Many organizations with a strong information security program often inadvertently leave one or two gaps in their defenses. In this article, we examine five common misses in addressing network and database security issues.
The Big Five
Most organizations finally get it; security is important. However, in the rush to put controls in place to meet regulatory constraints or customer/investor expectations, IT teams often miss one or two fundamentals. Based on my experience, the top five network and database security issues commonly found in networks include:
- Firewalls installed in a default open state
- Network access devices not physically secured
- Servers in satellite offices not physically secured
- Database servers not segregated from common-access network segments
- Lack of log management
These misses are not from negligence. They usually result from not conducting effective system risk assessments or gap analysis .
Open Firewalls
When network engineers install a firewall, they typically have a choice. Do they install it allowing all packets to pass by default, or do they close all ports and open only what is necessary? Deciding to do the former ensures nothing breaks on the network. However, it is poor security practice.
The venerable firewall is still the most commonly used device to protect the network perimeter and critical network segments. When properly configured, it should allow only traffic absolutely necessary for business operation. The best way, the only sure way, to reach this goal is to install the firewall to block everything, and then open those ports and services required by the business.
This isn’t always an easy sell to management or to the engineers who have to work through the challenges associated with this approach. Often, skirmishes break out within IT about whether to put in the extra effort. However, failing to start with a locked down configuration results in continuously checking to see if something you have open is considered high risk. And high risk ports and services are always changing.
Weak Physical Security
The second and third gaps are related, and result from non-existent or weak physical barriers between network devices and unauthorized physical access to switches, routers, servers, and end-user devices.
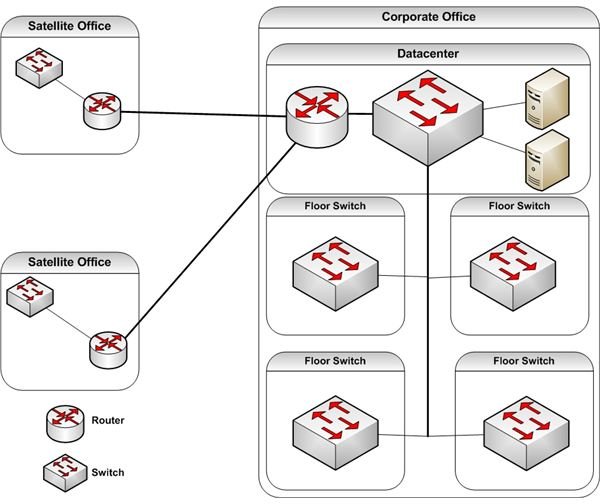
Figure 1 shows common switch and router locations. Typically, the data center is secure with strict access controls in place. However, many organizations fail to pay attention to the physical security of floor and satellite office network devices. It doesn’t matter where an attacker gains access to your network. Any opportunity for physical access is a great opportunity to lose control of some or all of your network.
An example of poor physical security is a company I once did some work for. The organization had several remote locations connected to the main office via IP VPN connections (over the Internet). They also had several floors at their corporate headquarters.
The company’s datacenter was secured by a centralized electronic badge system. The floor on which the datacenter door was located was also controlled by the same badge access system. This was a good start. However, physical access controls began to fall apart as I began looking at the other locations.
Access to floors was via the badge system. The floor switches were behind locked doors in rooms designed specifically for housing floor access equipment. However, I found one of the doors propped open. When I asked about this, I was told the doors to the floor switch rooms required a key for access. Once an engineer gained access to work on a project or problem, he or she left the door ajar so access was easy, and one of the other engineers could use the one and only key.
Although access to the floor was controlled, IT was counting on non-IT staff to make sure no unauthorized personnel piggyback to gain access. They also relied on the honesty of every employee at the corporate office. This was not a good physical security plan.
At the satellite offices, switches and routers were often placed in mop closets or other unlocked areas. I also found a server in an activities room. Apparently, the office manager found the server too noisy and had it moved from the business office by the maintenance staff.
Physical security should not be an afterthought. Rather, security analysts and auditors should include it in the same assessments they use to ensure adequate technical and administrative controls. No one should have physical access to devices unless required by identified business requirements.
No Datacenter Segmentation
Securing your network infrastructure, and the data passing through or stored there, requires layered controls. No single layer of defense is enough to stop or detect a motivated attacker. One layer an organization can use to protect its database servers is network segmentation.
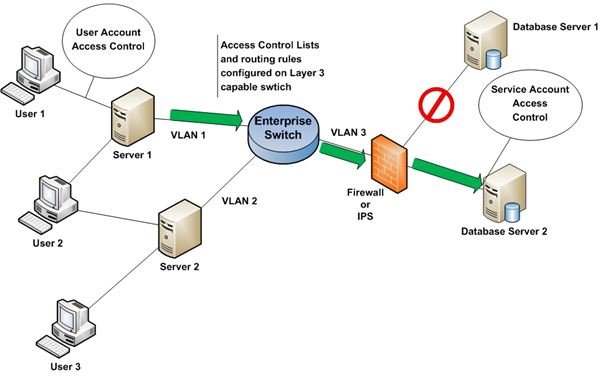
Figure 2 depicts one method of isolating database servers with segmentation. The two database servers are on a single, restricted VLAN (Virtual Private Network ). Access to the restricted VLAN is controlled, in this case, by a firewall. The firewall ensures that unwanted traffic does not pass. An IPS (Intrusion Prevention System) can replace the firewall or act in concert with it.
The firewall approves access to database servers only for explicitly allowed application servers. In this example, Servers 1 and 2 are application servers.
Let’s step through how this works. User 1 connects to Server 1 using her user ID and password. After loading the required application, she requests customer data. The application sends this request to Database Server 2 over a pre-established session. The session between Server 1 and Database Server 2 used a service account for authentication. At no time does User 1 gain direct access to VLAN 3 or to the servers located there.
Note that Server 1 is not allowed to connect to Database Server 1. This is prevented, in our example, by a rule which does not allow packets from Server 1 addressed to Database Server 1 to pass through the firewall,.
There are multiple ways to segment a network. If you don’t like this one, design your own. However, don’t ignore the value of placing your data behind strong layers of security.
No Log Management
Layering effective security controls is a great start. However, assuming everything is working as expected is a bad idea. Dealing with errors in configuration, unseen gaps, and emerging threats requires constant vigilance. The most fundamental approach is log management.
Log management is the process of collecting logs from all relevant devices, correlating events, and alerting or blocking unwanted or suspicious network/system behavior.
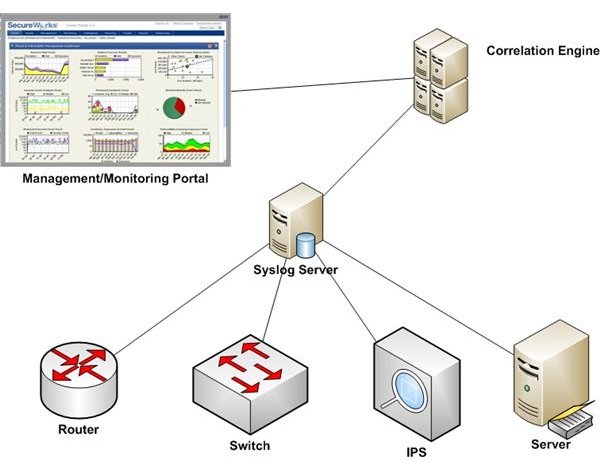
Figure 3 is a conceptual model of a typical log management solution. In this example, I use the Syslog standard to aggregate logs from key systems across the network. A correlation engine is then used to look at relationships between events. This event correlation step allows a view into collections of events that may point to malicious or other unwanted network behavior. This is much better than looking at individual logs in isolation.
A portal is used to report the results of log correlation and, if necessary, send alerts to key personnel. The portal shown here is from SecureWorks .
The Final Word
The five common network and database security issues described here are not the only gaps you may find in your network. Constant vigilance and effective risk assessments are necessary to identify old and new holes in your security program. Remember, security isn’t a project with a completion date. It is a continuous process, one in which your job is never done.