Ever wonder what tools and security measures hackers use to protect their own networks? Read on to find out what software and security practices are relied on by hackers and computer security professionals.
Security and Software Choices
Network security is a tough subject because the topic encompasses more than just the computers and networking devices
involved. Security begins with the user and ends with the machine, meaning that a lot of a hackers protection comes from their knowledge of common attack vectors and vulnerabilities. Implementing a few secure practices, you can help to secure your network from common, physical attacks, leaving only the software end to protect.
On the software side, hackers typically prefer free and open source software because they can review and manipulate the code themselves. The idea behind open source software is that its security comes from its wide distribution, allowing a community of thousands to review and submit security fixes. The other end of this is that it allows programmers to modify specific parts of code and its components, rendering different flavors or distributions of a single source or idea. Essentially, the variety in the system, like with genetics, creates strength and security since a single, automated virus cannot exploit diversity it’s not programmed to attack.
Operating System
Free and open source UNIX-like operating systems are a favorite of hackers. The reason is that they are free, the code is customizable, and the system will run on cheap or outdated hardware. The vast user community and the ability to participate in the development of the software also provides an excellent learning environment for expanding a hacker’s knowledge of how their own machine and others works. In fact, some would argue that a lot of the support for open source stems from its educational benefits.
GNU/Linux is by far the most popular set up used. Distribution popularity and loyalty varies depending on a hacker’s software beliefs, desktop preferences, and their overall approach to their system’s construction. Slackware has always been a favorite because its no-assistance approach allows users to really delve into the system. For this reason, Arch Linux has also been on the rise while Debian, because of its software principles and stability, has remained a long-standing favorite.
After Linux comes the BSDs, with FreeBSD being the most popular. The always-quoted major difference between the two operating systems is in their design philosophy with Linux being more free-for-all and FreeBSD being a centralized, controlled process. This is often argued over and will not be discussed here, but FreeBSD is a very stable and secure operating system. Another, popular for home-made network devices like routers and firewalls, is OpenBSD, a system designed with security in mind from the kernel up.
Firewalls
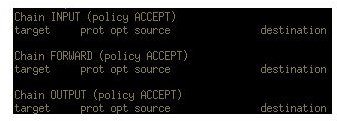
A weak or non-existent firewall is the first step to a remotely compromised system. You will never find a single system administrator or hacker who chooses to run a network with a non-existent firewall. As far as free and open source implementations go, iptables is the most popular firewall out there. Integrated with the Linux kernel, iptables can be customized to do any number of things. Unfortunately, for the novice user, configuring iptables from the command line can seem like an insurmountable mountain. Many users choose to use one of the many graphical interfaces for iptables such as bastille, ferm, or fwbuilder. Under FreeBSD, ipfw (IPFirewall) is the most popular, providing the same flexibility as iptables, but with the FreeBSD mindset and mentality. Firewalls should be the first thing put into place when you bring up a new system. For this reason, many operating systems like Mac OS X and Microsoft Windows have them in place already.
Encryption and Privacy
Most people do not realize how much of their day to day Internet traffic is transmitted in plain text. Every e-mail, dozens of
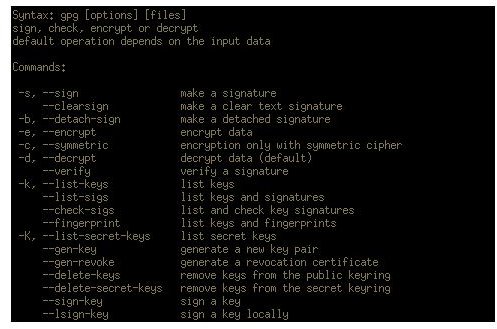
web application passwords, and more are transmitted in a [human readable format](/tools/Bright Hub: Internet Privacy Software for Linux), through hundreds of computers, on the way to the destination server. Hackers realize this and the potential security risks of transmitting things in plain text. An e-mail password here, a database user name there, and a few personal details here can lead to a convincing social engineering, attack, especially against a large company. For this reason, many hackers choose to encrypt their conversations using GnuPG , a free and open source implementation of the OpenPGP protocol. The security provided by GnuPG is government and military-level encryption and has yet to be easily compromised. Maintaining private details is an important step in securing a network. You should always opt for an encrypted option when accessing any service, whether it be a social media site or your favorite IRC server.
Privacy and anonymity as just as important in the hacker’s security arsenal. The first step in compromising a network is finding out where it is. For this reason, many hackers choose to use Virtual Private Networks (VPNs) or SSH tunneling to hide their origins. When connecting to a service where your IP address is publicly displayed, you always run the risk of identifying to any potential attackers your network. To go even a step further, some hackers choose to use The Onion Router (TOR), an anonymizing proxy that bounces every bit of information you transmit and receive off hundreds of computers around the world. Using TOR significantly slows down your connection, but provides a more secure environment for maintaining anonymity.
Strong Passwords
Strong passwords seem simple, but people do not realize how vital they are. A weak password can be easily brute forced, evaporating any semblance of security. Once an attacker is inside a system, with any user account, privilege escalation to administrator status is an easy task. Passwords should always contain special characters, numbers, upper and lower-case letters, and over ten characters. Omitting anything related to your life can reduce the chances of a word list being crafted to speed up an attack on your user name. If you can, using a one-time authentication (OTA) method or a secure token might be a better solution than a password for protecting your system.
Full Disk Encryption
Physical access to a machine is one of the breaking points of security. Using full disk encryption, you can protect against someone imaging your hard drives and using the accrued data to crack your system. Along with communication encryption and anonymity techniques, hard drive encryption is widely used by hackers to secure their systems. Full disk encryption isn’t only important for protecting against physical attacks, but also to protect your private information unless your device is lost or stolen. If you had a collection of passwords and financial data on an unencrypted hard drive that was stolen, you would need to go through the hassle of changing every user account and password before you could trust the accounts again.
Web Protection
As applications have moved to the web, a lot of hackers have chosen the Internet as an attack vector. Cross-Site Scripting
(XSS) vulnerabilities and SQL Injection attacks are used to compromise user data or force a web browser to execute malicious code on the client’s machine. Using a secure web browser with a few modifications can greatly increase your security.
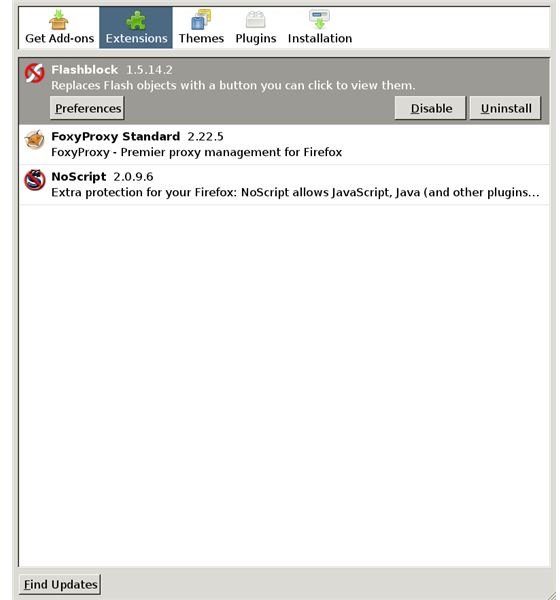
XSS attacks rely on Javascript to execute malicious code. The way they work is that a hacker sends you a specially crafted URL leading to a popular website that does not sanitize (restrict characters) used in their input boxes. The attackers URL uses this un-sanitized input box to call out to another website where their Javascript is stored. This code is crafted to execute in your browser and copy your account details, including passwords, to another server the hacker is using. By disabling Javascript, or installing a plug-in like NoScript for your web browser, you can review and execute only the scripts you deem safe. Additionally, occasionally frequently a vulnerability is released involving Adobe products, the makers of Flash. Using an extension like FlashBlock can not only help reduce the number of obnoxious advertisements you see, but can protect against any compromised Flash-based websites that may try to run malicious code on your machine.
Finally, SSL or secure HTTP should never be trusted on a public network. Using a Man-in-the-Middle (MITM) attack, hackers can transparently decrypt and work as a relay for your secure connection to your bank or private accounts.
Virus Protection
This may seem shocking, especially since viruses are so often talked about in the news, but many hackers do not use virus protection. The reason for this is simple: viruses rely on common, widespread, and well-known vulnerabilities to propagate. By following good security practices and keeping their systems up to date, a hacker should not have to worry about using virus protection unless they run a system being used by more than just themselves. Any vulnerability or virus that a hacker has not heard about or patched their system for is more than likely something a virus scanner will not recognize anyways. However, when running a system with multiple users, ClamAV is the most widely used virus scanner.
Good Security Practices
Finally, a few common security measures can be put in to place to help secure a system. Often times, attackers will use curiosity as a means into a system, so the first two should be rigorously followed.
Users should know never to put any disc or USB drive they found into their machine. The reason for this is that both discs and USB drives can be configured to run and install applications on the system upon insertion. This can be used to install backdoors, keyloggers, or other malicious software.
Never open random e-mail attachments or documents. PDF files especially have been known to contain malicious code that will execute upon opening. The reason for this is how the files are read by the system. Attackers are able to append code to the end of the document that could create a backdoor or other hole in network security.
Test your own system. Free vulnerability scanners for every operating system are available for download or you could use a penetration testing Live distribution like BackTrack Linux . Many of them even have automated functions for discovering and testing holes in your network. OpenVAS, a fork of Nessus, is commonly used and the Metasploit Framework, an exploitation framework, can be used to test your system for popular vulnerabilities.
Lastly, always keep up to date on the security alerts for the software you use. Most developers provide a security vulnerability mailing list or a RSS feed for keeping up to date with their software. Keeping your software up to date, with the latest bug fixes and patches, is one of the best ways to keep yourself secure.
Resources
Metasploit
Screenshots by the author.
Author’s Note: I recognize that there is a movement to differentiate between a cracker and a hacker. I also fully support the idea, but the simple fact is that everyone loops the terms together like people call all martial arts karate or anything with an electric guitar rock music.