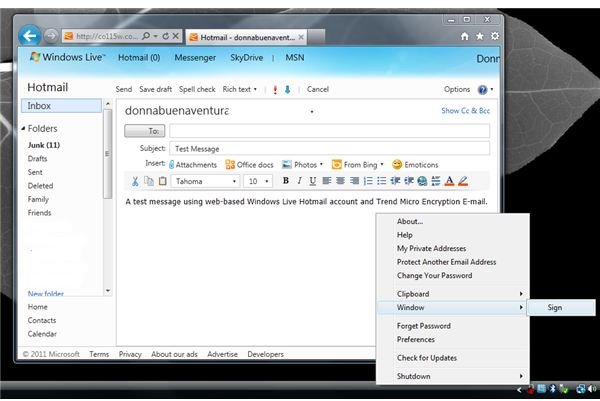
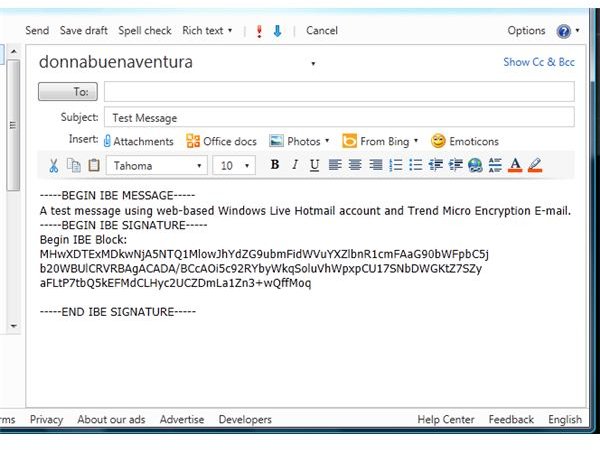
It’s simple to use since the tray icon of the encryption tool is available with handy command to sign the highlighted email message in the browser. Email messages to be sent using an email program can simply click the “Send private” or “Make private” buttons in the toolbar of the email client to start sending an encrypted or digitally signed email message.
The plugin by Trend Micro will install add-ons for Firefox and Internet Explorer in addition to updating the certificates to be use in sending a secure message or adding a digital signature when using Windows applications.
Encrypted Message
When an email message is encrypted using the tool by Trend Micro, the recipient will be able to view the message as private post:
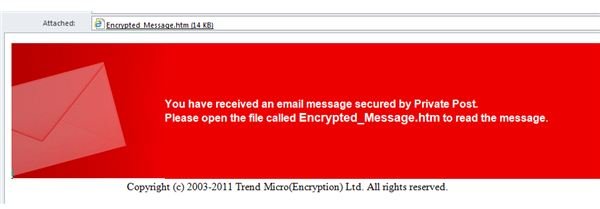
The recipients need not to install any software to their PC to view the message because the Trend Micro online message viewer will open the default browser to view the private or secure message. This method of sending email message to contacts will ensure that the message was not tampered or viewed by other people.
Options
Trend Micro encryption email plugin is not only easy to install or use but quite easy to manage. The available options are as follows:
- Add new email address to protect or use to digitally sign and make private. Note that adding another email address will require to validating the email address. Ensure that you have access to the email address and it is valid.
- Automatically make a new email message as private.
- Automatically open private post.
- Display digital signature information.
- Warn about invalid digital signatures.
- Keep messages in decrypt state when opened.
- Add proxy server information, if any.
The program also includes an option to check for updates and provides access to Trend Micro Encryption Email Client (TMEEC) website that is located at https://www.myprivatepost.com. This website allows the account users to administer their private post account e.g. settings, password, protected email addresses, security questions and licenses. Note there’s no need to purchase a license when using the program for personal use. You will be able to view the license code when you login to TMEEC website. The validity of the license is one year from the date you entered an email address, protected by the tool.
The program also has the option to managing private post keys using its’ Key Manager:
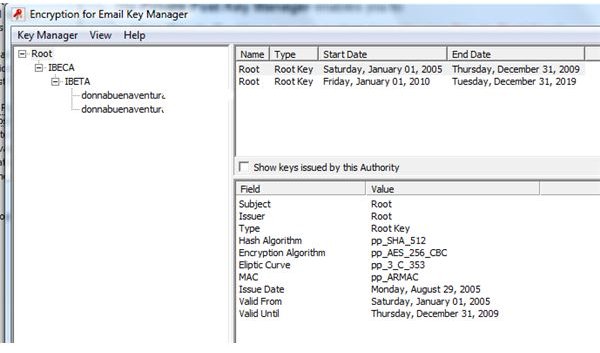
You can use the Key Manager to export, delete and view or register a new email address to be protected by Trend Micro encryption tool.
Conclusion
Trend Micro encryption email worked like a charm. However, we should note that there’s no 100% privacy tool that can prevent anyone or organization in spying on e-mail messages especially if the network or computers is a target by an attacker. We can only hope a high-level of privacy will be attained by using this kind of security software which is better than no prevention at all.
Note that this product involves storing digital certificates, we should be aware of security incidents regarding certificates. An example is the compromised DigiNotar certificate authority that has been revoked by Microsoft (see Microsoft Security Advisory 2607712). To prevent security problems or to becoming victim of spoof websites due to compromised certificates, it is recommended to keep Windows or other operating systems up-to-date.
References
- Product location: http://free.antivirus.com/email-encryption-service/
- Image credit: Screenshots generated by the author.
- Program version: Encryption for Email v5.6.0.1073
- Write-up based on author’s experience.
