What is the technique to removing spyware or adware threats? Find out in this anti-spyware master removal guide.
Spyware, Adware and Rogue Programs
Spyware is a program often installed on a computer without a user’s consent, or prominent notice. It also collects information, such as visited websites, without the user’s knowledge. Some spyware programs are installed by botnets and computer worms in an effort to earn quick profits. An example of such a botnet is called Rbot or Zotob; it exploits security vulnerabilities in Windows. Another example is the Waledac botnet which downloads rogue security software. Cyber-criminals are not bothered at all if the computer worm has been removed from an affected computer because their target is to install other programs that will give them money; e.g. adware, spyware or rogue software.
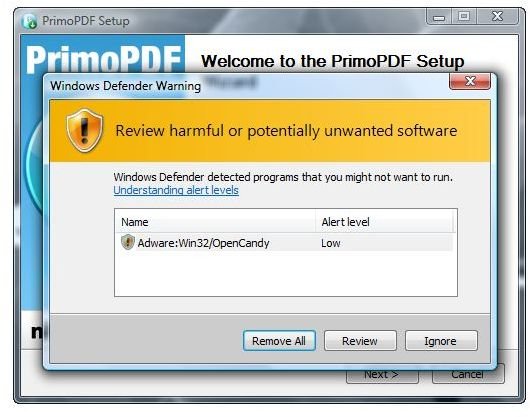
Note that some legitimate software was also found to install spyware or adware on computers; e.g. P2P or download managers software. Sometimes a setup file that is bundled with other software installer can be flagged adware or spyware, if the antivirus or anti-spyware vendors found the installer or the process of installation shows adware and spyware behaviors.
If the computer does not have an anti-spyware program or the virus protection tool has missed in detecting the spyware, adware or rogue programs installed by botnet or another legitimate program, the end-user’s private information is at risk. Most security software will flag an adware with low risk and provide an option to remove from the computer or ignore the detection.
Ignoring the detection on adware or spyware means the antivirus or antispyware will no longer detect any adware with the same threat name that the scanner has on its database, or the particular adware program or files will be excluded from future detections. Note that whatever rating the virus protection tool provides, it is important to note that it is being flagged due to privacy or security concern.
How to Deal with Adware and Spyware
Now that you are aware how adware, spyware or rogue software is distributed by malicious software and legitimate programs, you should know also how to prevent or remove such threats to your private information. Here’s an all-in-one guide for adware and spyware removal - an anti-spyware master removal guide.
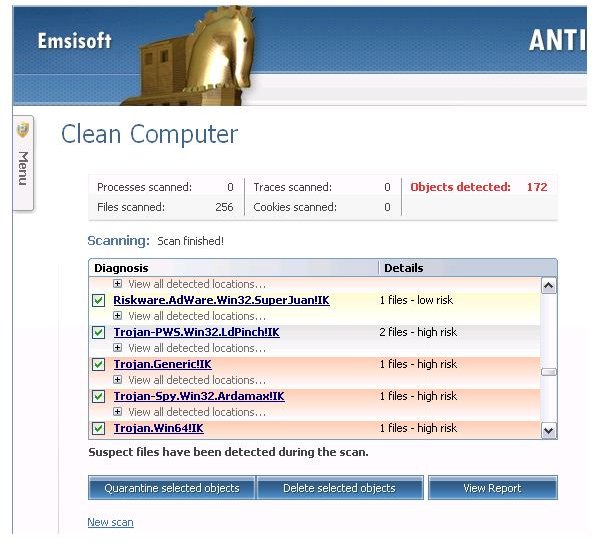
Removing adware and spyware is easily done if the computer has an anti-spyware program, but if the security scanner does not detect spyware or adware on the computer, you should regularly scan the computer using an online scanner or antispyware software by another security vendors. This is because not all antivirus program vendors share the same database or rating system. Some adware programs will be detected by scanner A but not by scanner B or C.
An example is a program that has the OpenCandy installer. Windows Defender found it as adware, but other security vendors do not find any threat in it . It does not mean that the software is malicious; it only means that by using the installer with OpenCandy, some information about you is sent to third-party or advertisers. Most privacy conscious users will opt to not to use such software, thus, Windows Defender detects it since their malware research team has found information is being transferred from the computer to advertisers (aka data collection).
If the computer is already infected with spyware or adware, you need to remove it using the Add or Remove Programs utility in Windows. It’s also important to scan the computer using an anti-spyware program to remove remnants or other files that the spyware program has left behind. Also see the related article: What to Do if Add or Remove Programs Won’t Remove Spyware or Adware?
Spyware Removal Tools
Below are the tools you should consider using to remove spyware or adware:
-
Spybot – Search and Destroy , Malwarebytes, Windows Defender and EmsiSoft Anti-Malware are quite good in detecting spyware and adware because the programs do not focus on malware detection only, but free spyware and adware prevention and detection.
-
WinPatrol – this is a security monitoring program that will alert and display to the end-user the installed programs on your computer. You can use WinPatrol to remove spyware or adware files programs in addition to using an antispyware program.
Advertisement
Advanced users usually use the following tools to remove spyware or adware infection:
-
HijackThis – this program will not scan the computer for spyware, adware or malware but will display the installed programs or files where spyware, adware or malware are known to store their files. It is not recommended to use HijackThis unless you are familiar in using it. Removing safe entries in HijackThis can cause problems on your computer. You should visit forums that offer a HijackThis analysis and then follow the advice of resident analysts; e.g. Bleeping Computer or AUMHA forums.
Advertisement -
Customized or standalone removal tools – advanced users will use a removal tool that only removes specific spyware, adware or malware threats. This method requires positive identification on the spyware or malware threat existing on the machine. Examples of these tools are McAfee Stinger or Malicious Software Removal tool.
-
Antivirus rescue CD – advanced users will also use an antivirus rescue disc to get rid of spyware or malware before Windows will startup. Examples of rescue CD are VIPRE Rescue, AntiVir Rescue System or Dr. Web LiveCD.
Advertisement
Preventing Adware and Spyware Infection
In addition to anti-spyware master removal guide, I thought you should also know how to prevent adware and spyware infections:
-
Do not rely on one security scanner alone. It’s recommended to use one antivirus program that provides detection and prevention of virus, Trojans, rootkit, computer worms, adware and spyware. Using more than one real-time protection against these threats might cause conflict and system instability. Instead it’s best to regularly scan the computer with another scanner and use a security scanner that complements your antivirus software. An example is scanning the computer using online scanner or on-demand scanner.
Advertisement -
If the antivirus program on your computer is compatible to the anti-spyware program, install and use anti-spyware software with real-time protection. Note that the anti-spyware program’s real-time protection should not automatically delete found spyware or adware, to prevent conflict with antivirus program. The anti-spyware program should only halt the installation of spyware or adware and then display the alert to the user for action. Antivirus programs, on the other hand, should automatically handle threats by sending to quarantine, denying access or removing the detected malware.
-
Enable Firewall protection – an advanced firewall provides outgoing traffic monitoring, which means spyware or adware that tries to use the Internet connection to send private information from the computer, download additional files or update the spyware and adware program is prevented, allowing end-users to investigate the particular connection made by software.
Advertisement -
Add an extra layer of protection by using a hosts file that blocks communication to known spyware sites.
-
Keep the computer up-to-date and stop using old versions or unsupported programs that have privacy and security issues.
Advertisement -
Download from trusted sources and scan the downloaded files using VirusTotal single file online scanner, if your antivirus software found no threat but you are unsure if the setup file is safe to use.
References
- Screenshots taken by the author, courtesy of EmsiSoft and Microsoft.
- Information based on author’s experience.