Black hat hackers seem to have innumerable ways to compromise your network once connected–connected in any way. Further, users will connect anything you allow to snatch an IP address. So, security control all organizations should begin considering is network access control.
What is Network Access Control?
A very simple definition of Network Access Control (NAC) is the implementation of controls which allow systems to connect to a network only when they meet certain business or security rules. Organizations implement NAC solutions to prevent unauthorized or weakly protected systems from accessing critical information resources.
Examples of business or security rules enforced by NAC include:
- An approved, up-to-date anti-malware solution is running;
- A client-side firewall is running;
- The system meets an acceptable patch level; and
- The system is owned/managed by the host organization.
The final bullet assumes that privately-owned end-user devices are not allowed access.
NAC is not just for remote access. It also ensures no machine can connect locally unless it meets specific security criteria. This is not only an important control for preventing black hats from gaining access from available physical or wireless connections. It also stops mobile users from connecting a company-owned laptop that hasn’t been updated in weeks–and may be compromised with malware, or worse.
How Does Network Access Control Work?
NAC vendors take different approaches. However, the basic characteristics remain the same. It is these common attributes that you should consider when implementing a solution.
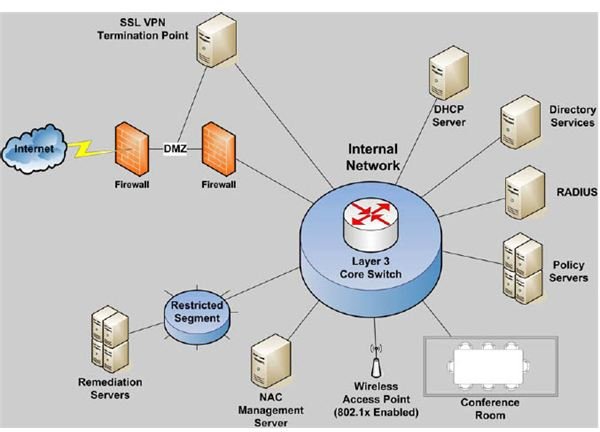
Please refer to Figure 1. This sample network is segmented into a primary and a restricted segment. Attached to the restricted segment are remediation servers, which update authorized systems that do not comply with business security rules. Policy servers and a NAC Management Server are attached to the main network segment. Network administrators use these devices to manage and apply NAC security rules.
Although organizations can use NAC to manage internal connections, let’s use Figure 1 to step through a remote access example.
- A remote device initiates a connection to the SSL VPN Termination Point.
- The user enters credentials which are passed to the RADIUS server.
- If user authentication is successful, a host checker is pushed to the client. The host checker uses information in the Policy Servers to ensure certain criteria are met. Not all host checkers are created equal. Some check only at login, allowing users to stop firewalls or make other configuration changes once connected. Others check at a user-defined frequency. Anytime the client is found to be out of compliance, it is either disconnected or proceeds to Step 5.
- If the client is in compliance, it is granted access according to rules set within the SSL VPN device.
- If the client is not in compliance, it is allowed to connect. However, access is confined to the restricted VLAN. Depending on the vendor implementation, the host checker may automatically request updates to bring the system into compliance. Once in compliance, the client is allowed normal access to the primary segment. If automatic remediation is not provided, this process may require user or Help Desk intervention.
The Final Word
Network access control technology has just recently made it to my list of viable security control solutions. Even so, not all vendors see NAC in the same way. To get a better idea about the different methods offered, visit the following sites: