PBX Hacking, Security, and Firewalls
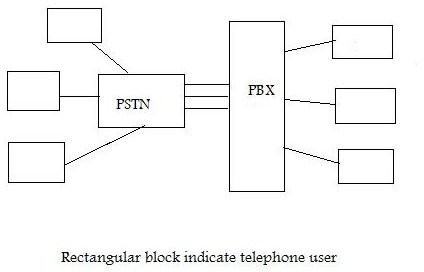
PBX stands for “private branch exchange.” Each PBX is owned by a private company and is dedicated to sharing the resources of dedicated telephone lines leased from a central telephone company. The company does not need to lease a dedicated line for each employee. When an employee wants to talk with another employee, he uses the resources of the company’s own internal telephone system. When the employee needs to call outside, he starts by dialing a specified digit (usually a 0 or 9) to tell the system to connect using the phone company’s lines.
PBX Hacking
How can a hacker damage a PBX? There are several techniques that can be used, but the hacker has to start by finding entry to the system. They gain access to a PBX is order to steal sensitive information, alter data, and simply for unauthorized use.
- Stealing information: A hacker with access to the PBX can listen to the telephone conversations. This could be either intelligently or accidentally.
- Altering data: Hackers can gain access to the network in order to alter data regarding billing or to delete stored data (conversations or messages).
- Unauthorized access: The intruder can simply gain access to the network to misuse system resources for kicks or for the lulz (internet jargon meaning “for the laughs”).
PBX Firewalls
Imagine a restricted area with law enforcement agencies keeping the area isolated using some physical barrier. Only legally permitted, authorized people can go inside the area. In networks we have the same policy. The network is kept isolated from the outside world using a barrier called a firewall. This can be a piece of software, an item of hardware, or a combination of both. The purpose of the firewall is to check all incoming and outgoing data and prevent the entrance of hackers. It blocks any data that does not meet the criteria specified by the security protocol being used for the firewall. There are several ways to implement a firewall.
- Packet filter
- Application gateway
- Circuit level gateway
- Proxy server
PBX Security
Authorized users gain entry to the network through a process called authentication. This involves the user sending a username and password to a network database. The network gives the go-ahead signal after authentication.
After entering the secure network, a user can interact with other users already inside the network. There they can send messages to each other in a secure way. When we talk about message security we are concerned about message:
- Privacy
- Authentication
- Integrity
- Nonrepudiation
Images
PBX Privacy
In a secure network, users communicate with each other, but they are still concerned about their confidentiality. Both the parties need to make sure that a third party is not listening to them. This is the privacy concept.
The message needs to be interpreted in such way that it becomes meaningful for the transmitter and the receiver. To all others, it must appear to be garbage, or meaningless. To achieve privacy, we use a technique called encryption. The message must be encrypted before it is transmitted by the sender. We have two techniques to achieve message privacy.
- Privacy with symmetric key encryption
- Privacy with public key encryption.
In symmetric key encryption we have one key used for both encryption and decryption. Imagine a door that can lock and open with a single key, so both parties share one key. This is very common technique to achieve privacy.
Privacy can also be achieved using public key encryption. Here we have two keys: a private key and a public key. The receiver uses the private key, while the public key is given to public.
Message Authentication
Let’s say that Smith sends a message to Alek. Both are now sure that their conversation is not intercepted by a third person, as their message is encrypted. However, Alek is still doubtful. He needs to make sure that the message he got is actually from Bob (or else somebody has sent him a fake message.) Alek needs to authenticate the source of his message.
Integrity
Alek also needs to make sure that the message he got remained unchanged during transmission (by either accidental or malicious means). Integrity plays a vital role in secure communications. For example, integrity is crucial when it comes to online banking systems. It would be a system failure if a request for transferring $1,000 changed to $100,000. We use a technique called digital signatures to provide message integrity.
Nonrepudiation
Bob sends a message to Alek. Now Alek must be able to prove that the message he got is from Bob. This is called nonrepudiation. For another example, consider a customer requesting that her bank manager transfer money from one account to the other. The bank manager must be able to prove that the customer did request the transaction in the event she later tries to deny it.
User Authentication
So far we’ve discussed various methods for message authentication. Now let’s look at user authentication, which is slightly different. Here we have two techniques.
First technique: Catharine wants to reply to a dinner invitation from Bob, so she sends her username and password with an encrypted message using a symmetric key. Now one would think this must a safe technique, and it is, to some extent. However, Lori can damage it, although she can’t read it. She can intercept both the message and the authentication, store them, and resend them to Bob. This is called a reply attack.
Second technique: To diminish the possibility of a reply attack, we use nounce, which is simply a large number used to prove authenticity. Catherine sends a number to challenge Bob to make sure that it is Bob, and someone, like Lori, is not replying to him.
Summary - Main Points
A PBX is a privately owned network that connects users inside a company or building, while giving access to the outside world through a dedicated shared line leased from the central telephone office. A hacker can gain access to a PBX and can alter, destroy, or steal sensitive information like stored messages and voice conversations recorded on the network server. A firewall acts as barrier in the path of a hacker to prevent entry to the PBX network. This firewall may be a piece of software or hardware or combination of both. It checks incoming and outgoing traffic based upon a special protocol called the security protocol. Network users communicating with each other will expect that another person is not intercepting their communications. PBX networks need to ensure privacy, integrity, authentication, and nonrepudiation.