Cyberwarfare or cyberwar can affect any business that uses the Internet, which means you need to know how to defend your business and your customers’ information. Find out here about the principles of cyberwar and how your business stands to lose.
What is Cyberwar or Cyberwarfare?
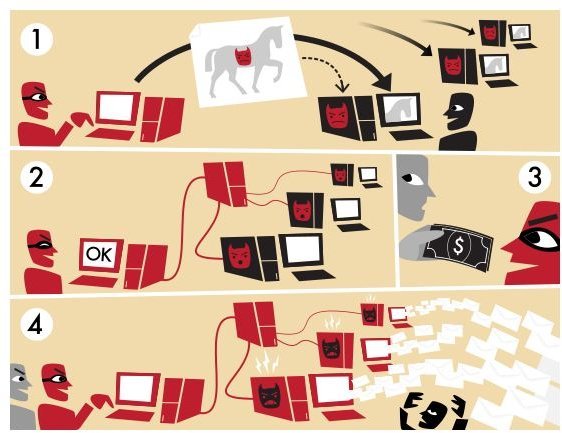
Cyberwar or cyberwarfare is a type of attack or assault via the Internet to a network, organization, or business by spying or retrieving sensitive information. The principles of cyberwar depend on the reason behind the attack, with the intention of distracting, disrupting, or stopping any operations of the target party. Cyberwar often creates chaos that can affect or put to risk your business.
Non-stop spam in a network, a DDoS attack, botnets, spreading malware, or hacking into computers are methods used by attackers.
Image Credit: Wikimedia Commons/Tom-b
Is Your Business at Risk?
When a cyberwar occurs, a business or private company will likely be caught in a crossfire thus putting it at risk or affected. A business is at risk if the platform used by attackers is widely used by consumers and within the company itself.
An example is when an attacker hacks a company server or database that will prompt the customers to change settings as a defense; the business operation is affected if the recommended settings do not meet the requirements to continue with operating the business. We can look at the recent incident in which a corporate giant advised its customers not to change the default password that could affect operations in a business. The company operated a widely used program to acquire and analyze data, which was targeted by a malicious program. The attacker created a program to create chaos by attacking the software used to control power grids, factories, and water-processing plants.
In the said incident, the attacker successfully exploited a security vulnerability in a Microsoft Windows operating system, which we all recognize as a widely used platform. Microsoft and the company’s security vendors worked hard and hand in hand to prevent and stop the problem. Unfortunately, one of the company’s clients was affected.
You might wonder why the above is called cyberwar. Here’s why:
A security researcher has found vulnerability in Windows Shell , a component in Microsoft Windows operating systems. The details of the vulnerability including the proof of concept (PoC) was publicly published. The said PoC has been exploited by malware creators and hackers by creating a program to attack. The researcher and the affected vendor have a different principle or belief on how a software company, in this example, should act when a vulnerability is discovered and reported. The impact on business or consumers is seemingly not taken into consideration.
Clearly, such incidents are evidence that when a cyberwar occurs, it is not only consumers who are at risk but the business as well.
Resource: The Wall Street Journal at https://online.wsj.com/article/SB10001424052748703954804575381372165249074.html
How to Protect Your Business When Cyberwar Occurs
Network- or Internet-based attacks are so sophisticated that a protection software is never enough. To help protect your business when cyberwar occurs, you should have done three important steps:
- Use prevention tools - Most security software or hardware vendors provide prevention programs that monitor the computers for any malicious activity. An intrusion detection System (IDS) for your business is quite important to use.
- Detection method - Tools are only created to prevent any possible security and privacy issue in a business but it is not a complete defense if the company or business will not use any detection program to regularly check that settings or policies are secure or configured properly.
- Review controls and correct them quickly- A regular review on policies and applying modifications or correcting settings is also important. You don’t want a flaw in any policy of your business that can cause chaos later on.
Any software that you use in business should be fixed by applying vulnerability and bug fixes or a work-around when available. Keeping your staff informed about security and privacy concerns is a must. It will help reduce any risk, if your employees are aware of the security or privacy issue. If your business has sensitive data, avoiding the services that are known to leak your privacy or sensitive data is a good decision as well as using only a secure service to communicate with your clients or potential customers.
Final Words
Your data and customers’ data are important to be secured. A default password or settings should not be used in any way. If the provider suggests using the default password, demand that they adjust the requirement or use another service that will provide proper service without compromising the security and privacy of your business when cyberwar or any network threats occur.